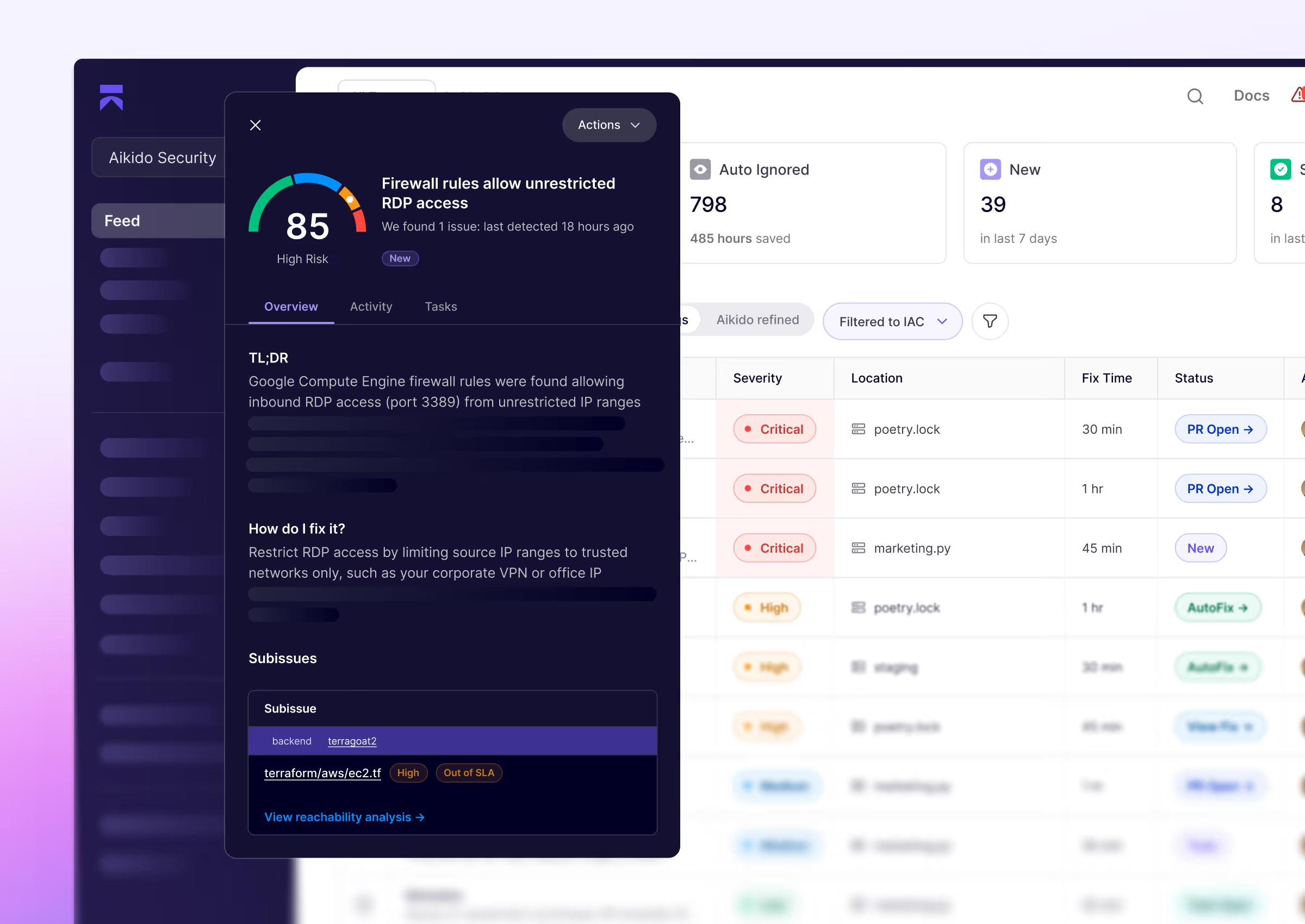
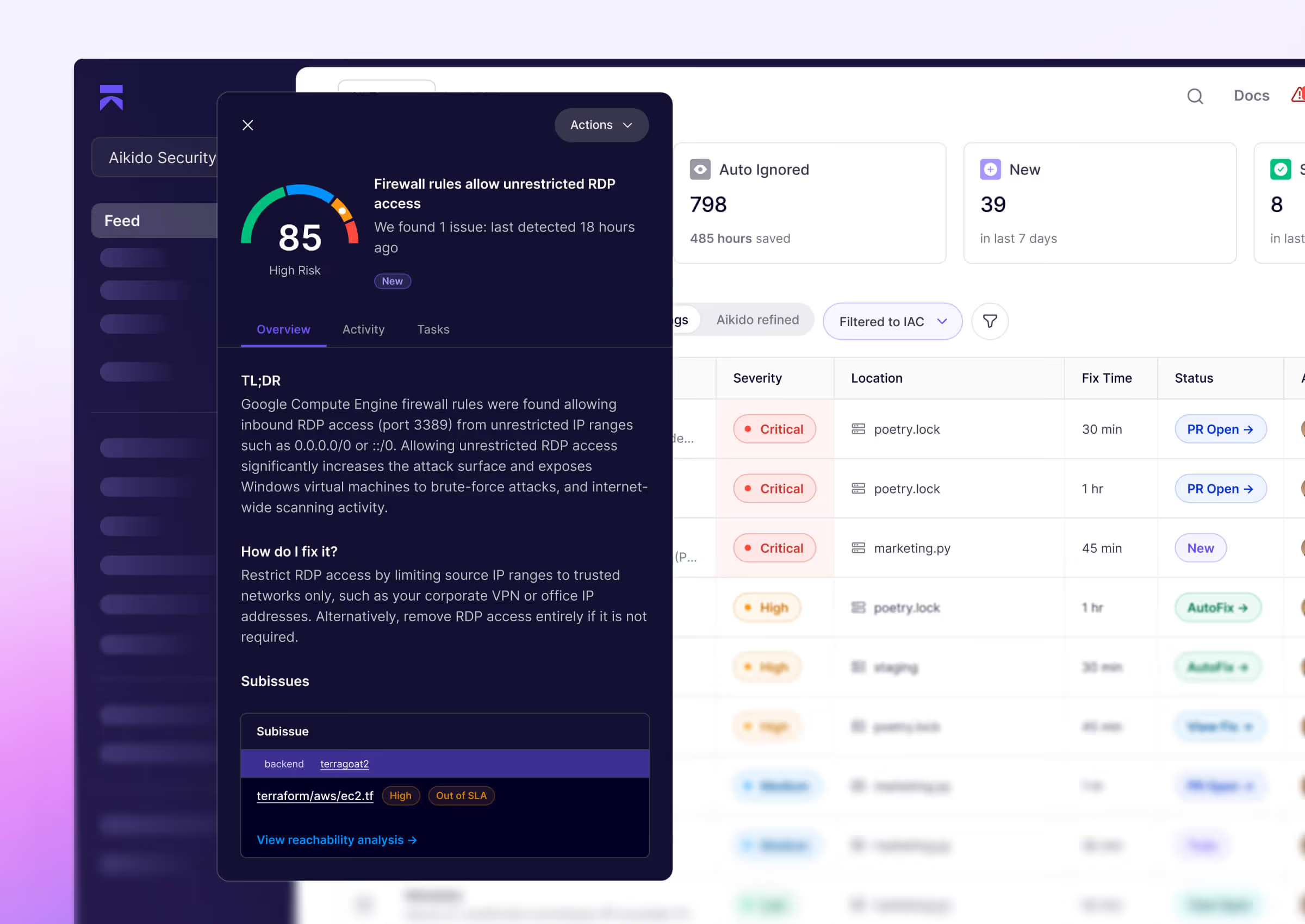
Scan and catch IaC misconfigurations early
Scan every Terraform, CloudFormation, and Helm change for critical misconfigurations.






























Why IaC scanning matters
Infrastructure as Code (IaC) scanning is crucial because it shifts security to the start of development. It checks your infrastructure definition scripts (Terraform, CloudFormation, Helm, etc.) for misconfigurations before they provision your cloud resources.
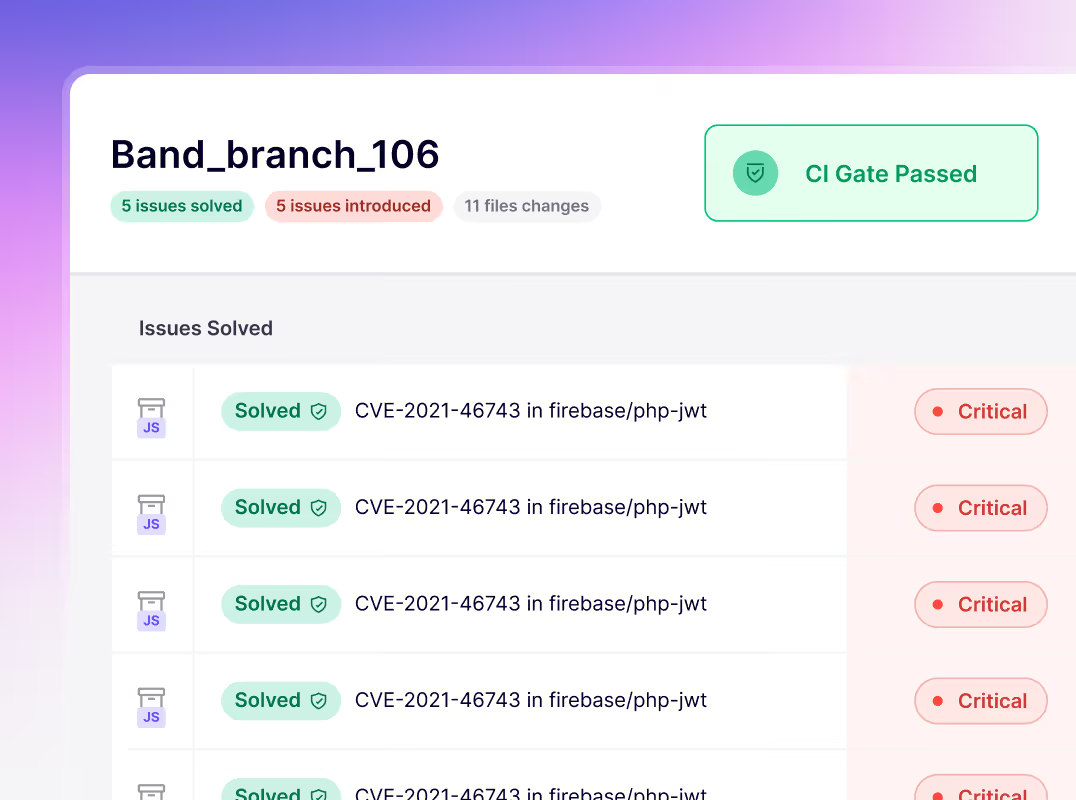
CI/CD integration
By integrating Aikido into your CI/CD pipeline, IaC misconfigurations are identified before they reach your main branch.
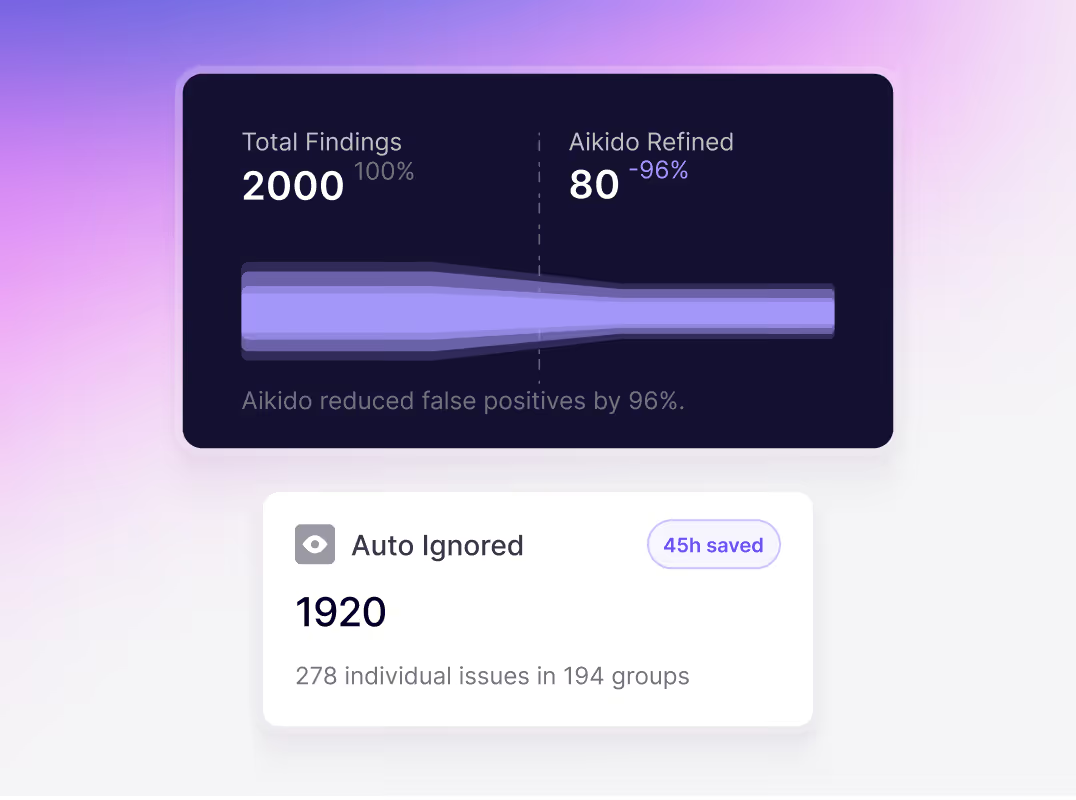
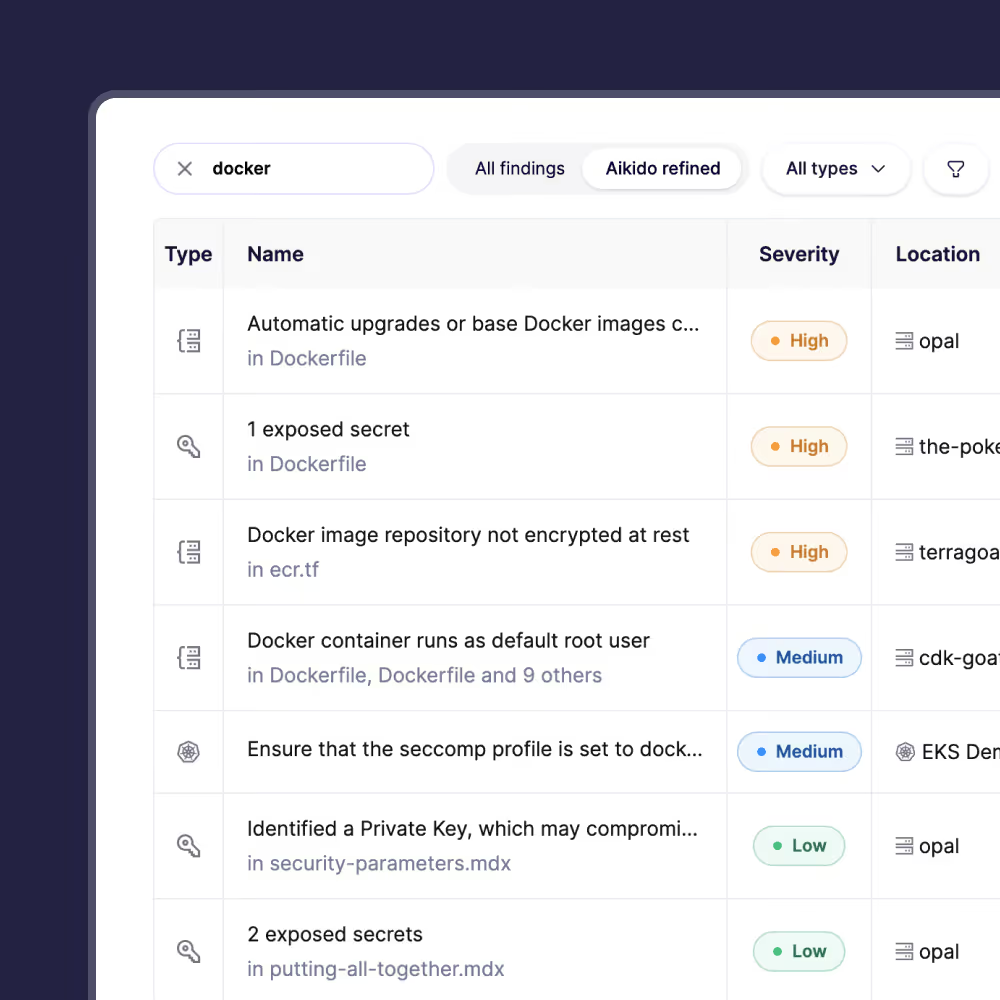
Only shows security issues
Shows only misconfigurations that pose a security risk, so you aren’t overwhelmed by noise.
Aikido's IaC features

“Aikido is used by different departments (Dev teams, infra, CISO) to view our security posture. This improves security awareness as well as helps us to place the right priorities to solve issues”
Patrick LCISO at HRlinkIT
FAQs about IaC scanning

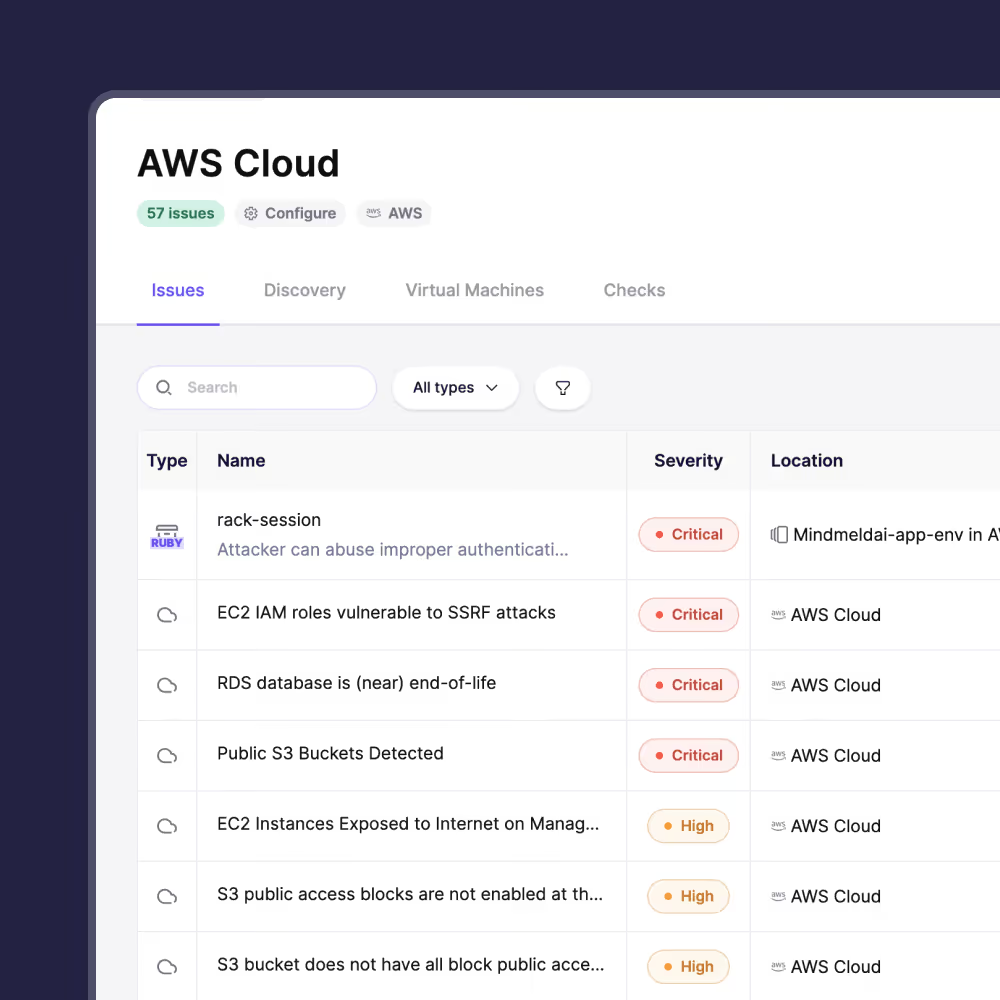
IaC scanning analyzes your infrastructure code (e.g., Terraform, CloudFormation, Kubernetes YAML) for misconfigurations before deployment. It helps catch issues like open S3 buckets or weak firewall rules early in the dev cycle. Fixing them in code is far easier than after they're live. Scanning ensures your cloud is secure by design - no surprises in production.

Aikido flags public storage buckets, overly open security groups (e.g., 0.0.0.0/0), unencrypted databases, excessive IAM permissions, and public VMs. It checks your code against best practices to catch common and critical misconfigs before deployment.

Aikido supports Terraform, CloudFormation, Kubernetes manifests, Helm charts, Azure ARM/Bicep templates, and more. Whether you use HCL, YAML, or JSON, Aikido can scan it for risks. Pulumi support is coming soon.

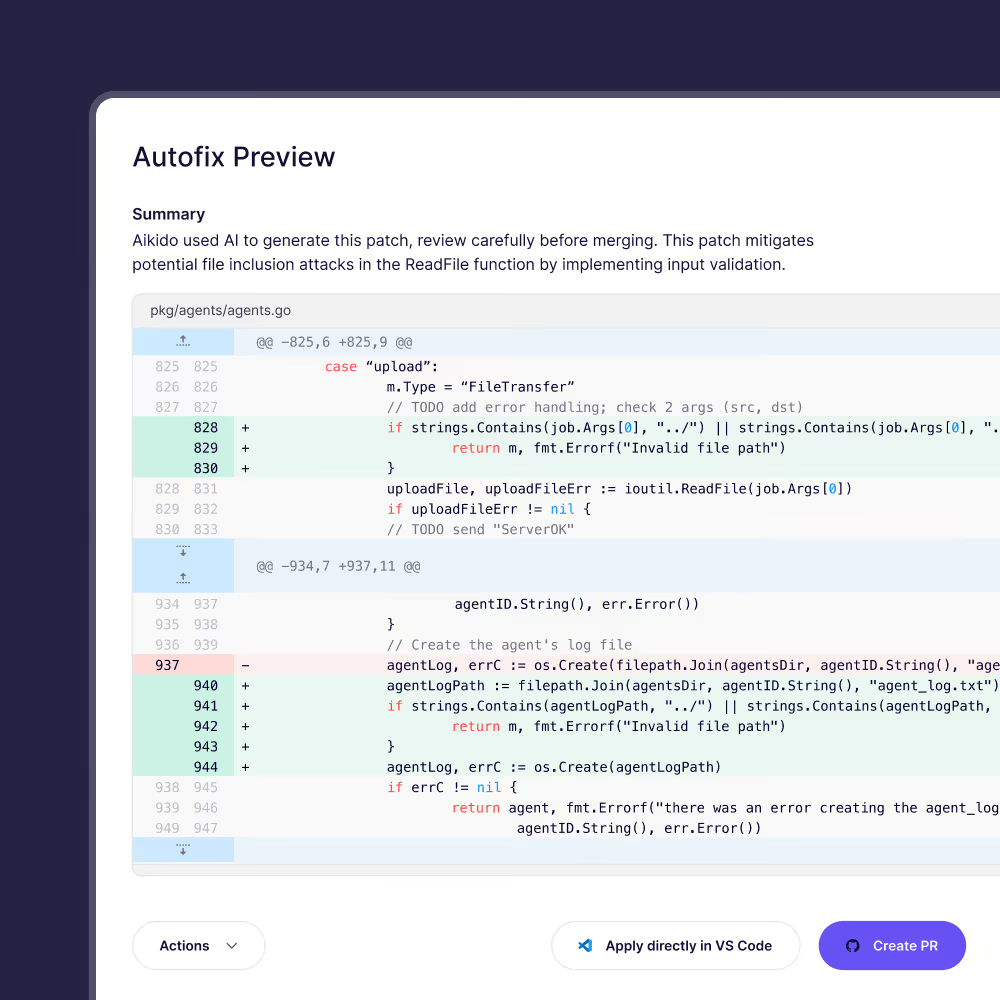
Yes. Aikido suggests best-practice fixes and can auto-generate code patches or pull requests. For example, it can fix open security groups or missing encryption with one click. The fix will be available as a PR/MR for you to review and merge.

You can integrate Aikido into CI/CD tools (GitHub Actions, GitLab, Jenkins, etc.), pre-commit hooks, or IDEs. Scans run automatically on commits or PRs and can block misconfigurations before merge or deploy.

Yes, it's fast and CI-friendly. Scans typically take seconds and don't interfere with Terraform apply. Even large projects complete quickly, making it practical for everyday use.

Aikido offers similar coverage but integrates with your full security stack. It reduces noise, auto-suggests fixes, and correlates IaC issues with running cloud resources. Unlike using multiple tools, it's all in one platform.

Yes. You can create custom rules - e.g., "S3 buckets must have logging" or "disallow region X." Aikido supports flexible policy controls so your scans reflect your internal security standards.

You can mark findings as ignored, accepted risk, or false positive. You can also customize rules to avoid blocking your CI/CD pipeline for intentional configs.

You can adjust severity, add code annotations, or use config files to suppress specific checks. Aikido is built to adapt to your environment and reduce friction - not to block intended workflows.
Secure your cload configurations today
Secure your code, cloud, and runtime in one central system.
Find and fix vulnerabilities fast automatically.

















.png)