The right mindset for any security strategy is to assume you've been breached. It's the principle that underpins zero-trust architecture as defined by NIST. Complex software products are full of potential vulnerabilities, and AI is helping developers ship faster than ever, giving attackers more surface area to work with. The data backs this up. In 2025, 48,000+ CVEs were published, a 20% increase from 2024, itself a record year. Open-source malware detections jumped 73% in 2025. Aikido Intel now analyzes over 100,000 suspicious projects per day, up from 20,000 this time last year.
Attackers only need to find one opening, and the average cost of a data breach hit $4.4 million in 2025. That’s why everything must be systematically stress tested before attackers do it for you.
Penetration testing (pentesting) and red teaming are the two most common ways to perform those stress tests. These terms often get used interchangeably, and they rely on many of the same methodologies, but their scope and purpose are quite different. Both are designed to verify security and uncover issues, but they approach that objective from different angles.
Pentesting asks: what can be exploited? Red teaming asks: could an attacker actually achieve their objective? And would you even notice?
This post breaks down how each works, when to use one over the other, and where AI pentesting is changing the equation.
What is penetration testing?
Penetration testing is a structured security assessment designed to identify vulnerabilities that could be exploited by adversaries within a defined technical architecture, whether that’s a network, cloud environment, or application. Think of it like a locksmith trying the doors and windows in your building before a burglar does.
Unlike Static Application Security Testing (SAST) tools, which scan source code at rest, pentesting finds vulnerabilities that emerge when a system is running, like how a broken access control can lead to exploiting an issue in another system, or how a misconfiguration opens a lateral path. Automated tooling covers ground quickly, while human expertise connects findings into real attack paths.
The level of access and information a tester receives at the outset defines the type of engagement and shapes what it can realistically find. A tester handed the full codebase will find very different things than one sent in with nothing but a domain name. These variations are formalized into three testing modes, white box, grey box, and black box. Each has its own methodology:
The choice of framework follows the same logic. PTES (Penetration Testing Execution Standard) is a general purpose engagement framework that works across all three modes. NIST SP 800-115 is used for compliance-driven white box assessments. The OWASP Testing Guide is used for web application testing. And MITRE ATT&CK is a supplementary knowledge base of adversary tactics and techniques, often used alongside the others. In practice, testers often blend the frameworks depending on what's being tested.
Many compliance frameworks, such as PCI, HIPAA, SOC 2, and more, require penetration testing. Even when it’s not mandatory, security best practices advise running these tests before releasing software, after making changes, and regularly to build resilience.
Increasingly, AI pentesting is handling more of that process than ever before. More on that below.
{{cta}}
What is red teaming?
Red teaming simulates the tactics, techniques, and procedures (TTPs) used during a real cyberattack. Unlike pentesting, the security team (blue team) is not informed about the red team's engagement in order to test how well they perform at detecting and stopping the simulated attacks. Employees are also not informed about how well they hold up against social engineering tactics like phishing.
The goal is to build organizational resilience. Red teaming tests people, processes, and technology together, evaluating how a SOC analyst responds, whether the IR team escalates correctly, and how well communication holds under pressure. It's an organizational assessment that requires human observers, human attackers, and human psychology to be meaningful.
How red teams operate:
- Small teams in specialized roles (e.g., operator, lead)
- Typically black box; no upfront information or access
- Prioritize stealth and adversary emulation over systematic coverage
- Use tools selectively to avoid triggering detection
- Focus on achieving a specific objective (e.g. exfiltrating data, reaching a critical system) rather than cataloging every weakness
Red teaming is most common in larger, more mature organizations where established security programs need to find blind spots and track progress over time.
Penetration testing vs. red teaming: main differences
Comparing penetration testing vs. red teaming head-to-head makes it clear that they’re complementary rather than interchangeable.
The sections below break each dimension down in detail.
Scope
A penetration test will focus exclusively on a defined technical target, such as a network, application, cloud environment, or system, checking it for weaknesses and faults that attackers could exploit. A red team will cover all corners of an organization, from the tech stack to the team members, to assess overall resilience in the face of an attack.
Duration
Traditional penetration tests last anywhere from several days to several weeks, depending on the scope of the test. AI-powered pentests compress that dramatically. Tests will typically happen frequently, in some cases continually, since companies are always expanding or changing their products and infrastructure. Red teaming will run for at least several weeks and potentially several months on an annual basis, though highly sensitive organizations may run more frequent engagements.
Access
Penetration testers receive defined levels of access (white, grey, or black box) depending on the scope and objective of the engagement. Red team engagements will typically be black box (no upfront information or access) to simulate what a real hacker will see and do when orchestrating a compromise.
Objectives
The objective of penetration testing is to find exploitable vulnerabilities so they can be resolved and remediated before attacks target them. By fixing these issues quickly and comprehensively, developers ensure their products meet minimum security standards while making it harder for attackers to gain access or breach assets. The objective of red teaming is to test how well an organization would do against a real-world attack that exploits whatever it can. Red teaming gives the security team valuable practice at detection and response while revealing strengths and weaknesses in the overall security posture.
Output
A penetration test concludes with a detailed report of all the vulnerabilities that were found, the business risks each one poses, and a prioritized list of remediation steps. A red teaming report is more narrative by comparison. It starts with an executive summary, then details the actions taken by the red team, followed by the response they encountered and the malicious outcomes they were able to achieve. It breaks down the business risk of each successful action and recommends remediation steps to prevent a repeat result.
KPIs
Successful penetration tests are measured by the percentage of in‑scope attack surfaces tested, the rate of vulnerability and false positive discovery, alignment with regulatory requirements, and MTTR. Rather than quantifying the number of issues discovered, red teaming success is measured by the strength of defenses through metrics like time-to-detection, time-to-containment, and time-to-eviction.
Typically used by
Penetration testing is used across organizations of all sizes. Red teaming is most common in larger, more mature organizations where an established security program needs to find blind spots and track progress over time. It requires a well-resourced security team substantial enough to meaningfully test detection and response.
When to use penetration testing vs. red teaming
Use penetration testing when:
- Compliance requires it (PCI DSS, HIPAA, SOC 2 strongly require or expect at least annual testing)
- Launching a new product or feature
- After significant infrastructure changes
- You need continuous coverage as your codebase evolves
Use red teaming when:
- Your security program has reached maturity and you need to find blind spots
- The SOC or IR team needs to test real-world readiness
- You need executive-level assurance on organizational resilience
- You're in a sensitive industry (finance, healthcare, critical infrastructure) with elevated threat exposure
- You want to test whether your defenses would catch a real APT-style attack
How does AI pentesting fit in?
AI pentesting vs manual pentesting
Increasingly, AI pentesting can be used to replace manual pentesting. In a head-to-head benchmark across four production web applications, Aikido's autonomous AI pentesting completed each test in hours, while manual testers took up to four weeks from start to finish. Additionally, the AI surfaced deeper application-logic vulnerabilities like IDORs, authentication bypasses, and e-signature forgery that human testers missed.
The structural reason is access asymmetry. Greybox testing is the norm for humans because reviewing a full codebase is prohibitively expensive. AI doesn't have that constraint. Source code access is instant, so AI operates at whitebox depth while humans are stuck at greybox by default.
AI pentesting for red teaming
Continuous AI pentesting is a perfect complement to red teams. 79% of CISOs and engineering leaders say issues go undetected between scheduled penetration tests, and continuous AI pentesting handles that surface drift automatically. That frees red teams from making the tradeoff between coverage and depth, so they can focus on the crown jewels.
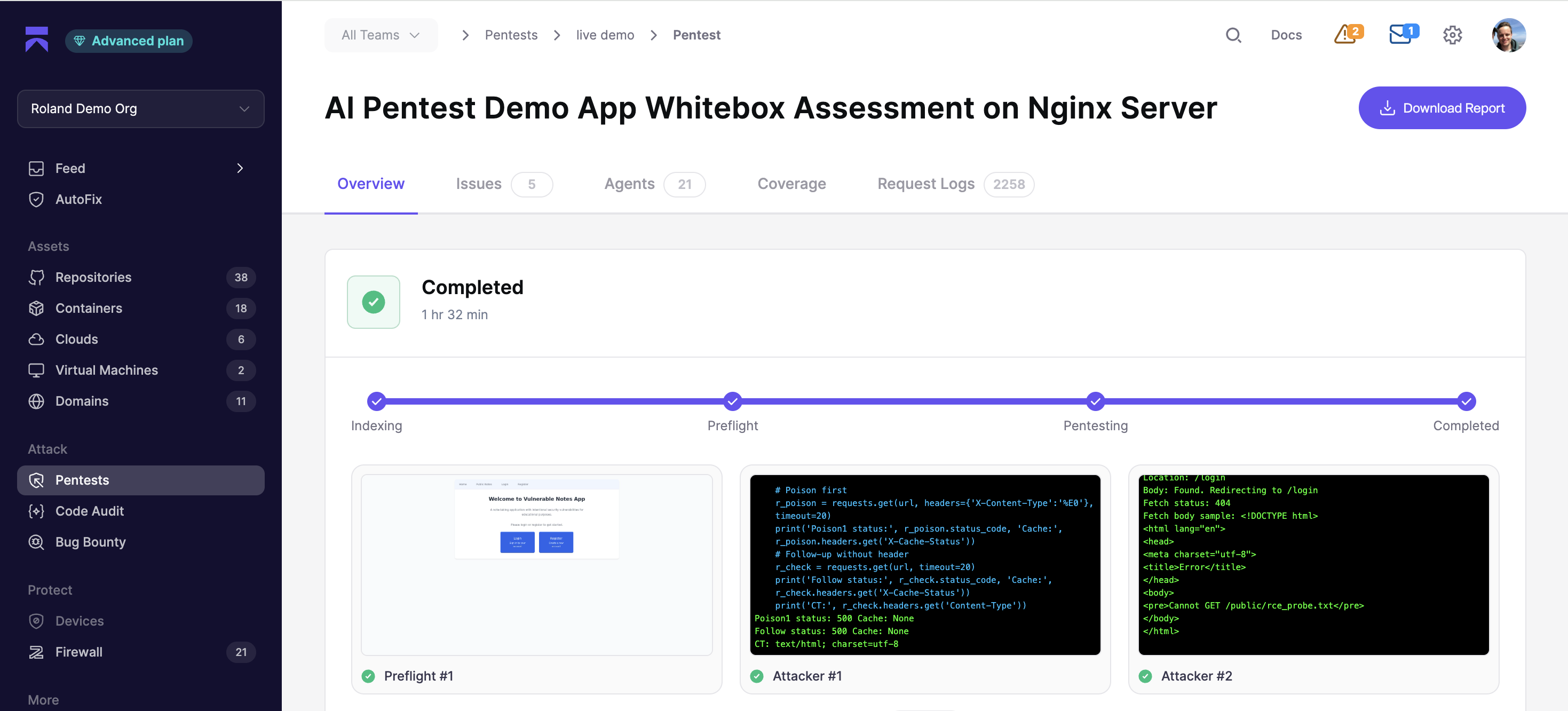
Aikido Security exemplifies the potential of AI-driven pentesting. Agentic AI trained to follow industry-standard frameworks operates by default at whitebox depth, with grey and black box modes also available. Additional validation prevents false positives and hallucinations. Each result, along with the agent behavior and root cause, is explained in detail before being remediated automatically and retested to confirm the fix. Tests finish in hours instead of days, and produce audit-ready reports mapped to SOC 2, ISO 27001, and other compliance frameworks.
Start with pentesting, grow into red teaming
As a simple rule of thumb, penetration testing evaluates products, and red teaming evaluates organizations. They’re both trying to “break in,” but the motives and methods are different.
Most companies start with penetration testing, increase cadence as they grow, and eventually add red teaming once the security program is mature enough to benefit from it. Because if they don’t hunt down vulnerabilities, attackers will.
{{pentest}}
FAQ
<script type="application/ld+json">
{
"@context": "https://schema.org",
"@graph": [
{
"@type": "TechArticle",
"@id": "https://www.aikido.dev/blog/penetration-testing-vs-red-teaming#article",
"headline": "Penetration Testing vs. Red Teaming: What's the Difference?",
"description": "Penetration testing and red teaming are both ways to stress test your security, but they're not the same thing. This post breaks down how each works, when to use one over the other, and where AI pentesting is changing the equation.",
"url": "https://www.aikido.dev/blog/penetration-testing-vs-red-teaming",
"datePublished": "2025-05-15",
"dateModified": "2025-05-15",
"inLanguage": "en-US",
"mainEntityOfPage": {
"@type": "WebPage",
"@id": "https://www.aikido.dev/blog/penetration-testing-vs-red-teaming"
},
"author": {
"@type": "Person",
"@id": "https://www.aikido.dev/authors/nicholas-thomson",
"name": "Nicholas Thomson",
"jobTitle": "Senior SEO & Growth Lead",
"url": "https://www.aikido.dev/authors/nicholas-thomson",
"sameAs": [
"https://www.linkedin.com/",
"https://x.com/"
],
"worksFor": {
"@type": "Organization",
"name": "Aikido Security",
"url": "https://www.aikido.dev"
}
},
"publisher": {
"@type": "Organization",
"@id": "https://www.aikido.dev#organization",
"name": "Aikido Security",
"url": "https://www.aikido.dev",
"logo": {
"@type": "ImageObject",
"url": "https://www.aikido.dev/logo.png"
}
},
"image": {
"@type": "ImageObject",
"url": "https://www.aikido.dev/og/penetration-testing-vs-red-teaming.png",
"width": 1200,
"height": 630
},
"keywords": [
"penetration testing",
"red teaming",
"AI pentesting",
"ethical hacking",
"vulnerability assessment",
"OWASP",
"NIST SP 800-115",
"PTES",
"MITRE ATT&CK",
"OSSTMM",
"blue team",
"SOC",
"incident response",
"CVE",
"broken access control",
"security misconfiguration",
"white box testing",
"grey box testing",
"black box testing",
"continuous pentesting",
"PTaaS",
"zero trust",
"APT",
"PCI DSS",
"HIPAA",
"SOC 2",
"DORA",
"time-to-detection",
"IDOR",
"authentication bypass",
"access asymmetry"
],
"about": [
{
"@type": "DefinedTerm",
"name": "Penetration Testing",
"description": "A structured security assessment designed to identify vulnerabilities that could be exploited by adversaries within a defined technical architecture."
},
{
"@type": "DefinedTerm",
"name": "Red Teaming",
"description": "A simulation of real-world cyberattacks using adversary tactics, techniques, and procedures to test an organization's detection and response capabilities."
},
{
"@type": "DefinedTerm",
"name": "AI Pentesting",
"description": "Autonomous AI-driven penetration testing that operates at whitebox depth by default, completing assessments in hours rather than weeks."
}
],
"mentions": [
{"@type": "Thing", "name": "OWASP Top 10", "url": "https://owasp.org/www-project-top-ten/"},
{"@type": "Thing", "name": "NIST SP 800-115", "url": "https://csrc.nist.gov/publications/detail/sp/800-115/final"},
{"@type": "Thing", "name": "MITRE ATT&CK", "url": "https://attack.mitre.org/"},
{"@type": "Thing", "name": "PTES", "url": "http://www.pentest-standard.org/index.php/Main_Page"},
{"@type": "Thing", "name": "OSSTMM"},
{"@type": "Thing", "name": "PCI DSS"},
{"@type": "Thing", "name": "HIPAA"},
{"@type": "Thing", "name": "SOC 2"},
{"@type": "Thing", "name": "DORA"},
{"@type": "Thing", "name": "NIST Zero Trust Architecture", "url": "https://nvlpubs.nist.gov/nistpubs/specialpublications/NIST.SP.800-207.pdf"},
{"@type": "SoftwareApplication", "name": "Aikido Attack", "url": "https://www.aikido.dev/attack/aipentest"},
{"@type": "SoftwareApplication", "name": "Aikido Infinite", "url": "https://www.aikido.dev/attack/infinite"},
{"@type": "SoftwareApplication", "name": "Aikido Intel", "url": "https://intel.aikido.dev/"}
],
"speakable": {
"@type": "SpeakableSpecification",
"cssSelector": ["h1", "h2", ".article-summary"]
},
"timeRequired": "PT10M",
"articleSection": "Security Testing",
"citation": [
{
"@type": "CreativeWork",
"name": "Autonomous vs. Manual Pentesting Benchmark",
"url": "https://www.aikido.dev/reports/autonomous-vs-manual-pentesting-benchmark"
},
{
"@type": "CreativeWork",
"name": "Continuous Pentesting: How It Works and What It Requires",
"url": "https://www.aikido.dev/blog/continuous-pentesting-requirements"
},
{
"@type": "CreativeWork",
"name": "OWASP Top 10 2025",
"url": "https://owasp.org/www-project-top-ten/"
},
{
"@type": "CreativeWork",
"name": "NIST SP 800-207 Zero Trust Architecture",
"url": "https://nvlpubs.nist.gov/nistpubs/specialpublications/NIST.SP.800-207.pdf"
}
]
},
{
"@type": "WebPage",
"@id": "https://www.aikido.dev/blog/penetration-testing-vs-red-teaming",
"url": "https://www.aikido.dev/blog/penetration-testing-vs-red-teaming",
"name": "Penetration Testing vs. Red Teaming: What's the Difference?",
"isPartOf": {
"@type": "WebSite",
"url": "https://www.aikido.dev",
"name": "Aikido Security"
},
"primaryImageOfPage": {
"@type": "ImageObject",
"url": "https://www.aikido.dev/og/penetration-testing-vs-red-teaming.png"
},
"breadcrumb": {
"@id": "https://www.aikido.dev/blog/penetration-testing-vs-red-teaming#breadcrumb"
}
},
{
"@type": "BreadcrumbList",
"@id": "https://www.aikido.dev/blog/penetration-testing-vs-red-teaming#breadcrumb",
"itemListElement": [
{
"@type": "ListItem",
"position": 1,
"name": "Home",
"item": "https://www.aikido.dev"
},
{
"@type": "ListItem",
"position": 2,
"name": "Blog",
"item": "https://www.aikido.dev/blog"
},
{
"@type": "ListItem",
"position": 3,
"name": "Penetration Testing vs. Red Teaming: What's the Difference?",
"item": "https://www.aikido.dev/blog/penetration-testing-vs-red-teaming"
}
]
},
{
"@type": "FAQPage",
"@id": "https://www.aikido.dev/blog/penetration-testing-vs-red-teaming#faq",
"mainEntity": [
{
"@type": "Question",
"name": "What is the difference between penetration testing and red teaming?",
"acceptedAnswer": {
"@type": "Answer",
"text": "Penetration testing identifies exploitable vulnerabilities in a specific technical target, such as an app, network, or cloud environment. Red teaming simulates a full real-world attack against an entire organization, including its people and processes, to test detection and response. Pentesting finds holes; red teaming tests whether anyone would notice them being used."
}
},
{
"@type": "Question",
"name": "Can penetration testing and red teaming be done at the same time?",
"acceptedAnswer": {
"@type": "Answer",
"text": "Not effectively. Red teaming requires the security team to be unaware of the engagement to produce meaningful results. Running a pentest simultaneously would contaminate the environment and skew how defenders respond."
}
},
{
"@type": "Question",
"name": "How often should you run a penetration test?",
"acceptedAnswer": {
"@type": "Answer",
"text": "Most compliance frameworks require at least annual penetration testing, but modern security teams run them more frequently: before major releases, after significant infrastructure changes, and continuously via AI-powered pentesting tools."
}
},
{
"@type": "Question",
"name": "Is red teaming required for compliance?",
"acceptedAnswer": {
"@type": "Answer",
"text": "Generally no, though requirements are growing. Frameworks like DORA are increasingly referencing adversarial simulation. Most organizations adopt red teaming voluntarily once their security program reaches sufficient maturity."
}
},
{
"@type": "Question",
"name": "What qualifications should a penetration tester have?",
"acceptedAnswer": {
"@type": "Answer",
"text": "Look for certifications like OSCP (Offensive Security Certified Professional), CEH (Certified Ethical Hacker), or GPEN (GIAC Penetration Tester)."
}
},
{
"@type": "Question",
"name": "Can AI replace human penetration testers?",
"acceptedAnswer": {
"@type": "Answer",
"text": "For manual pentesting, yes. AI agents already outperform human testers on speed, coverage, and depth of logic flaw detection. For red teams, the better frame is complementary. Continuous AI pentesting can take care of surface drift so experienced offensive teams can focus on the crown jewels."
}
}
]
},
{
"@type": "Organization",
"@id": "https://www.aikido.dev#organization",
"name": "Aikido Security",
"url": "https://www.aikido.dev",
"logo": {
"@type": "ImageObject",
"url": "https://www.aikido.dev/logo.png"
},
"sameAs": [
"https://www.linkedin.com/company/aikido-security",
"https://x.com/aikido_security",
"https://github.com/AikidoSec"
]
}
]
}
</script>




