Pentest your Lovable app before someone else does it for you
Shipping fast doesn't mean shipping blind. AI agents find real vulnerabilities in your app, inside Lovable, before you go live.






























Ship fast with Lovable. Know it's secure with Aikido
Tests your live app like a hacker
Your code can look clean and still have gaps that only show up once it's live. Aikido finds those.
Detect injection flaws before they're exploited
Catch broken access control & data exposure
Expose authentication bypass vulnerabilitie
Uncover chained attack paths across your app
How to Pentest your Lovable app
For every software business, big or small
For the founders
Go from "I trust it's secure" to "I can prove it's secure"
A security test of your live application
Shareable report for investors, customers, and auditors
Audit-ready for SOC 2, ISO 27001, and security questionnaires
Plain-language fix instructions you paste into Lovable, or one-click remediation
For enterprise teams
Shipping Lovable apps faster than security review can keep up
Test your full portfolio of Lovable apps across the org
Visibility into security posture across everything your team ships
Shareable PDF reports for internal reviews and client requirements
Scalable pricing with an in-app calculator for larger apps
Industry leading pentests, built into the world's biggest vibe coding platform







Frequently Asked Questions

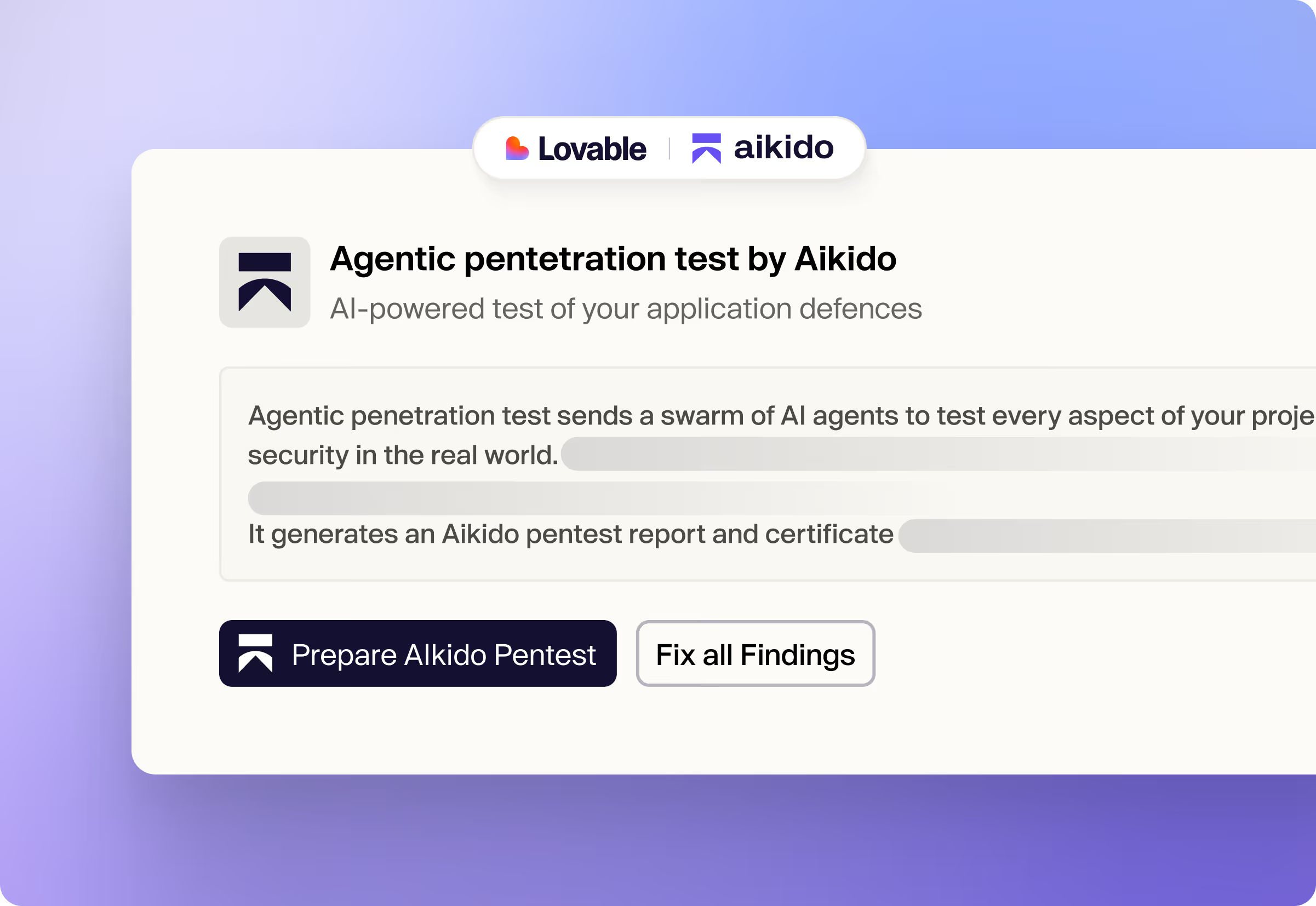
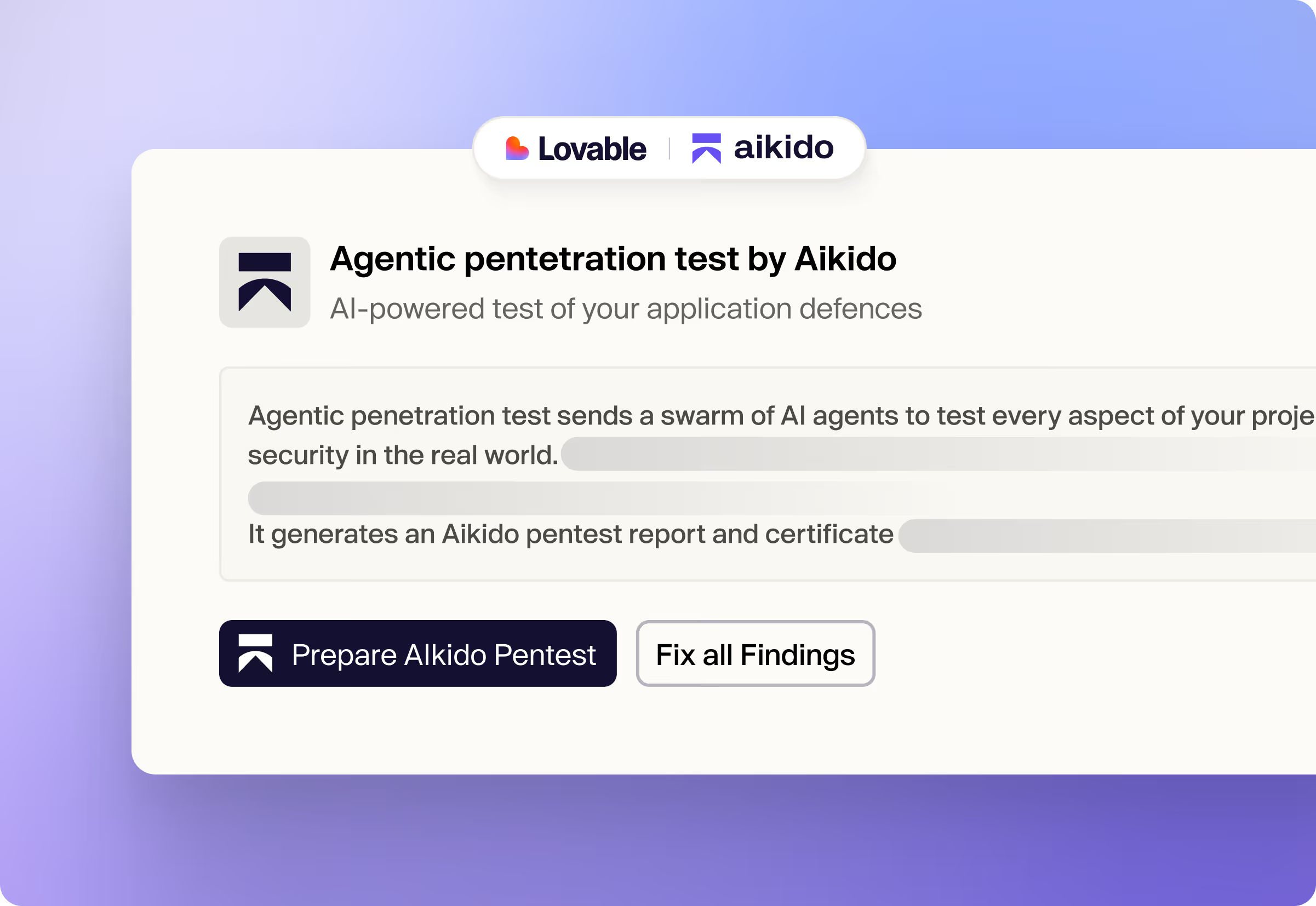
It's a real pentest, not a scan. Aikido deploys AI agents against your live, running application, the same one your users access. They probe login flows, try to access data they shouldn't be able to reach, and attempt to chain smaller weaknesses into bigger breaches. You get findings with full reproduction steps, not just a list of potential issues. Lovable's built-in scanner reviews your code before you publish. Aikido attacks what's actually running after you do.

Quite a lot! Most vulnerabilities in Lovable apps aren't in the code itself. They're in how the application behaves at runtime. Can a logged-in user access another user's data by changing a parameter? Does your API enforce the same rules your UI does? Are your authentication flows as airtight as they look? The pentest tests the running application, not the source code, which is exactly why it catches things a code review misses.

The agents interact with your app the way any user would, through its front end and APIs. One thing worth knowing: because the agents actively probe your app, they may create test data in the process (submitted forms, created accounts, and so on). They don't access your database directly. Findings are stored in your Aikido account and visible only to you.

They cover different moments and different threat models. Lovable's scanner reviews your code before you publish. It catches exposed secrets, misconfigured database policies, and known vulnerability patterns at the source level. Aikido tests your live application after it's running, probing how it actually behaves under attack, not just how it looks on paper. You need both. Code that looks clean can still have logic flaws that only show up when someone tries to break in.

No. Each finding comes with a plain-language explanation of what was found, why it matters, and the exact steps to reproduce it. When you're ready to fix, click Fix all in Lovable and their agent patches the vulnerabilities for you, without leaving your project.
First scan results in under 2 minutes
Connect your repo and see only the vulnerabilities that are actually reachable.

“Aikido’s automation and accuracy help our teams focus on building, not babysitting vulnerabilities.”
















%201.png)