Checkmarx has been a leader in static application security testing (SAST) since 2006. It scans code in dozens of languages and finds complex vulnerabilities that not all tools catch. It has strong brand recognition in the compliance world and provides detailed analysis for security teams.
But Checkmarx has some real limitations, like long scan times, high false positive rates, and a central scanner built for waterfall development cycles rather than CI/CD workflows. Combined with missing modern features, continuing to pay its high price gets hard to justify. And with on-prem contracts ending after 2025 and Checkmarx One showing the same limitations as the older legacy platform, many teams are exploring what’s out there.
We’ll look at eight alternatives to Checkmarx:
Some are specialists focused on doing one thing exceptionally well, while others cover more ground (Aikido notably does both). Each section explains what the tool does and why you may want to consider it over Checkmarx.
What Problems does Checkmarx Solve?
Checkmarx was built for CISOs and AppSec teams who need policy enforcement, audit trails, and executive reporting. The platform works for large enterprises with mature AppSec programs, specialized security teams, and the patience to manage heavy tooling. If you're in a heavily regulated industry where compliance documentation matters more than developer velocity, Checkmarx has been a decent fit until the last five or so years, when modern security platforms began to emerge.
Checkmarx’s platform also handles polyglot codebases, scanning dozens of languages without requiring separate tools for each stack. For organizations with legacy infrastructure, COBOL support is the only real differentiator since few security tools can handle it.
On the technical side, Checkmarx's exploitable path analysis traces how an attacker could exploit a vulnerability by showing the full call path from user input to vulnerable functions. While it helps prioritize remediation by identifying which vulnerable code is actually reachable, it’s more of a remediation aid than a noise filter for false positives (we’ll get to that later).
While known primarily for its SAST offering, it also has open-source vulnerability scanning and dynamic application security testing (DAST) as part of Checkmarx One, its cloud-based offering introduced in 2021.
What are the Challenges with Checkmarx?
Checkmarx launched in 2006, when security testing happened at the end of the development cycle. It’s evolved since then, but parts of the platform still feel rooted in the waterfall era. Checkmarx on-prem contracts are now at “end-of-life” as Checkmarx pushes users to migrate to Checkmarx One. Organizations using the legacy platform now have to decide whether to migrate or explore other options.
Checkmarx One is essentially the original on-prem engine moved to the cloud rather than rebuilt from the ground up. That means it still relies on centralized scanning, which requires significant workarounds to fit into modern CI/CD pipelines. Customers describe the experience as feeling like it’s still in beta-testing with UI bugs, missing features, and dashboards that are less flexible than the on-prem version.
False positives are also a big problem. Checkmarx's own studies put its false positive rate at around 36%, which means security and development teams spend a large amount of time triaging alerts that turn out to be noise (if devs don’t just start ignoring them instead). Full scans can take 25 to 45 minutes per application, which is much slower than other tools that can do this in seconds. There's no issue grouping to make sense of the findings, nor is there SLA reporting to give teams visibility into how quickly findings are getting resolved.
Then there's the cost: Checkmarx starts at $40K annually. For that spend, you'd expect strong support and a state-of-the-art product. Neither holds up especially well; their customer support isn’t very strong, and the platform still lacks some essential security capabilities: CSPM, runtime protection, malware detection, and automated vulnerability triaging and fixing. If your team is running into any of these pain points, it's worth taking a serious look at what the alternatives actually offer.
What are the Top Checkmarx Alternatives?
Aikido Security
Secure your code, cloud, and runtime in one central system.
Aikido Security secures everything end-to-end in one platform for code, cloud, and runtime. Aikido includes capabilities that Checkmarx doesn't, at a fraction of the cost, without compromising; Aikido regularly comes out on top of head-to-head enterprise pilots on performance. In addition to SAST, DAST, and SCA, Aikido provides AI Code Quality analysis, CSPM, runtime protection (in-app firewall), and malware detection, and puts findings directly into the tools developers already use. Teams using separate AppSec and CloudSec tools are 50% more likely to face incidents, so when you consolidate your tools in Aikido, you’re also lowering your risk of a major breach.
For organizations that need compliance-focused tools, Aikido maps security findings to ISO 27001, SOC 2, OWASP Top 10, NIS2, PCI DSS, and HIPAA, and integrates directly with GRC platforms like Vanta, Drata, Secureframe, and Thoropass to automate control validation. While Checkmarx offers compliance reports, it doesn’t have automated integration, so you have to manually export data and build custom reports to achieve a similar outcome. In addition, Aikido’s AI pentesting also automatically provides audit-ready pentest reports that map directly to the appropriate standards.
In terms of technical differences, when comparing Checkmarx with Aikido:
- Aikido reduces false positive rates with EPSS and AI based-prioritization. Checkmarx's own studies report a 36% false positive rate. Aikido Security uses AI AutoTriage and reachability analysis to filter out noise and dramatically reduce false positive. Over a 6-week Aikido pilot period, 50 devs from a global HRtech platform resolved 92% of critical issues and reduced critical false positives by 99% vs their Checkmarx, their existing AppSec platform (Remember, more findings do not equate to a better platform)
- Aikido scans run in minutes, not hours. Checkmarx SAST scans take 25-45 minutes per application. Aikido Security scans complete in seconds and provide instant PR feedback.
- Aikido setup is quick and easy. Checkmarx needs excessive customization of scanning engine rules, and often needs dedicated staff for implementation and maintenance. Aikido Security connects to repos in 10 minutes via GitHub App or CLI with no pipeline setup required, so you can start to get feedback right away.
Aikido's platform requires less investment (both upfront and overtime), produces significantly fewer false positives, and is easier to use— meaning the overall value of the product (actually getting security done properly and faster) is far higher.
Checkmarx requires you to conform your development workflow to its centralized scanning model, while Aikido gives you total flexibility. And when something does need fixing, Aikido’s AI AutoFix automatically generates pull requests for SAST, IaC, and container issues, with the minimal safe upgrade already calculated. Engineers notice the difference in their workflows immediately. “We tried Checkmarx… but Aikido was faster, more actionable, and easier to work with,” said Ega Sanjaya, Development Head Manager at Faspay. “We needed better security, but not at the cost of productivity.”
To get all those services with Aikido Pro, it will cost you under $10,000 for the year for 10 users. You’d have to spend over $40,000 to get the same services with Checkmarx, which is harder to justify with the smaller feature set and limited cloud usability. Aikido is just a better value overall.
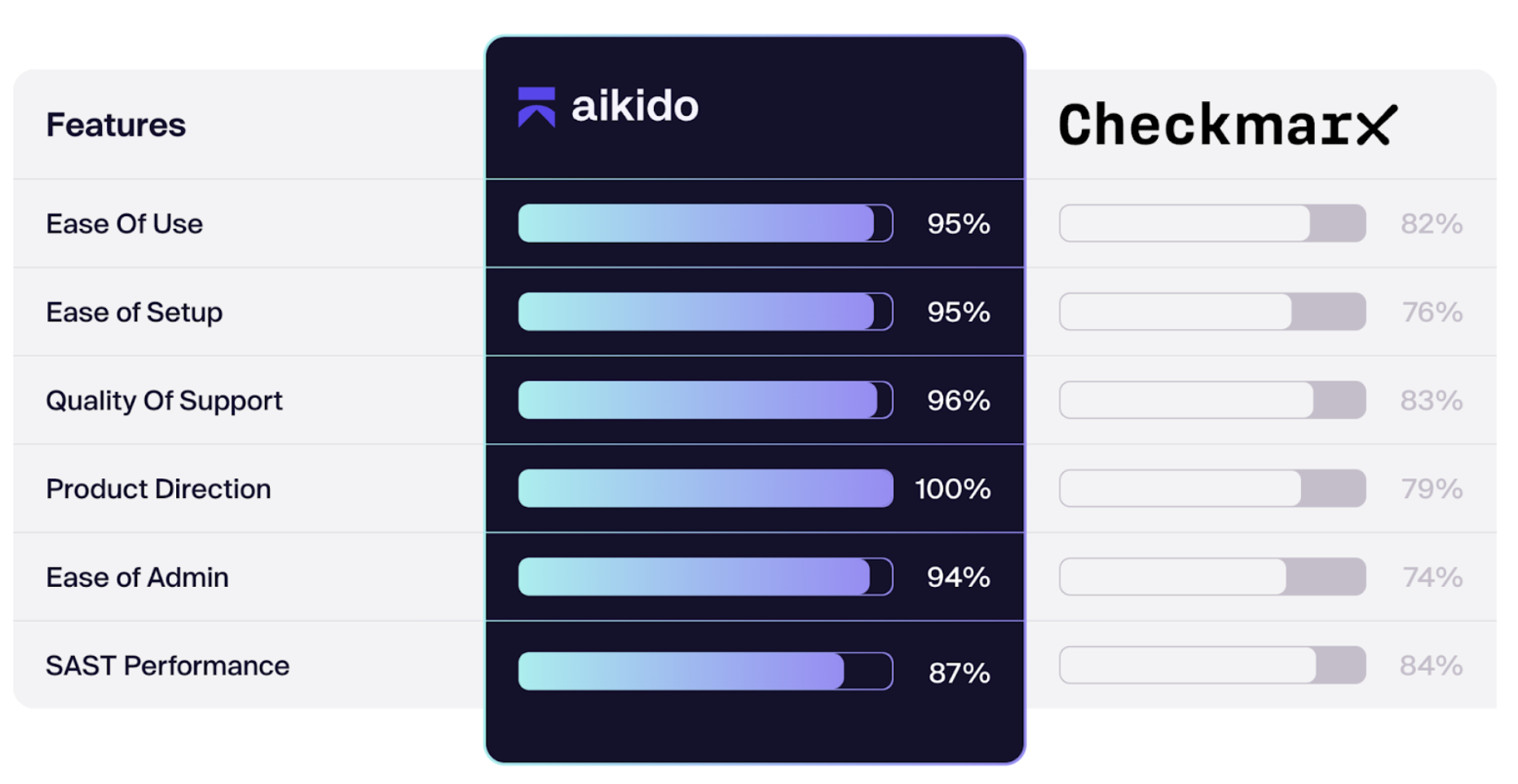
Aikido vs Checkmarx
Top Features
- Comprehensive Coverage: SAST, DAST, SCA, CSPM, Runtime Protection
- 85% False Positive Reduction via AI AutoTriage
- AI AutoFix for SAST, IaC, and Containers
- Built-In Compliance Mapping (ISO 27001, SOC 2, PCI DSS)
- Fast Setup– Minutes to First Results
- AI Pentesting
Further reading:
Compare: Aikido Security vs Checkmarx
Read: Gartner Reviews Aikido vs Checkmarx
Compare: G2 rates Aikido at 4.6 stars, Checkmarx at 4.2 stars
Black Duck
Legacy SCA leader focused on open source compliance and license management
While Checkmarx added SCA capabilities later (mainly in Checkmarx One), Black Duck has focused on open source vulnerability detection as its core function. If you're scanning binaries, compiled code, or third-party libraries where you don't have source access, Black Duck's detection is more accurate than Checkmarx.
For teams in regulated industries or enterprises with strict compliance requirements, Black Duck's license compliance tracking is more mature. It catches license conflicts, copyleft obligations, and export control issues that Checkmarx's SCA add-on won’t do. If your legal team needs audit trails on every open source component, Black Duck provides this for compliance-heavy organizations.
However, similar to Invicti’s limitations, Black Duck has a pretty limited scope– open source dependencies are covered, but it doesn’t give you SAST or DAST. You’ll need to pair it with other tools to get the coverage you get from Checkmarx, and if you’re an enterprise, you can expect to drop at six figures on Black Duck alone. Finally, as a legacy company, Black Duck also comes with some legacy issues: an outdated UI, an experience not created for developers, and slower scan times.
Top Features
- 20+ years of SCA expertise with a vulnerability database (5M+ projects)
- Binary analysis for C/C++ compiled code
- Black Duck Security Advisories (BDSAs) weeks ahead of NVD
- Industry-leading SBOM generation
- Superior license compliance and policy enforcement
Cycode
Cycode takes a different approach than other security tools on this list. Instead of just scanning your code for problems, it tries to be a central hub that pulls together findings from all your other security tools and shows you how everything connects. If you're using Snyk for dependencies, GitHub for code scanning, AWS Security Hub for cloud issues, and a SIEM for monitoring, Cycode ingests all of that data (it can connect to over 100 different tools) and builds a map of how risks flow through your system. If you have a collection of security tools you can’t get rid of, Cycode can help you make them work together for you.
Cycode has its own SAST, SCA, and IaC scanners like Checkmarx, but also does things Checkmarx doesn't touch. It scans for secrets across your entire development lifecycle, in code and in logs, infrastructure configs, Kubernetes, Docker, even Slack messages. Other features include monitoring your CI/CD pipelines for security misconfigurations and detecting when your source code leaks somewhere on the internet.
Cycode does fall short as a Cherkmarx alternative in a few ways. Cycode doesn’t have IDE integration or DAST , and neither tool covers malware detection, so you have to get another tool for that.
Beyond coverage, users frequently report bugs, so engineers have to depend on Cycode support to fix issues that shouldn't exist in an enterprise product (that has an enterprise price tag). The interface has bizarre limitations, like not being able to use it fully while scans run or open multiple windows at once, and onboarding is complex because the platform tries to do so much. Keep this in mind if you’re seriously considering Cycode as an option.
Top Features
- Risk Intelligence Graph correlating 100+ tools
- Secrets scanning (code, logs, IaC, Kubernetes, Slack)
- CI/CD security posture management
- Code leakage detection across the internet
- Automated remediation options
- End-to-end supply chain visibility
GitHub Advanced Security
Native GitHub security scanning for teams already on the platform
If your team already works in GitHub, GitHub Advanced Security (GHAS) is worth a look as a beginner’s security tool. You get code scanning, secret detection, and dependency review without leaving your workflow, with security findings appearing as PR comments.
CodeQL is GitHub's proprietary semantic code analysis engine that powers GHAS’s SAST capabilities, which works well for standard use cases. CodeQL works differently from other SAST scanning methods by treating code like data in a database. It creates a database representation of your codebase, then you run queries against that database to find vulnerabilities. However, CodeQL times out on large repositories after an hour or two, so for enterprises with large codebases, GHAS might not be a good fit. There’s also no reachability analysis to filter out false positives, giving us another noisy SAST tool.
Since GHAS only looks at your code in GitHub, it only covers a narrow slice of application security; there's no DAST, no API security testing, no runtime protection, no IaC scanning, and no CSPM. So if (when) you inevitably need DAST or container scanning or cloud security, you'll need to research more tools anyway.
Top Features
- CodeQL for SAST with high detection rates
- Secret scanning with push protection
- Dependency review in pull requests
- Custom auto-triage rules for Dependabot
- No context switching for GitHub-native teams
Invicti
DAST-focused web application security with proof-based scanning
Invicti’s main strength is dynamic application security testing. Its DAST coverage is broader than Checkmarx's API-only scanning, which means it can catch runtime vulnerabilities that Checkmarx's DAST wouldn't detect.
Invicti uses proof-based verification, attempting to exploit vulnerabilities to confirm they exist rather than flagging theoretical patterns. While this approach is not as strong as reachability analysis in other static scanning tools, it does help in filtering out noise. Checkmarx doesn't do any of this (refer to Checkmarx’s high false positive rate above).
However, Invicti is a DAST-only solution, which prevents it from being a complete alternative to Checkmarx. You'd still need other tools to cover some of Checkmarx’s features, assuming you want full application security. Invicti scans running applications and APIs, but it doesn't analyze source code or check dependencies for known vulnerabilities. That means you'd still need separate tools for SAST and SCA to get the coverage Checkmarx provides. Invicti also charges around $37,000 annually and charges per domain, so you're paying enterprise money for a point solution.
Scan speed is another consideration, since Invicti can be slow on large applications. This becomes a problem if you're running scans frequently as part of CI/CD (which you very may well be, since it’s best practice).
Top Features
- Industry-leading DAST accuracy with low false positives
- Proof-based scanning
- REST/SOAP API security testing
- Advanced crawling for more complex applications
- Popular with enterprise customers
Veracode
Enterprise security platform with binary scanning for regulated industries
Veracode covers more ground than Checkmarx, which is appealing if you need security coverage across the board. It scans code, cloud infrastructure, containers, IaC templates, and manual penetration testing. The binary scanning capability is solid if you need to analyze compiled applications without source access, and the compliance documentation is built for regulated industries that need audit-friendly reports. If your organization runs on governance processes and you need a tool that speaks that language, Veracode does that better than Checkmarx. It also offers AI-assisted vulnerability fixes, although that's limited to specific languages.
Veracode, unfortunately, comes with its own list of drawbacks; the first is that it’s super slow. You upload your code to their environment and wait hours to days for scan results, which kills any hope of real CI/CD integration. The IDE support is minimal compared to other tools on the market, so developers don't see findings where they're actually writing code.
Strangely (and a bit counter-intuitively), Veracode makes you jump through a lot of hoops to earn the privilege of using them as a product– even getting your hands on the product for evaluation requires proving you're serious first. You fill out a compatibility questionnaire, wait for Veracode to turn on access on a specific day, and you're not allowed to test beyond what you defined upfront. Veracode is also expensive and doesn't publish pricing, like Checkmarx. And after you purchase it, setup takes months.
The bigger issue is that Veracode's scan engines don't talk to each other. Each module produces its own output with no central correlation layer to connect findings across SAST, DAST, and SCA. You're managing multiple streams of alerts that don't deduplicate or prioritize based on actual risk. The result is noise that requires significant adjustments and configuration to make actionable, which is the same problem teams are trying to escape from Checkmarx.
Top Features
- Binary/bytecode analysis without source code access
- Strong compliance reporting for audit requirements
- AI-assisted vulnerability fixes
Snyk
Developer-first security with focus on open source dependencies
Snyk is a cloud-native security platform that scans your code, open source dependencies, containers, and IaC files directly within your existing developer workflows. SCA was Snyk's original focus, so it's genuinely strong ground for them, versus Checkmarx One’s SCA offering, which was created as an add-on later.
Since it was built with cloud setups in mind, Snyk feels like it was designed for engineering teams rather than security teams (unlike Checkmarx). For example, Snyk’s CI/CD integration can be set up relatively quickly with a CLI tool. Checkmarx, on the other hand, requires that your pipelines are set up in a specific, consistent way, such as standardizing which IDE everyone uses (sorry, devs) and setting up workarounds to get scanning triggered on commits (the native integrations only do scheduled scans by default).
That said, Snyk has grown through acquisitions over the years, which shows in some clunky integrations (like with Jira) and a disconnected dev experience. Its customers have grown frustrated with its opaque product roadmap, with little influence over significant feature and capability updates. Customer support is also limited; If you want support beyond the self-serve tier, you won’t get human support until you spend $20K, and costs add up quickly through separate charges for CI/CD, API access, container scanning, and reporting. Like Checkmarx, it still floods developers with false positives (potentially even more than Checkmarx), which leads to developers potentially ignoring alerts. Checkmarx’s reputation is still stronger for enterprises than Snyk. It's for this reason that many organizations are also considering Snyk alternatives.
Top Features
- IDE integration for select IDEs (VS Code, IntelliJ)
- Free tier for small teams
- Established provider in container security
- AI code fixes for remediation
- CI/CD integration
- SAST, DAST, SCA, IaC
SonarQube
Code quality platform with basic security features
SonarQube is a code quality tool first, with security features added later, so this may be an option for you if you’re looking for code-quality primarily and security second. It focuses on readability, refactoring, and stylistic rulesm but covers some security basics as well.
SonarQube runs on your own infrastructure by default, so your code stays in-house. For developers, SonarLint provides real-time feedback in its IDE, and you get branch analysis, technical debt tracking, and a unified view of both code quality and security findings in one dashboard. The open-source community is massive, which means plugins, customizations, and troubleshooting help are available. However, as with many other legacy vendors, it’s behind on modern features like AI code review. And while the free Community Edition gives you code quality analysis plus basic security scanning, the paid product can get expensive fast.
Because SonarQube is fundamentally a code quality tool with security treated as a limited add-on, the security engine and coverage are basic– the majority of its focus is on code quality, complexity metrics, and maintainability. There's no DAST, no container scanning, no cloud security, no API security testing, and no reachability analysis to filter out noise.
If you need actual application security coverage, you'll still need a tool like Aikido for dependency scanning, something like Invicti for DAST, and probably a cloud security tool on top. Checkmarx, although not best in class for all its features, covers more than SonarQube does.
Top Features
- Best-in-class code quality metrics (complexity, technical debt, code quality)
- Free Community Edition with powerful capabilities
- Simple deployment
- Open-source option for self-hosting
- Over 30 languages for quality analysis
Conclusion
Among the Checkmarx alternatives, Aikido Security offers the strongest combination of cost, coverage, and developer experience. It reduces false positives by 85% through AI AutoTriage and reachability analysis, which directly addresses the noise problem that plagues Checkmarx. Combined with the AI AutoFix feature, developers spend way less time sitting in security tools and more time developing.
That said, some competitors excel in specific areas. SonarQube's free Community Edition and focus on code quality make it hard to beat for teams that want both security and maintainability. GitHub Advanced Security is a great starting point for teams already working in GitHub. If you’re looking for a tool that focuses more on governance processes, then Veracode is a better option than Checkmarx.
For organizations tired of managing multiple narrow tools, high false positive rates, and systems built for security teams instead of developers, Aikido consolidates what used to require three or four separate products into a single platform to make security easier.
If you’re ready to simplify your application security, try Aikido Security for free or book a demo to see it in action.
FAQ
You Might Also Like:




