Enterprise security is a high-stakes balancing act. As organizations grow, their attack surface expands, creating a complex web of endpoints, cloud services, applications, and networks that must be protected. A single breach can lead to devastating financial losses, regulatory penalties, and a permanent loss of customer trust.
The challenge for security leaders is to build a resilient defense against sophisticated cyber threats without stifling the innovation that drives the business forward.
Choosing the right security tools is fundamental to this effort, but the market is a labyrinth of platforms, suites, and point solutions. Many traditional enterprise tools are powerful but also notoriously complex, expensive, and slow to adapt.
This guide is designed to bring clarity to your decision-making. We’ll start with an overview of the top enterprise security platforms for 2026 (unranked, alphabetical), breaking down their capabilities, ideal use cases, and limitations.
After that, we will break down the best enterprise security tools for 7 specific use cases like software security, multifactor authentication, data loss protection, and more. Skip to the relevant use case below if you’d like.
- Enterprise Software Security
- Enterprise AI infrastructure security
- Enterprise Extended detection and response (XDR)
- Enterprise Cloud Native Application Protection Platform (CNAPP)
- Enterprise Multifactor authentication & Identity and access management (IAM)
- Enterprise Incident management
- Enterprise Backup and disaster recovery
How We Chose the Top Enterprise Security Tools
We evaluated each platform based on criteria essential for modern enterprise security:
- Integration and Breadth: How well does the platform unify different security functions (e.g., endpoint, cloud, application) into a cohesive whole?
- Effectiveness and Automation: How effective is the tool at detecting and responding to threats, and how much does it rely on automation to reduce manual effort?
- Scalability and Management: Can the platform scale to meet the demands of a large, distributed enterprise, and how complex is it to manage?
- Developer and Cloud-Native Focus: How well does the tool address the security needs of modern, cloud-native application development?
- Total Cost of Ownership (TCO): Beyond licensing, what is the overall cost in terms of personnel, training, and operational overhead?
The 9 Best Enterprise Security Tools
Here is our analysis of the leading platforms designed to secure the modern enterprise.
The Top 7 Enterprise Security Platforms in 2026
1. Aikido Security

Aikido Security is a modern, developer-first software security platform that provides category leading products in SAST, DAST, SCA, infrastructure security, AI penetration testing that integrate with any infrastructure. Its security products are used by 50,000 organizations, including Revolut, The Premier League and Serko.
While many enterprise tools focus on protecting the perimeter and endpoints, Aikido secures the applications that run the business from the inside out.
You can also use Aikido as a complete enterprise security platform that covers everything from code to cloud and even runtime security. The goal: give developers and security teams a single pane of glass for security without the usual noise and friction.
Aikido’s secret sauce is automation and AI. Aikido uses AI to cut out ~90% of noise, so you’re not flooded with false positives and issue deduplication. It even offers one click bulk fixes: for example, it can create “ready to merge pull requests” that address multiple related alerts at once, saving time and manual work.
While Aikido is not a legacy platform, it is heavily backed with $60m funding announced in 2026, enabling it to continue coming out on top of evaluations against legacy security vendors.
Key Features & Strengths:
- Category leading products: Aikido offers best-in-class products for any part of your enterprise IT estate. Code scanning, IaC scanning, API scanning, etc. And compared with other platforms, Aikido has shown better reachability analysis and auto remediations.
- Intelligent AI Triaging: Automatically prioritizes vulnerabilities that are actually reachable and exploitable, allowing security and development teams to focus on fixing what matters and ignore the 90% of alerts that are just noise.
- AI-Powered Autofixes: Delivers automated code suggestions to resolve vulnerabilities directly within developer pull requests, dramatically speeding up remediation times and reducing the burden on security teams.
- Seamless CI/CD Integration: Natively integrates with GitHub, GitLab, and other enterprise tools in minutes, embedding security into the pipeline without friction or complex configuration.
- Cloud or on-prem deployment: Use Aikido SaaS or self-host it if you need to keep data in-house. It also provides compliance reports (SOC2, ISO) out-of-the-box for the audit folks.
- Enterprise-Grade Predictable Pricing: Built to handle the demands of large organizations with robust performance, while its straightforward, flat-rate pricing model eliminates the complex, per-seat licensing common with other enterprise tools. Learn more on the Aikido pricing page.
Ideal Use Cases / Target Users:
Aikido is the best overall solution for modern enterprises that want to shift security left and build a strong, developer-led security culture. It is perfectly suited for security leaders who need a scalable and efficient platform to secure their applications and cloud environments, and for development teams who want to own security without being slowed down.
Pros:
- Exceptionally easy to set up and drastically reduces alert fatigue
- Consolidates the functionality of multiple security toolsBroad language support
- Robust compliance features
- Transparent pricing
- Comprehensive Software Bill of Materials (SBOM)
- AI-powered filtering
- Cross-platform support
- Developer-friendly UX
Pricing / Licensing:
Aikido offers a free-forever tier for getting started. Paid plans use a simple, flat-rate pricing model that provides predictable costs as the organization scales.
Recommendation Summary:
Aikido Security is the top choice for enterprises looking for an enterprise security tool with seamless developer experience and enterprise governance in mind.
From its On-prem vulnerability scanners to Monorepo splitting features for improved security issues management, Aikido enables enterprises to not just meet current security requirements, but innovate confidently for the future.
Explore how Aikido can help unify security, eliminate noise, and empower developers to build secure software at enterprise scale.
2. Check Point Infinity
Check Point Infinity is a consolidated cybersecurity architecture that spans networks, cloud, mobile, endpoints, and IoT. It aims to provide a single, unified platform for threat prevention and security management across an organization's entire IT infrastructure. For organizations assessing the strengths of single-vendor versus best-of-breed security approaches, our overview on OWASP Top 10 2025 changes for developers is a helpful guide to understanding the latest in modern threat landscapes.
Key Features & Strengths:
- Consolidated Architecture: Integrates a wide range of security products under a single management umbrella, from next-generation firewalls (Quantum) to cloud security (CloudGuard) and endpoint protection (Harmony).
- ThreatCloud AI: Leverages a global threat intelligence network to share indicators of compromise across all products, enabling real-time threat prevention.
- Broad Security Coverage: Offers one of the most extensive portfolios on the market, aiming to be a one-stop shop for an enterprise's security needs. For those considering more cloud-native or container-focused options, see our analysis of Docker container security vulnerabilities.
- Unified Management: Provides a central console for managing policies and viewing security events across the entire infrastructure.
Ideal Use Cases / Target Users:
Check Point Infinity is designed for large enterprises, particularly those with complex, hybrid environments that span on-premise data centers and multiple clouds. It's best for security teams looking for a single-vendor solution to simplify management. If you're also managing open-source security tools or hybrid environments, you may want to review our roundup of top open-source dependency scanners to complement existing solutions.
Pros and Cons:
- Pros: Extremely broad product portfolio, strong threat intelligence, and unified management can reduce complexity.
- Cons: Can lead to vendor lock-in. The platform can be complex to navigate, and integrating all the different pieces may not be as seamless as advertised.
Pricing / Licensing:
Check Point Infinity is offered as an enterprise-wide subscription license, with pricing that can be complex and depends on the specific products and scale required.
Recommendation Summary:
For enterprises committed to a single-vendor strategy for broad security coverage, Check Point Infinity offers a powerful and comprehensive, albeit complex, solution.
3. CrowdStrike Falcon
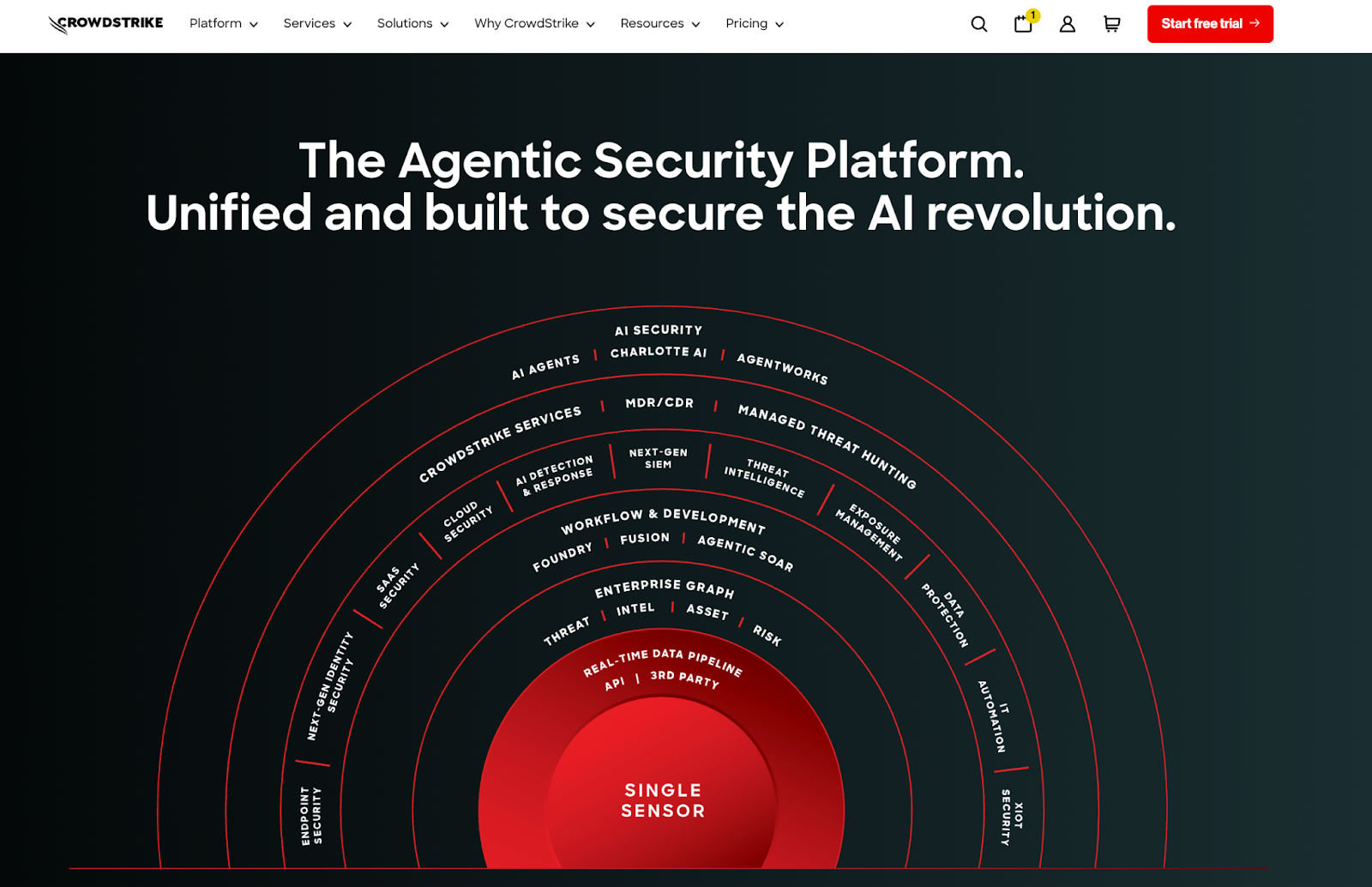
CrowdStrike Falcon is a cloud-native platform that has redefined endpoint security. It provides a suite of services built around its Endpoint Detection and Response (EDR) capabilities, using a single, lightweight agent to deliver next-generation antivirus, threat intelligence, and managed threat hunting.
Key Features & Strengths:
- Cloud-Native Architecture: Built from the ground up in the cloud, allowing for massive scalability and real-time analysis without the need for on-premise hardware.
- Single Lightweight Agent: A single agent provides a wide range of security functions, from antivirus to EDR and vulnerability management, simplifying deployment and management.
- Threat Graph: Uses powerful AI and graph database technology to analyze trillions of events per week, identifying and stopping sophisticated attacks in real-time.
- Managed Threat Hunting (Falcon OverWatch): Offers an elite team of security experts who proactively hunt for threats in your environment 24/7.
- Alignment with AI Trends: As organizations adopt more AI-driven security techniques—like those discussed in Aikido's overview of AI-powered pentesting—Falcon's use of machine learning and advanced analytics puts it at the forefront of modern EDR solutions.
Ideal Use Cases / Target Users:
CrowdStrike is ideal for enterprises of all sizes that are prioritizing endpoint security. It is highly valued by security operations centers (SOCs) for its powerful threat detection capabilities and by IT teams for its ease of deployment.
Pros and Cons:
- Pros: Market-leading EDR capabilities, easy to deploy and manage, and the OverWatch service provides immense value.
- Cons: Primarily focused on endpoint and identity security. While it has expanded into cloud security, it is not an all-in-one platform for application or network security. Can be expensive.
- Integration with Broader Security Strategies: For organizations weighing multiple security tools and approaches, comparing endpoint security with other areas like supply chain or SCA management (see Snyk vs. Trivy comparison) can help create a comprehensive stack.
Pricing / Licensing:
CrowdStrike Falcon is a subscription-based service with various tiers and add-on modules.
Recommendation Summary:
CrowdStrike Falcon is the gold standard for endpoint protection. It is an essential tool for any enterprise looking to defend against modern, sophisticated attacks targeting user devices and servers. For further insight into how endpoint security integrates with broader security programs, check out articles like Top AI Pentesting Tools on the Aikido blog.
4. SentinelOne Singularity
SentinelOne Singularity is an autonomous security platform that combines EDR, Endpoint Protection Platform (EPP), and other security capabilities into a single solution. Its key differentiator is its use of AI to autonomously detect, prevent, and respond to threats in real-time on the device itself, even if it's not connected to the cloud.
Key Features & Strengths:
- Autonomous AI: The agent can independently identify and neutralize threats on the endpoint without needing to stream data to the cloud first, enabling faster response times.
- Cross-Surface Visibility (XDR): The Singularity platform extends beyond the endpoint to ingest data from cloud, network, and identity sources, providing extended detection and response (XDR) capabilities.
- Automated Response and Remediation: Can automatically kill malicious processes, quarantine files, and even roll back an endpoint to its pre-attack state.
- Single-Agent Architecture: Like CrowdStrike, it uses a single agent to simplify deployment and management across the enterprise.
Ideal Use Cases / Target Users:
SentinelOne is great for enterprises looking for a highly automated endpoint security solution that can reduce the workload on their security teams. Its autonomous nature makes it particularly attractive to organizations with limited SOC resources.
Pros and Cons:
- Pros: Powerful on-agent AI provides extremely fast response times. Strong automation features can reduce manual effort.
- Cons: The high degree of automation can sometimes make security analysts feel like they have less control. It is also a premium-priced solution.
Pricing / Licensing:
SentinelOne Singularity is a commercial subscription service with pricing based on the number of endpoints and the feature set.
Recommendation Summary:
SentinelOne is a top competitor to CrowdStrike in the endpoint security space, offering a compelling vision for an AI-driven, autonomous security platform.
5. Fortinet Security Fabric
The Fortinet Security Fabric is an integrated cybersecurity platform that provides broad, automated protection across the entire attack surface. Rooted in its powerful FortiGate firewalls, the Fabric is designed to interconnect different security solutions into a single, cooperative mesh.
Key Features & Strengths:
- Broad, Integrated Portfolio: Offers a massive range of products, including firewalls, secure SD-WAN, email security, endpoint protection, and SIEM, all designed to work together.
- Security-Driven Networking: Tightly integrates network infrastructure and security, a concept that is central to its SD-WAN and SASE (Secure Access Service Edge) offerings.
- Fabric Management Center: Provides centralized management, analytics, and automated response across the entire suite of Fortinet products.
- Strong Price-Performance: Fortinet is often recognized for providing strong security performance at a competitive price point compared to some other enterprise vendors.
Ideal Use Cases / Target Users:
The Fortinet Security Fabric is ideal for organizations that want to build their security architecture around a strong network security foundation. It is particularly popular in distributed enterprises that need to secure many branch offices.
Pros and Cons:
- Pros: Very broad and well-integrated product portfolio. Strong performance in its core networking products. Often more cost-effective than competitors.
- Cons: Can encourage vendor lock-in. While broad, some of the non-core products may not be as mature as best-of-breed solutions.
Pricing / Licensing:
Fortinet products are sold as perpetual hardware or virtual appliances with subscription services for security updates and support.
Recommendation Summary:
For enterprises that prioritize network security and want a tightly integrated, single-vendor architecture, the Fortinet Security Fabric is a compelling and cost-effective choice.
6. Palo Alto Networks Platform
Palo Alto Networks offers a comprehensive security platform that is a leader across multiple domains: network security, cloud security, and security operations. Its platform is built on preventing successful cyberattacks through a combination of powerful firewalls, cloud-native protection, and advanced threat detection.
Key Features & Strengths:
- Next-Generation Firewalls: The company's hardware and virtual firewalls are considered market leaders, providing deep visibility and granular control over network traffic.
- Prisma Cloud: A comprehensive Cloud-Native Application Protection Platform (CNAPP) that provides security from code to cloud.
- Cortex XDR: An extended detection and response platform that ingests data from endpoints, networks, and clouds to provide advanced threat detection and response.
- Strong Integration: The different components of the platform are well-integrated to share threat intelligence and provide a unified defense.
Ideal Use Cases / Target Users:
Palo Alto Networks is geared toward large enterprises that are willing to invest in a premium, best-of-breed security platform. It's for organizations that need top-tier security across network, cloud, and endpoint environments.
Pros and Cons:
- Pros: Market-leading products in multiple categories. Strong integration across its platform. Excellent reputation for security efficacy.
- Cons: It is one of the most expensive enterprise security solution on the market. The platform can be complex to deploy and manage, requiring significant expertise.
Pricing / Licensing:
Palo Alto Networks uses a mix of perpetual hardware licenses and subscription services. It is a premium-priced enterprise solution.
Recommendation Summary:
For enterprises where security is a top priority and budget is a secondary concern, the Palo Alto Networks platform offers an unparalleled suite of best-in-class security tools.
7. Rapid7 Insight Platform
The Rapid7 Insight Platform is a cloud-based suite of tools designed to provide visibility, analytics, and automation across an organization's security program. It combines vulnerability management (InsightVM), SIEM/XDR (InsightIDR), and application security (InsightAppSec) into a single platform.
Key Features & Strengths:
- Strong Vulnerability Management: InsightVM is a market leader in vulnerability management, providing excellent scanning, prioritization, and reporting capabilities.
- User-Friendly SIEM/XDR: InsightIDR is known for being an easy-to-use cloud SIEM that combines log management, user behavior analytics, and endpoint detection.
- Integrated Platform: The different modules on the Insight platform are well-integrated, allowing for cross-product workflows (e.g., finding a vulnerability in InsightVM and investigating related alerts in InsightIDR).
- Focus on Actionability: Rapid7 focuses on providing actionable insights that help security teams prioritize their work and respond to threats faster.
Ideal Use Cases / Target Users:
The Rapid7 Insight Platform is ideal for mid-to-large enterprises that need a strong, integrated platform for their security operations. It's particularly well-suited for teams that need powerful vulnerability management and a user-friendly SIEM.
Pros and Cons:
- Pros: Strong in its core areas of vulnerability management and SIEM. The platform is generally easy to use and provides actionable data.
- Cons: The application security and cloud security modules are not as mature or comprehensive as some of the other platforms on this list.
Pricing / Licensing:
The Rapid7 Insight Platform is a subscription-based service with pricing based on the number of assets, users, and data volume.
Recommendation Summary:
Rapid7 offers a powerful and user-friendly platform for managing security operations, making it a great choice for teams that want to mature their vulnerability management and threat detection programs.
Enterprise Software Security
Software security tools help organizations identify, prioritize, and remediate vulnerabilities across internally developed code, open-source dependencies, and modern application environments. For enterprises, software security is now a foundational control for reducing breach risk without slowing delivery. Why?
Why Software Security is Essential
Unlike decades ago, enterprise software now depends heavily on open source and third-party APIs, coupled with increased development velocity, every line of code introduces potential risk.
A good enterprise software security tool:
- Identifies vulnerabilities early
- Prioritizes real risk, and
- Integrates into developer workflows without slowing delivery
Top 3 Software Security Products
- Aikido Security: From its API-first approach that streamlines integrations, comprehensive compliance reporting, to its innovative AI pentesting solution that performs human-level tests at machine speed. Aikido Security is the best software security tool on the market today. Unlike legacy enterprise tools that often feel heavy and siloed, Aikido focuses on developer-friendly workflows and zero-noise results. That means fewer false positives, faster remediation, and tighter integration with tools enterprises already use.
- Wiz: Wiz often calls itself an application security tool, however it wasn’t built with developers in mind. DevOps teams can use Wiz to catch misconfigurations, but when it comes to code and pipeline security, it falls short. Although its recently introduced “Wiz Code” module adds some Infrastructure-as-Code (IaC) scanning, it falls short when compared to dedicated SAST, SCA, or CI/CD pipeline security tools.
- Checkmarx: Many large companies use Checkmarx for its depth and track record. It’s heavy but battle-tested. Checkmarx’s reporting, auditing features, and the ability to customize rules cater well to enterprise governance needs. However many teams find Checkmarx complex, costly, and prone to false positives. They are looking for alternatives. Also in today’s fast moving development landscape, this leads to tech debt with teams ignoring findings.
Additional Software Security Resources
- Software security (DevSecOps) tools explained by Aikido
- Reducing cybersecurity debt with AI Autotriage
- Open source threat intelligence database
- Top 23 DevSecOps Tools in 2026
Enterprise AI Infrastructure Security
AI has changed our world. AI is here to stay. These two sentences are true, and every forward thinking enterprise is building any AI product or feature.
Why AI Infrastructure Security is Essential
In the rush to implement AI and gain market share, many enterprises are skipping security. The sad thing is AI systems introduce entirely new attack surfaces. From training data poisoning and model theft to prompt injection and unauthorized inference access.
Unlike traditional applications, AI infrastructure blends data pipelines, GPUs, AI agents, cloud services, APIs, and models that often evolve continuously.
Top 3 AI Infrastructure Security Products
- HiddenLayer: Provides runtime threat detection for AI systems, helping detect model abuse, adversarial attacks, and anomalous inference behavior. Think running AI models and AI agents in production environments.
- Protect AI (A Palo Alto Company): Focuses on securing the entire ML supply chain, including model scanning, artifact integrity, and dependency risk.
- Aikido Security: Aikido takes a unique approach to AI security by focusing on the software supply chains and AI-driven development workflows. Aikido offers Continuous compliance, AI-powered detection, integration across CI/CD pipelines, AI code reviews and AI pentesting like no other enterprise security tools.
Additional AI infrastructure Security Resources
- The CISO vibe coding checklist for security
- Best 6 AI Pentesting Tools in 2026
- The Rocky Path of Managing AI Security Risks in IT Infrastructure
Enterprise Extended Detection and Response (XDR)
Modern attacks rarely stay confined to a single domain. Threats move laterally across endpoints, cloud workloads, identities, and networks which often evade siloed security tools such as standalone endpoint protection or traditional intrusion prevention systems (IPS).
XDR emerged as a way to automatically collect and correlate data from these sources.
XDR uses AI and ML to analyze large datasets, identify behavioral anomalies, and prioritize threats, reducing alert fatigue.
Why Extended Detection and Response (XDR) is Essential
A typical enterprise has thousands of microservices, uses multiple cloud providers, has on-prem infrastructure and employees across different timezones.
XDR reduces alert fatigue, shortens mean time to detect (MTTD), and helps security teams respond to incidents with better context and automation.
Top 3 Extended Detection and Response (XDR) Products
- Palo Alto Networks: Delivers a tightly integrated XDR platform combining endpoint, network, and cloud telemetry with strong automation capabilities.
- CrowdStrike: Built on a powerful endpoint foundation, with expanding XDR capabilities across identity, cloud, and log data.
- Microsoft Defender: Microsoft offers XDR through Microsoft Defender, tightly integrated with Microsoft 365, Azure, and Entra ID. This is best for enterprises heavily invested in the Microsoft ecosystem.
Additional Extended Detection and Response (XDR) Resources
- Extended Detection and Response (XDR) Reviews and Ratings
- What Is XDR (Extended Detection and Response) and Why Do You Need It?
- G2 Review of Extended Detection and Response (XDR) Platforms
Enterprise Cloud Native Application Protection Platform (CNAPP)
A Cloud-Native Application Protection Platform (CNAPP) is a unified cloud security solution designed to protect applications across their entire lifecycle from code to cloud and at runtime.
Aikido Security’s 2026 State of AI in Security & Development report shared that 93% of teams struggle to integrate application software security with cloud security, resulting in gaps where threats can slip through unnoticed.
A complete CNAPP solution typically includes:
- Cloud Security Posture Management (CSPM)
- Cloud Workload Protection (CWPP)
- CI/CD and IaC Scanning
- KSPM (Kubernetes Security Posture Management)
- Runtime Threat Detection
Why Cloud Native Application Protection Platform (CNAPP) is Essential
A CNAPP solution ensures you have:
- Full-Stack Visibility
- Fewer Alerts
- DevOps Friendly Security
- Consolidation and Cost Efficiency
- Continuous Compliance
Top 3 Cloud Native Application Protection Platform (CNAPP) Products
Not all platforms with the CNAPP label are equal. Here are our top 3:
- Aikido Security: Aikido Security is an AI-driven security platform designed to secure every aspect of the cloud application lifecycle, from code and dependencies to containers, multi-cloud infrastructure, and runtime. Aikido offers:
- End-to-end coverage,
- SSO and RBAC support,
- Optional on-prem deployment,
- Out-of-the box compliance controls,
- AI-driven noise reduction.
- Lacework FortiCNAPP: Lacework is a data-driven CNAPP platform known for its patented “Polygraph” technology. Its Polygraph Data Platform maps behaviors across your cloud to surface threats and misconfigurations.
- Sysdig Secure: Sysdig is primarily used by organizations running Kubernetes and container heavy workloads. It also offers runtime threat monitoring as it originates from open-source Sysdig and Falco projects.
Additional CNAPP Resources
- Top 9 Cloud-Native Application Protection Platforms (CNAPP) in 2026
- What Is CSPM (and CNAPP)? Cloud Security Posture Management Explained
- Gartner Cloud-Native Application Protection Platforms Reviews and Ratings
Enterprise Identity and Access Management (IAM) & Multifactor Authentication (MFA)
Modern enterprise security starts with identity. The first step to effectively managing identity access is to make sure every identity has access to what they need and nothing more. That is what the Principle of Least Privilege (PoLP) encourages.
But even with every identity having only the access they need, it is still important to implement multi-factor authentication, especially for admin accounts. MFA adds an additional layer of protection.
Why IAM & MFA is Essential
Credential compromise remains one of the most common entry points for enterprise data breaches. As organizations grow, managing access across thousands of users, applications, APIs, and cloud services becomes increasingly complex and manual controls are impossible.
IAM and MFA help enterprises:
- Enforce least-privilege access consistently
- Reduce the blast radius of compromised credentials
- Centralize identity governance across cloud and on-prem environments
- Support secure remote and third-party access
Top 3 IAM & MFA products
- Okta: A leading IAM platform offering single sign-on (SSO), adaptive MFA, lifecycle management, and broad SaaS integrations.
- Apono: Offers an IAM platform with speciality in Just-in-Time and Just Enough Priviledges access
- Cloud providers IAM: Leading cloud providers like AWS and Microsoft offer IAM for their services and resources. These IAM products can also be expanded with 3rd party software like Okta and Apono mentioned earlier.
Additional IAM & MFA Resources
Enterprise Incident management
Enterprises today operate across multiple clouds, regions, and business units, often with distributed security teams. When an incident occurs, lack of coordination, unclear ownership, and manual processes can significantly delay containment and recovery.
Why Incident management is essential
Security incidents are inevitable. Over 2,200 cyberattacks occur daily worldwide. The difference between disruption and disaster lies in how effectively an organization responds. Incident response is less about individual heroics and more about repeatable, coordinated execution.
Aside from creating the best possible security team, the next best thing you can do is to empower them with the right tools.
Incident management help organizations:
- Standardize incident handling and escalation
- Reduce mean time to respond (MTTR)
- Improve cross-team collaboration during incidents
- Maintain audit trails for compliance and post-incident reviews (Postmortem)
Top 3 Incident Management Tools
- Incident.io: A relatively new kid in the block, Incident.io has quickly become a leader in the incident management space. With products ranging from On-call to response and recently AI SRE, if you are considering an incident management plus response tool, Incident.io should be among your options.
- Pagerduty: Founded in 2009, Pagerduty is widely used for on-call management, alerting, and incident coordination, with strong integrations across monitoring and security tools.
- ServiceNow: Offers incident response as part of its broader security operations and ITSM platform, enabling deep workflow automation and reporting. Can be an overkill if you just want a platform to manage incident escalation and remediation.
Additional Incident Management Resources
- The Incident, On-call and Reliability Conference
- Google Site Reliability Engineering: Incident Management Guide
Enterprise Backup and Disaster Recovery
Backups ensure organizations can recover systems, data, and services after outages, ransomware attacks, or catastrophic failures.
While often grouped with IT operations, enterprise backup and recovery tools play a critical role in modern security strategies especially as ransomware attacks increasingly target backups themselves.
Why Backup and disaster recovery is essential
It is not about if disaster will happen, it's about what to do when it does. Without reliable backups and tested recovery processes, organizations face prolonged downtime, data loss, and regulatory exposure.
Backup and disaster recovery tools help enterprises:
- Restore systems quickly after ransomware or outages
- Protect critical data across cloud and on-prem environments
- Meet regulatory and business continuity requirements
- Reduce financial and reputational damage
Top 3 Backup and Disaster Recovery Tools
- Veeam: A market leader in enterprise backup and recovery. Veeam supports virtualized, cloud, and physical workloads. For enterprises with hybrid environments that require strong recovery point and time objectives, consider Veeam.
- Rubrik: Focuses on cloud-native backup, ransomware resilience, and fast recovery with strong automation.
- Commvault: Known for its depth in data management, ransomware recovery, and compliance-driven recovery workflows. Commvault offers comprehensive protection across on-prem, hybrid, and multi-cloud environments. A Reddit user said: “Rubrik if you can afford it. Veeam if you're in the middle. I've been pretty happy with Commvault for many years, but Veeam and Rubrik seem to be developing faster, especially in cloud”.
Additional Backup and Disaster Recovery Resources
- Reddit thread on enterprise backup
- Disaster Recovery (DR) Architecture on AWS, Part II: Backup and Restore with Rapid Recovery
Choosing the Right Enterprise Security Platform
The landscape of enterprise security is dominated by powerful platforms from vendors like Palo Alto Networks, CrowdStrike, and Fortinet. These tools are essential for protecting the traditional boundaries of the enterprise—networks and endpoints. They form the backbone of a strong defensive posture.
However, the modern enterprise is built on software. Applications are the new perimeter, and securing them requires a different approach. This is where traditional tools often fall short, and a new generation of security platforms excels.
Aikido Security stands out as the best overall tool for the modern enterprise because it addresses this critical gap. By unifying application and cloud-native security, eliminating alert fatigue, and embedding security directly into the development process, Aikido helps organizations secure their most valuable assets: the applications that drive their business.
Aikido complements traditional enterprise tools by securing the software supply chain from the inside out, creating a truly comprehensive and resilient security strategy for 2026 and beyond.




