The US government agency NIST’s NVD system never truly recovered from a backlog that began in February 2024. By mid-2024, 75% of submitted CVEs were unprocessed, and in March last year, NIST admitted that a 32% jump in submissions meant the backlog was still growing despite its promise to clear the backlog.
Even before the backlog began, we launched Aikido Intel in January 2024. We believed relying on vulnerability databases alone was no longer sustainable. It was cumbersome and unable to keep pace with the reality of the velocity and volume of open-source security.
Yesterday, the US government agency NIST finally admitted it can’t keep up with the volume of CVE submissions.
Despite a 45% increase in CVEs enriched in 2025, the CVE submissions increased by 263%. There was no way the agency could keep up. Therefore, the agency would have to take on a new, “risk-based” approach to cope.
The new approach will prioritize CVEs for software used within the US government, for critical software, or for those appearing in the Known Exploited Vulnerabilities (KEV) catalog. Other CVEs will be added to NVD, but won’t be analyzed. That means they won’t be independently scoring every CVE. Instead, they’ll just accept the submitter’s score and won’t re-analyze modified CVEs unless someone flags that they should. The growing backlog will move to ‘not scheduled’, which is code for “we might get to it someday (but don’t count on it)”.
Without this enrichment, CVEs will be less up-to-date and less reliable. So what will the impact be on the thousands of organizations and security pros that rely on NVD as their source of truth? If a CVE isn’t enriched by NIST, the tools that rely on NVD won’t surface the CVE. Teams won’t be alerted that something was missed. And the tools themselves will produce false negatives.
So in short, the coverage they’re relying on is no longer complete. And if they continue to rely on NVD as a source of truth, they’re getting a false sense of security.
CVEs were never the full picture anyway
There will, of course, be scrutiny on NIST, but the reality is that even if NVD were running perfectly, teams would miss the majority of real vulnerabilities, because CVEs only cover what gets disclosed.
Maintainers - even of the largest vendors - fix security issues and never report them. Centralized databases alone can’t catch what never gets reported.
This is why we launched Aikido Intel back in January 2024, weeks before NVD’s backlog even started, because we could already see that relying solely on centralized databases to tell you about vulnerabilities was a losing strategy.
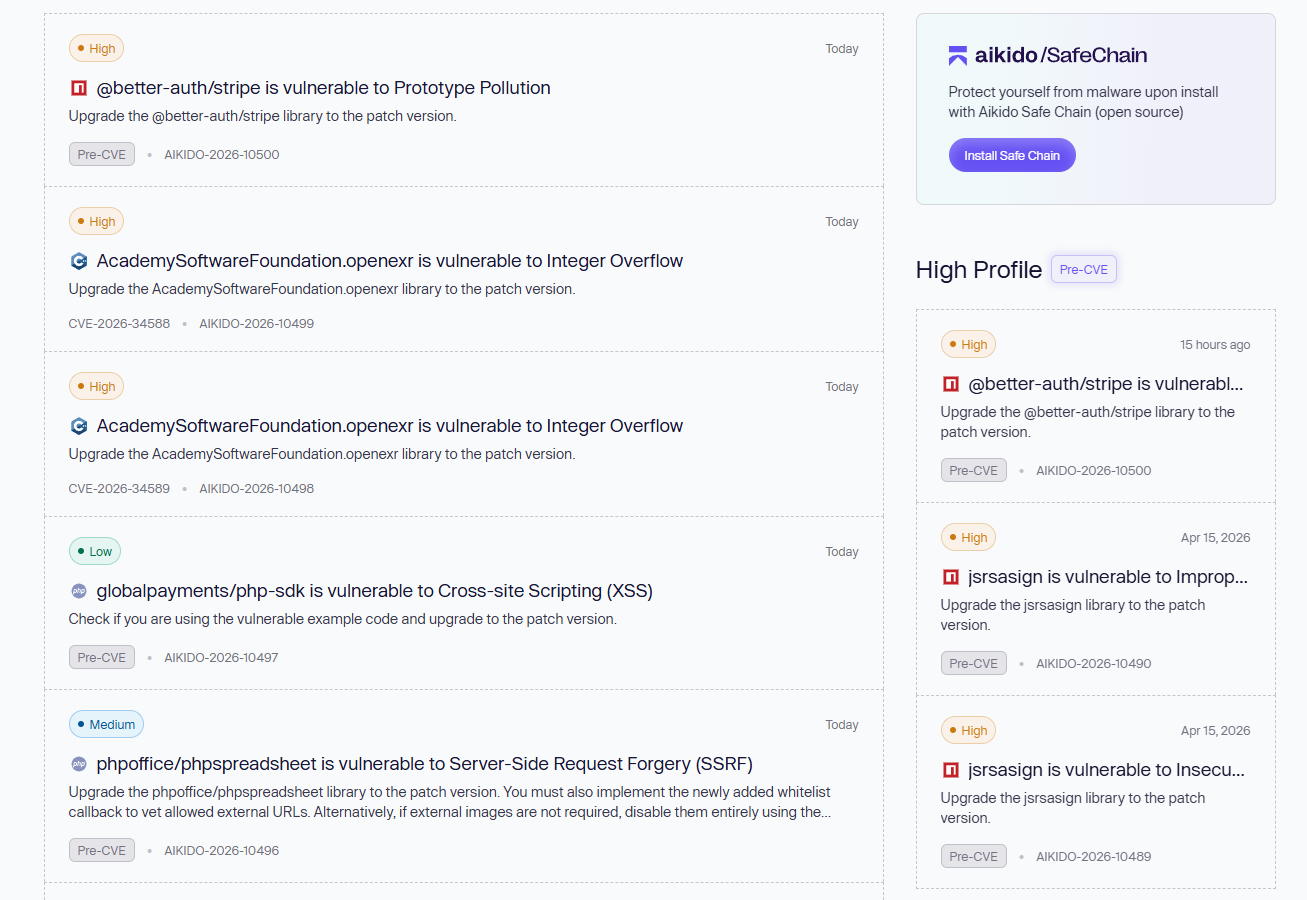
Intel uses custom-trained LLMs to read changelogs, release notes, and commit messages across open-source packages. When it flags security-relevant patches, it checks against five vulnerability databases. If no disclosure exists, our security engineers validate and publish an advisory with an Aikido Vulnerability ID.
To illustrate this point: In its first year, 67% of packages where Intel found vulnerabilities were never publicly disclosed to any database - not NVD, not GitHub Advisory, not MITRE, not anywhere.
And these aren't obscure packages. Axios (56 million weekly npm downloads) silently patched a prototype pollution vulnerability that still has no CVE to this day. Apache ECharts patched a cross-site scripting issue and never disclosed it. Chainlit fixed a critical path traversal vulnerability and said nothing. Of the ones that did eventually get disclosed, the average time from patch to CVE was 27 days. The longest time for disclosure was nine months.
In a single week of Intel monitoring this January, 12 out of 16 flagged vulnerabilities had no CVE assigned at all.
Today, Intel monitors 4.3 million packages and has discovered over 2,000 vulnerabilities. It’s open-source under AGPL, meaning anyone can use it, modify it, and distribute it. It also doesn’t depend on CPE mappings or NVD enrichment to work.
Aikido Intel was already filling this void before it appeared.
So what now?
The EU is already building its own alternative to NVD, the European Vulnerability Database (EUVD), which has been live since May 2025. By September 2026, reporting actively exploited vulnerabilities will become mandatory for manufacturers under the Cyber Resilience Act. The EU saw the risk of depending on a single US-run database and is decoupling as a result. But even the EUVD is in its early stages and relies heavily on synchronizing with NVD and other existing databases. These databases aren’t going away, and they shouldn’t - they serve an important role. But treating any single one as your complete picture is no longer a viable strategy.
The TL;DR is that there is no single source of truth anymore (if there ever really was). NVD is deprioritizing, EUVD is nascent but may go the same way, and other CVE programs, such as MITRE, have had funding scares. Being reliant on one database as a team or for a security tool means you have less coverage and visibility. That era is officially over.
We’ve been building for this moment. Aikido Intel is live, open-source, and scaling. Check it out here.




