When a new CVE drops, the first question on every developer's mind is: Are we secure? It's an uncomfortable question to sit with. Manually cross-referencing dependencies against the NVD is time-consuming and error-prone, and a CVE may be assigned weeks after a vulnerability is already being exploited in the wild.
The volume of CVEs disclosed every year has increased tremendously. 48,000+ CVEs were published in 2025 alone, or 131 new vulnerabilities a day. AI-assisted research has made finding vulnerabilities easier than ever, but the infrastructure built to catalog and track them was never designed for this kind of volume, and is showing real strain. NIST has shifted to a 'risk-based' prioritization model for the NVD, which, in practice, means a large number of newly published CVEs are sitting unenriched with their backlog status marked as 'not scheduled.' MITRE has faced funding uncertainty. No single database can be trusted to give you complete coverage.
This matters enormously for how you choose a CVE scanner. Tools that rely on a single database inherit its blind spots. Others aggregate across a handful of public databases, some layer in proprietary research, and fewer still can surface threats before a CVE has been assigned at all. As public databases struggle to keep pace, the intelligence behind a scanner matters more than ever.
The best scanners pull from multiple intelligence sources, can surface vulnerabilities before they've been assigned a CVE, use reachability analysis to filter noise, and cover the full stack: code, dependencies, containers, and the supply chain.
What to look for in a CVE scanner
Before diving into the tools, here's what we're measuring and why each criterion matters.
Coverage breadth: What attack surface can a scanner actually see? Network infrastructure, open-source dependencies, containers, IaC, application code? A scanner that can't see part of your stack simply can't protect it.
Intelligence sources: A scanner's findings are only as good as its underlying threat data. When choosing a scanner, it's important to know where the tool's intelligence comes from, how current it is, and whether it can surface vulnerabilities before a CVE has been assigned at all.
Signal-to-noise ratio: A measure of how actionable a scanner's findings are. High false positive rates cause alert fatigue, which can lead to real vulnerabilities getting lost in the noise.
Auto-fix: With the rate of new vulnerability disclosures accelerating, automation is an essential feature for time- and resource-pressed teams. Scanners that can push a fix automatically or open a PR with one click lighten your team's load, helping avoid a backlog of unfixed vulnerabilities.
Best for: No scanner is the right fit for every team. This column cuts through the feature lists to answer a simpler question: given your stack, your workflow, and your security maturity, is this the tool for you?
CVE scanners vary widely in scope, approach, and who they're built for. Some, like Nessus and Qualys VMDR, are designed for enterprise security teams running scheduled infrastructure scans rather than developers working in fast-moving pipelines. Snyk and Semgrep sit closer to the developer workflow, with strong dependency and static analysis coverage, though both come with signal-to-noise tradeoffs at scale. Checkmarx offers broad enterprise AppSec coverage but requires meaningful tuning investment. Aikido leads this list for full stack CVE coverage. It consolidates multiple scan types into one place, and pulls from multiple intelligence sources, including its own pre-CVE feed Aikido Intel, to catch vulnerabilities that never make it into public databases. Reachability analysis surfaces only the vulnerabilities that can actually be exploited in your environment, and AutoFix handles remediation without leaving your workflow.
TL;DR: If you need full-stack CVE scanning in 2026, Aikido Security offers the broadest coverage with intelligence that surfaces vulnerabilities before CVEs are assigned, reachability analysis that cuts noise by over 90%, and AutoFix that turns findings into merged PRs in a single click.
Below, we break down each tool in detail.
Aikido Security
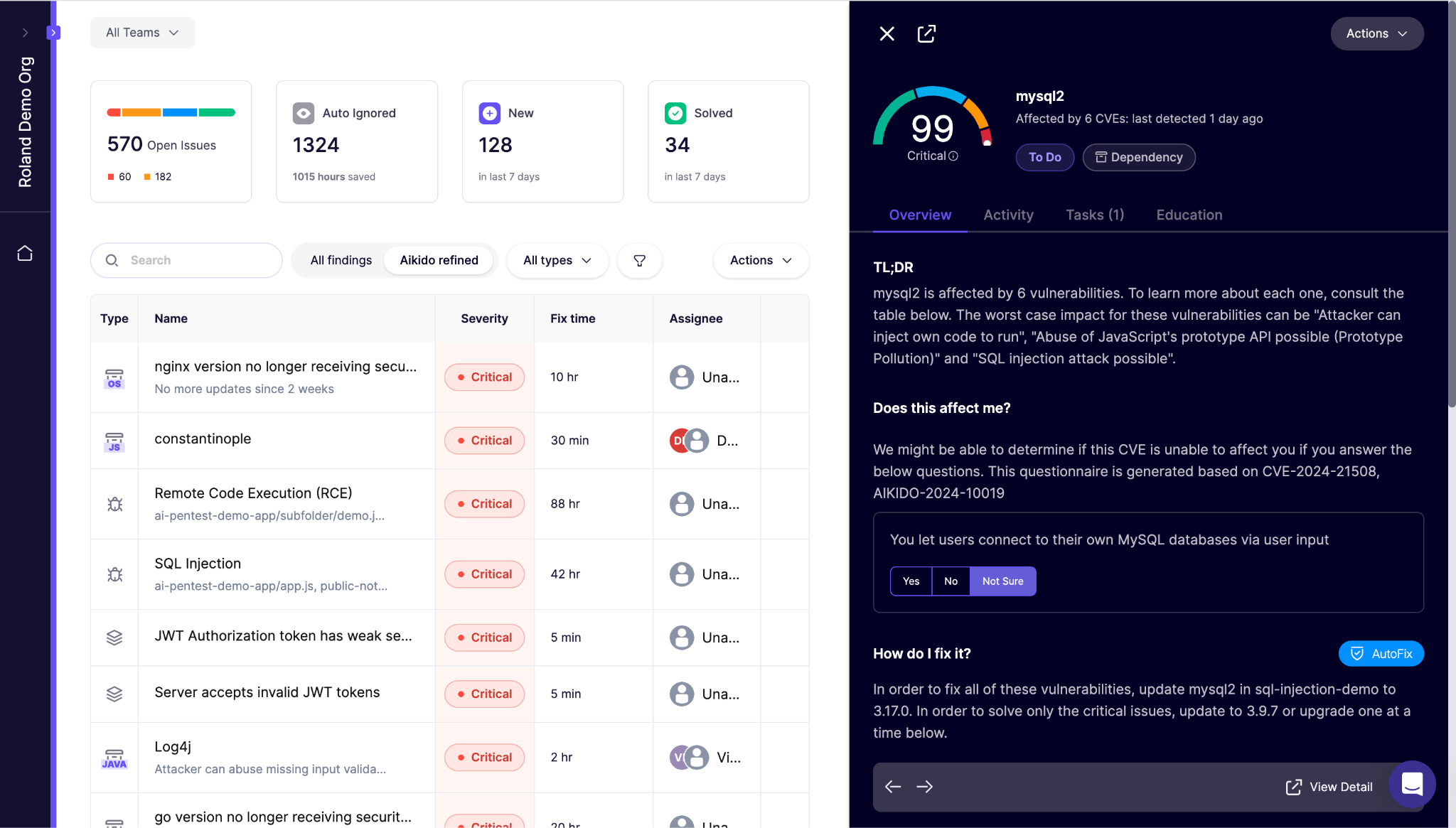
Aikido Security brings code, cloud, and runtime security together in a single platform. Features like reachability analysis that are locked behind enterprise tiers in tools like Snyk are included from the outset, and teams are up and running in minutes with no agents required. Teams using separate AppSec and CloudSec tools are 50% more likely to face incidents, so consolidating in Aikido lowers your risk profile as well as your tooling costs. Aikido Security offers the broadest CVE coverage in this list, including pre-CVE and undisclosed vulnerabilities that other scanners miss entirely.
Coverage breadth
Most teams are duct-taping together four or five tools to get the coverage that Aikido ships out of the box. SCA checks every dependency in your tree against known CVE databases, flagging vulnerable packages, malicious dependencies, and end-of-life runtimes. Aikido’s SAST engine, built on Opengrep and Aikido's proprietary analysis, catches code-level vulnerabilities like SQL injection and XSS with cross-file taint tracking. Container scanning covers OS-level CVEs in your images. Malware detection covers supply chain threats in your dependencies. The result is a single dashboard covering the attack surface most teams need.
Intelligence sources
Aikido pulls from NVD, OSV, GitHub Advisory, and MITRE. But its key differentiator is Aikido Intel: an open-source threat feed that uses custom-trained LLMs to monitor changelogs and release notes across 4.4 million open-source packages, surfacing vulnerabilities before they're assigned a CVE, or ever disclosed at all. Each finding is validated by a human security engineer before release, keeping the feed high-signal rather than noisy. 67% of the vulnerabilities Aikido Intel has discovered were never reported to any public database, meaning scanners relying solely on NVD or GitHub Advisory would miss them entirely. And for those that were eventually disclosed, the average time from patch to CVE assignment was 27 days, meaning scanners relying solely on NVD or GitHub Advisory would miss them entirely, often for weeks.
Signal-to-noise ratio
Aikido separates the findings that actually matter from those that don't with two distinct, layered mechanisms that together cut alerts by over 90%.
Reachability Analysis runs as an initial filter across your findings. Aikido builds a call and dependency graph and traces whether there's an execution path from a real entry point to the vulnerable function. If no such path exists, or if the vulnerable code only runs in tests or build tooling, the finding is suppressed before it ever reaches your queue.
AutoTriage handles whatever reachability doesn't catch. It asks whether exploitability can be ruled out by examining sanitization, input sources, and whether vulnerable code runs in production. For complex cases, it uses reasoning models.
{{false-positives}}
Auto-fix
Aikido's AutoFix generates reviewable code patches for dependencies, first-party code, IaC, containers, and pentest findings, and delivers them as inline IDE suggestions, PR comments, and CI gate feedback. For dependency fixes, AutoFix analyzes your full dependency tree to find the optimal upgrade point, often resolving multiple vulnerable transitive dependencies in a single step. Every generated patch carries a confidence level (High, Medium, or Low), and nothing auto-merges without review unless you explicitly configure it to. Fix it fast, but always know what you're merging.
Best for
Development teams that want full-stack CVE coverage, including dependencies, code, containers, infrastructure, and cloud, without managing multiple tools or suffering from alert fatigue. Especially well-suited to startups and mid-market companies that need to ship fast and can't afford a dedicated AppSec team to manually triage findings. Aikido Security rates 4.9 out of 5 stars on Gartner Peer Insights, with reviewers consistently citing noise reduction and time to value as reasons they switched. Independent research from Latio Pulse found that Aikido has 85% fewer false positives than Snyk, more advanced reachability analysis, and a more intuitive UI, meaning fewer support requests and faster time to resolve. The free tier covers up to 10 repos with no credit card required, and most teams are seeing findings within a minute of connecting their first repo, so there's no reason not to find out what's actually lurking in your stack.
Snyk
Snyk built its reputation as a dependency scanner for developer teams, and that focus shows in the depth of its SCA capabilities. It covers dependencies, code, containers, and IaC, and integrates cleanly into developer workflows. Where it starts to show limitations as a CVE scanner is in noise reduction at scale.
Coverage breadth
Snyk's roots are in open-source dependency scanning, and that's still where it's strongest. Snyk Open Source identifies vulnerable dependencies by scanning package manifests and lockfiles, showing the full dependency path alongside severity, exploit maturity, and fix recommendations. Beyond SCA, the platform covers SAST (Snyk Code), container scanning, IaC, and DAST, making it a broad developer security platform rather than a pure CVE scanner.
Intelligence sources
Snyk Intel is Snyk's proprietary vulnerability database, combining public sources, developer community data, expert research, and machine learning. It pulls from NVD, GitHub Advisory, and npm Advisory alongside findings from its own research team, and actively monitors GitHub issues, PRs, and commit messages for signals of unreported vulnerabilities. The database is researcher-led and broader in scope than pure CVE aggregation.
Signal-to-noise ratio
Reachability analysis is available for SCA, though it is currently only available to a limited set of languages, which can make SCA noise management more manual for polyglot stacks. User reviews for SAST reachability analysis consistently flag false positives in Snyk Code for vulnerabilities that are technically present but unreachable or unexploitable in context.
Auto-fix
For dependency vulnerabilities, Snyk opens full automated PRs with the required upgrades and patches, with customizable PR templates. Fix workflows include auto-retesting and quality checks after generation. On the SAST side, Snyk Code's auto-fix generates fix suggestions using an LLM, then validates them against its own static analysis engine to filter out hallucinations before they reach the developer. Unlike the dependency workflow, it applies fixes via PR inline comments rather than opening standalone fix PRs. But SAST language and framework coverage is still expanding, and auto-fix capabilities lag behind tools that have invested more heavily in AI remediation.
Best for
Teams that primarily need SCA, especially those with heavy open-source usage who want automated fix PRs and smooth IDE integration. For CVE scanning, Snyk is strongest on disclosed dependency vulnerabilities with assigned CVEs, less so on pre-CVE threats or undisclosed issues. Less compelling as a standalone SAST tool. If your stack is dependency-heavy and you want vulnerability fixes landing in your PR queue automatically, Snyk is the natural first look.
Checkmarx
Checkmarx One is built for enterprise AppSec teams that need broad, compliance-grade coverage across the full SDLC. It's a mature platform with deep scanning capabilities, but that maturity comes with complexity. It rewards organizations that have the security engineering resources to configure and maintain it. As a CVE scanner, it covers a wide surface area, including SAST, SCA, IaC, containers, and secrets, with analyst-validated intelligence and a proprietary malicious package database that goes beyond public CVE sources.
Coverage breadth
Checkmarx One covers an extensive range of scan types: SAST, SCA, DAST, container scanning, IaC, API security, and secrets detection, with ASPM layered on top to correlate findings across all engines. The platform includes security checks specifically for AI-generated code entering SDLC at speed. For enterprises that need to show auditors a single-vendor answer to "are we covered?", the coverage map is hard to argue with. The question is whether coverage breadth translates to actual security outcomes or just a longer list of findings to manage.
Intelligence sources
Checkmarx aggregates from multiple vulnerability databases and threat intelligence sources, and layers proprietary research from its Checkmarx Zero security research team on top. The research team operates as a CVE Numbering Authority, meaning they can discover, assign, and disclose new vulnerabilities. Its proprietary malicious package database extends detection beyond formal CVE disclosure into registry-level supply chain threats.
Signal-to-noise ratio
Coverage breadth is a double-edged sword. The more scan types a platform runs, the more findings it generates, and with Checkmarx One, that list can get long fast. ASPM helps by correlating findings across scanning engines using application context, surfacing what's exploitable and actionable rather than a raw list of everything found. Enterprise users report that query customization is important; the ability to account for application-specific patterns, including custom sanitizers, is what keeps false positive rates low at scale. But that tuning takes time and dedicated AppSec resources. Teams without a security engineering function to configure and maintain the rules will struggle with noise at scale.
Auto-fix
Checkmarx One Assist provides AI-assisted remediation. Autonomous agents classify findings by real-world risk and generate reviewable diffs or PRs. Worth noting: the Checkmarx Assist family is powered by technology from Tromzo, which Checkmarx acquired in December 2025. It is listed as an optional add-on rather than included by default across all tiers. Teams evaluating this capability should confirm current availability and tier requirements directly with Checkmarx.
Best for
Enterprise AppSec teams with the resources to tune and manage the platform, especially those in regulated industries that need compliance-grade CVE coverage and a single-vendor answer to auditors. For CVE scanning specifically, Checkmarx One is strongest when paired with dedicated security engineering to configure rules and manage noise. Without that investment, the volume of findings can outpace a team's ability to act on them. Not the right fit for teams looking for a lightweight, out-of-the-box CVE scanner.
Semgrep
Semgrep started as an open-source static analysis engine and has expanded into SCA and secrets detection over time. In the context of CVE scanning, the relevant capability is its SCA engine, Semgrep Supply Chain, which identifies vulnerable open-source dependencies, and filters findings by reachability.
Coverage breadth
Semgrep is a SAST-first tool with SCA and secrets detection added on. Worth noting: in December 2024 Semgrep moved features including fingerprinting, tracking ignores, and key metavariables out of Community Edition, prompting a coalition of 10+ vendors, including Aikido, to fork it as Opengrep in January 2025.
Intelligence sources
Semgrep integrates data from OSV.dev, which aggregates advisories from GitHub Security Lab, OpenSSF, Google's security teams, the PyPI Advisory Database, and the GitHub Security Advisory Database. On top of that, Semgrep monitors external sources including security communities for major incidents and malicious package reports. The underlying vulnerability feeds are drawn from public, community-sourced databases and Semgrep's security team builds proprietary reachability rules on top of them.
Signal-to-noise ratio
Semgrep's own 2022 study of 1,100 repositories found only ~2% of dependency alerts were reachable. However, an academic study applying Semgrep's public PHP ruleset to 300 applications estimated 81% of findings were not exploitable, meaning triage burden remains high unless your team invests heavily in rule tuning.
Auto-fix
Semgrep Autofix (in public beta) can open draft PRs with AI-generated fixes for code findings and trigger dependency-upgrade PRs for supply chain findings. By design, all generated PRs require human review before merging.
Best for
Security engineers running a mature AppSec program who are willing to invest in rule configuration. Not a strong fit for development teams wanting plug-and-play scanning with automated remediation, and any team building on the open-source ecosystem should weigh the risk of further feature restrictions down the road.
Tenable Nessus
Tenable Nessus is one of the most established vulnerability scanners on the market, with a track record built on infrastructure and network coverage rather than application security. As a CVE scanner, it excels at identifying known vulnerabilities across endpoints, network devices and operating systems, but its scope ends at the application layer. Teams looking for open-source dependency coverage will not find it in Nessus specifically.
Coverage breadth
Nessus is a widely-used network and infrastructure vulnerability scanner. Tenable Research has published detection checks covering more than 117,000 CVE IDs. Its focus is the network and infrastructure layer, not application code or dependencies. Container image scanning is handled by Tenable Cloud Security, a separate product, not part of Nessus itself. Organizations with application security needs will quickly run up against its limitations.
Intelligence sources
Tenable's vulnerability database draws primarily on vendor advisories, supplemented by the GitHub Advisory Database and NVD. These sources are aggregated into a proprietary internal Vulnerability Intelligence Database that drives prioritization and detection content. Prioritization is further enriched through Tenable's own Vulnerability Priority Rating, which combines CVSS scores, real-world threat intelligence, and insights from the Tenable Research Team. The intelligence model is built around network, endpoint, and infrastructure CVEs, rather than application-layer or supply chain threats.
Signal-to-noise ratio
Tenable claims approximately 0.32 defects per million scans, a figure it describes as better-than-six-sigma accuracy. In practice, that figure holds best for authenticated scans. Unauthenticated scans produce more false positives and can miss significant portions of internal vulnerabilities. The interface has been described as outdated compared to more modern platforms.
Auto-fix
No native auto-fix. Nessus produces patch guidance in reports, but remediation is manual. Automated patching requires Tenable Patch Management, a separate product built through a partnership with Adaptiva, but it integrates with the broader Tenable Vulnerability Management platform rather than standalone Nessus. Even Nessus's older patch credential integrations are unavailable on Nessus Essentials, Professional, and Expert. Either way, this is an IT ops workflow with no developer-facing remediation path.
Best for
Enterprise IT and security teams running scheduled infrastructure assessments against compliance frameworks like CIS, DISA STIG, HIPAA, and PCI-DSS. If your security needs extend beyond perimeter and endpoint scanning into application code, open source dependencies, container builds, or CI/CD pipelines, Nessus isn't designed to cover that ground.
Qualys VMDR
Qualys VMDR is an enterprise vulnerability management platform built for IT security operations. As a CVE scanner, its strength is the breadth of infrastructure coverage and compliance reporting. For large enterprises that need continuous visibility across complex infrastructure at scale, it's one of the most established options in the market.
Coverage breadth
Qualys VMDR covers asset discovery, continuous scanning, and risk prioritization across on-prem servers, cloud workloads, endpoints, containers, and network infrastructure. Its scope is infrastructure-focused. While SwCA adds runtime scanning of open-source components on deployed assets via the Qualys Cloud Agent, it operates at the production environment level rather than scanning source repositories or integrating into CI/CD pipelines the way developer-native tools do.
Intelligence sources
Qualys VMDR draws from more than 25 threat intelligence feeds, including the CISA Known Exploited Vulnerabilities (KEV) catalog and the MITRE ATT&CK Framework, aggregated through the Qualys Cloud Threat Database and correlated daily with NVD. Prioritization is powered by Qualys TruRisk, which combines feed data with the Qualys Threat Research Unit's own analysis and machine learning to score vulnerabilities by actual risk rather than raw CVSS. Signal-to-noise ratio
Qualys TruRisk claims fewer vulnerabilities to prioritize compared to CVSS-based prioritization alone, but realizing those gains requires significant configuration work. User reviews note that vulnerability identification can result in false positives and inaccuracies. Teams should plan for ongoing governance around asset tagging, ownership, and remediation SLAs to keep results actionable.
Auto-fix
Patch deployment requires a separate Patch Management subscription. There are no PRs opened or code changed, just an IT ops patching workflow.
Best for
Qualys VMDR is best suited for large enterprises managing complex infrastructure, especially in finance, healthcare, and government, where compliance reporting is a core requirement. It's built for IT security operations at scale. If you're an IT security team responsible for endpoint and network CVE management across thousands of assets, it's one of the most established platforms available.
Try the Top-Rated CVE Scanner for Developers
Aikido gives you full-stack CVE coverage (dependencies, code, containers, IaC, secrets, and more) with reachability analysis that cuts noise by over 90% and AutoFix that turns findings into reviewable PRs in a single click. Start for free with up to 10 repos.




