→ TL;DR Developer devices are the new Achilles' heel of the software supply chain. Aikido Device Protection protects devices from installing attacks across package registries, IDE extensions, browser plug-ins, and skills marketplaces. Build fearlessly.
Things have been pretty crazy lately, huh?
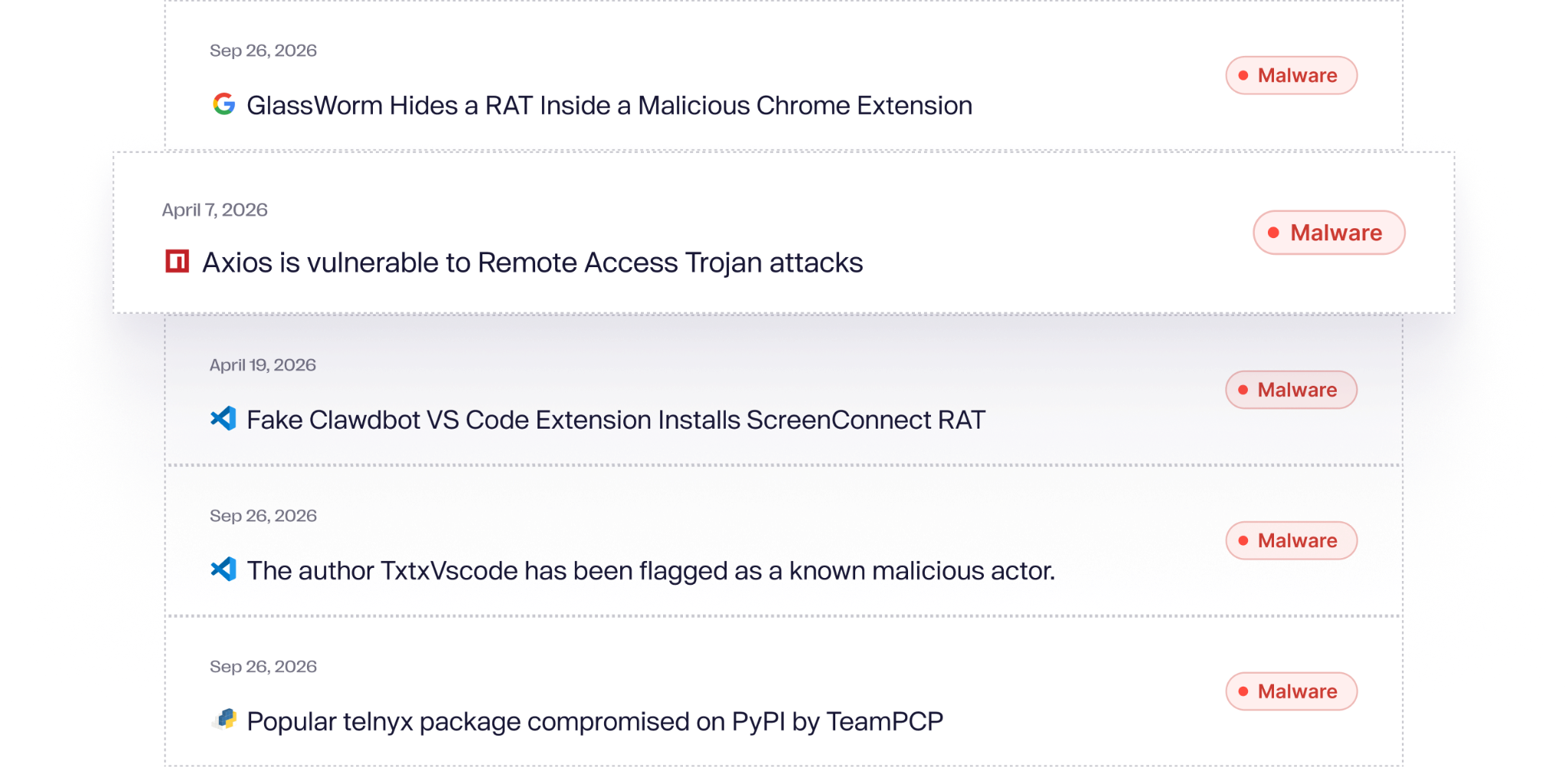
In March alone, TeamPCP chained stolen credentials across four major open source projects in under ten days: Trivy, Checkmarx KICS, LiteLLM, and Telnyx. Days later, Axios, the JavaScript HTTP client with over 100 million weekly downloads, was compromised through a hijacked maintainer account. This week, Vercel disclosed that an attacker accessed internal systems and environment variables after likely compromising a Chrome extension used by one of its employees.
Keeping up with security recently feels like a long, long week:

And if you’re feeling left out, hang tight.

In twelve months, we went from single-package compromises to self-replicating worms to full CI/CD pipeline hijacks chaining across registries. The attackers are learning faster than we're shipping fixes.
“Writing a supply chain attack used to require real skill. You needed to understand package registries, CI/CD pipelines, obfuscation techniques, and how to write payloads that evade detection. Now you need an $8 ChatGPT subscription. You don't even need to understand what npm is to write malware that spreads through it.
Ask a model to write a postinstall hook that exfiltrates environment variables, and it will. Ask it to obfuscate the payload, and it will. The offense got democratized. The defense has gotten better, but not at the same pace.”
On the other side, AI coding agents are pulling packages, invoking tools, and adding skills autonomously, with little-to-no human oversight over what gets installed. Where is this all heading?
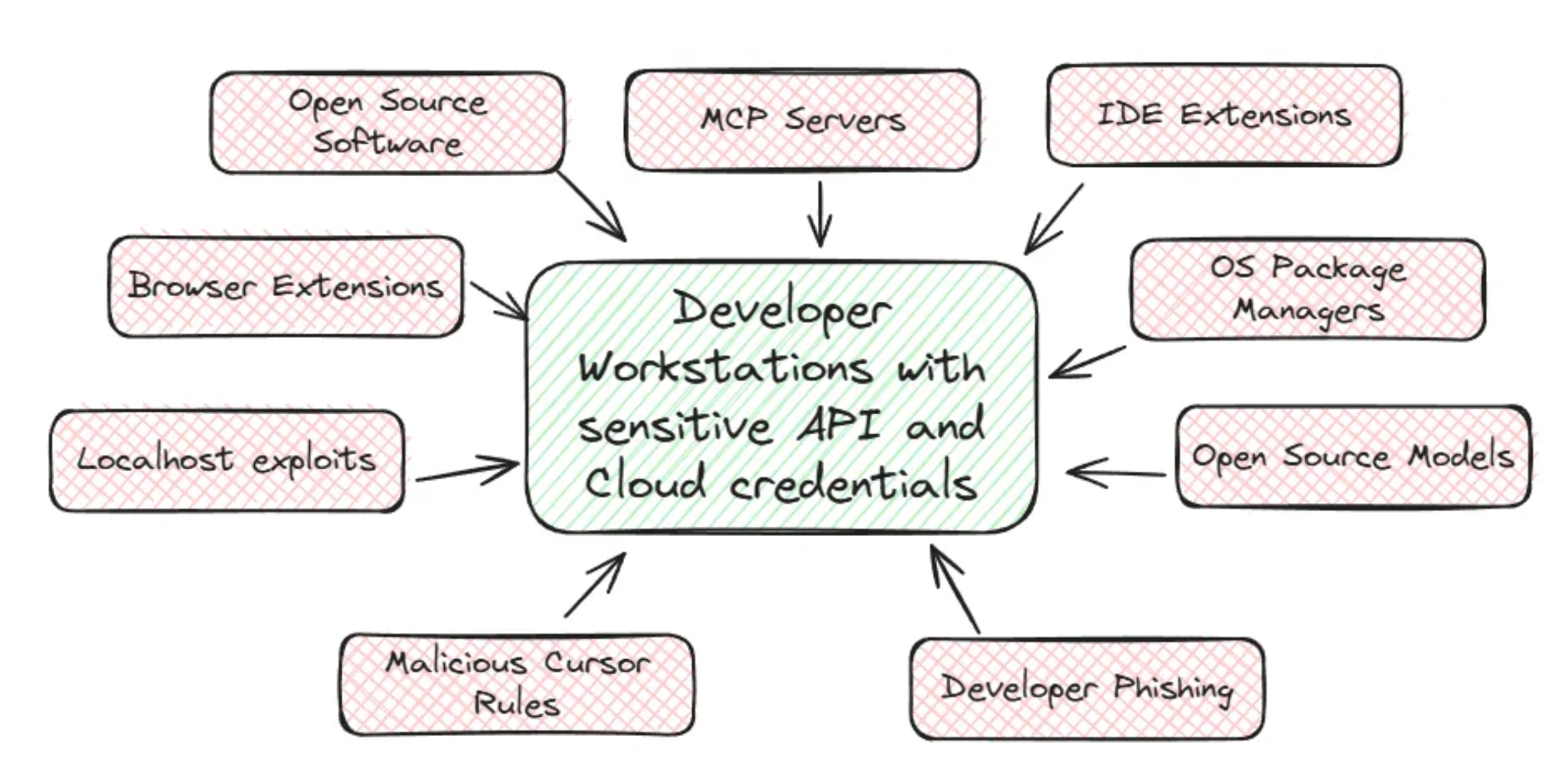
The new endpoint: developer devices
These attacks all share the same target: the developer device itself. Why?
Developer devices are trusted environments that hold the keys to the castle: cloud credentials, SSH keys, npm publish tokens, Kubernetes configs, direct access to source code, and production. Compromise one, and the blast radius is enormous. A single compromised credential has been enough to publish malicious versions of legitimate packages, triggering compromises across thousands of organizations.
So aren’t developer devices protected by existing tools? No. That’s the thing. The security tools most companies rely on, traditional endpoint protection (EDR) for detecting threats on the operating system and device management (MDM) for managing what gets installed, were built for a world of signed binaries and operating system attacks. And they definitely weren’t built for today’s developers.
The software being installed on developer machines today is code packages, IDE extensions, browser extensions, AI tools, and MCP servers. Plaintext, uncompiled software. EDR doesn't see npm install. MDM doesn't know what an MCP extension does.
Developer devices are the new Achilles' heel of the software supply chain.
The status quo doesn't work
Without tooling that covers the developer endpoint, most companies end up in one of two bad positions.
- They block everything. No installs. Private registries, iron walls between developers and the open internet. Might work for highly regulated enterprises like banks, but kills speed everywhere else. It's so restrictive that developers fight for wide exemptions or find workarounds, like second laptops and disabled VPNs, which makes the problem worse.
- They allow and pray. No effective method to govern what developers install, so they hope nothing goes wrong, relying on rotating secrets and minimum access policies. This is how most companies operate.
Or they do some combination of the two, with manual case-by-case review. It doesn't scale (obviously). None of these work.
“In the business world, developer productivity outranks every other concern, and typically these machines are given wide exemptions to the normal controls, creating a massive blind spots in organizations…or the juice just is not worth the squeeze to prevent potential exploits, especially knowing the developer backlash that would inevitably come.” (James Berthoty)
Companies can't afford to slow development down, and they can't afford to leave it unprotected anymore either. So we built Aikido Device Protection.
Introducing Aikido Device Protection
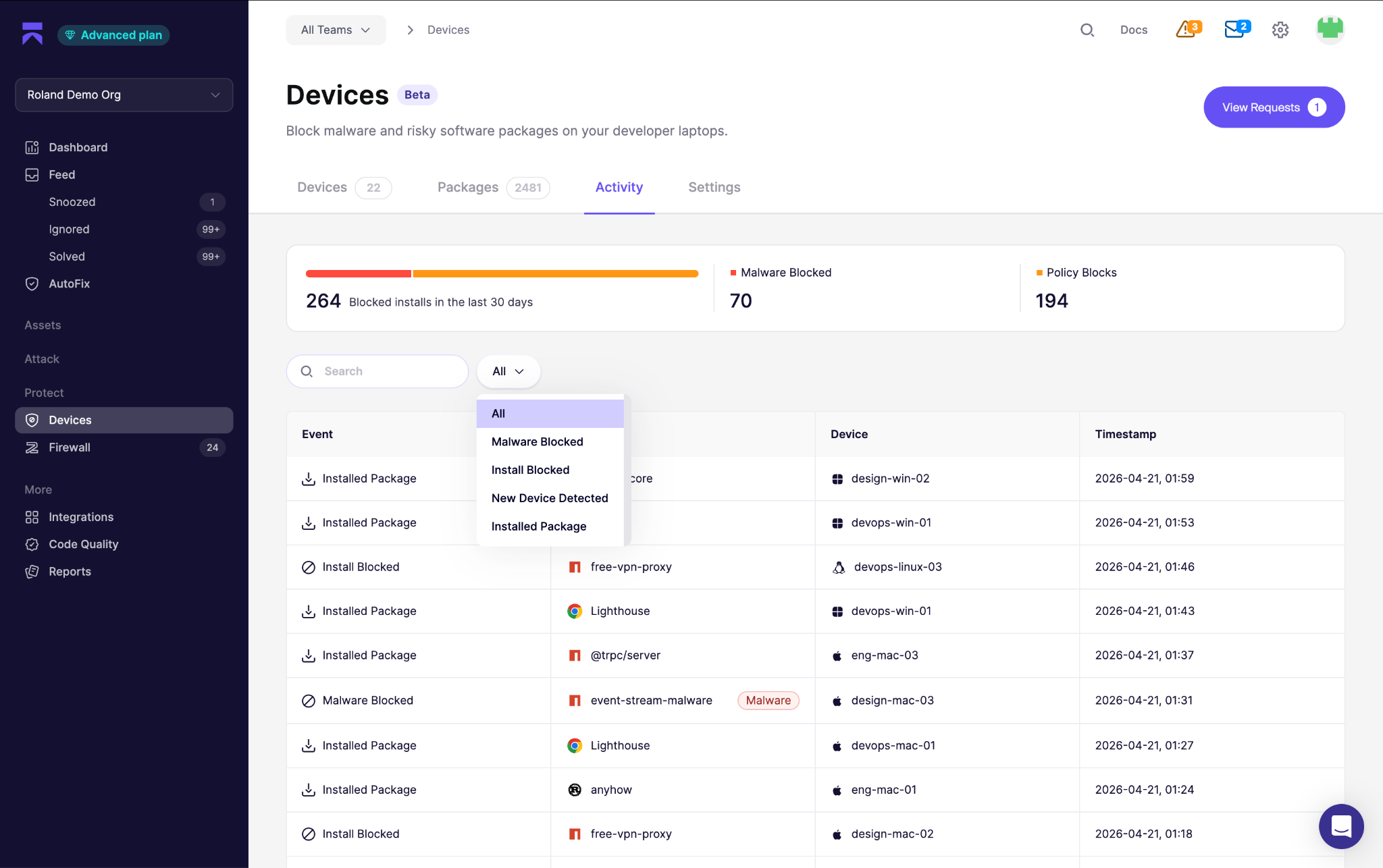
Aikido Device Protection is the security layer that sits on the developer device, giving you visibility, control, and protection over what is installed on your engineer’s workstations.
With Aikido Device Protection, teams can:
- Get full visibility into your software supply chain: See every browser extension, code library, IDE plugin, and build dependency installed across your team's devices.
- Stop malware before it gets installed: Aikido automatically identifies malicious packages and installs, blocking them before they reach the device
- Enforce minimum package age: Set your own requirements for package maturity before usage, minimize risk windows
- Lock down specific ecosystems: Block all installs from any ecosystem and marketplace when your team doesn't need them.
- Require approval for new software: Let team members request installs while keeping admins in control of what gets approved, set team policies, exceptions, and workflows.
In practice, this looks like:
A developer installs a VS Code extension that looks legitimate, works as advertised, and silently drops a remote access trojan on launch. Device Protection checks it against Aikido Intel's threat feed and blocks it before it activates. We found exactly this in January with a fake Clawdbot extension.
A developer runs npm i axios, which tries to pull the latest version. That version was published an hour ago. Device Protection falls back to the most recent version that satisfies a 48-hour minimum age policy. In the Axios attack, the malicious dropper dependency was pre-staged less than 24 hours before the compromised versions pulled it in. The age check alone would have blocked infection.
Throughout all our products, we remain ruthlessly loyal to getting developers back to building. For devs, Aikido Device Protection is designed to disappear. Build with freedom. Safe installs go through without interruption. If something is malicious, it gets blocked before it touches the machine. If you forget it’s running, that's the point. [...Insert cliche metaphor about how you’re glad you wear a helmet the day you get into an accident]
For security teams, Aikido Device protection is designed to give you visibility and control, without slowing down development. Set your own team policies, allow lists for known-good tooling, request-and-approval workflows, get a full audit trail, and visibility across every developer device in the organization. Deploy easily through your existing MDM.
Built on open foundations
Last year we released Safe Chain, an open source proxy server that wraps the CLI, blocking malicious packages before install, and enforcing a 48 hour minimum package age. With over 200,000 weekly downloads, Safe Chain provides a protection to individual developers and enterprise teams alike. If you were running Safe Chain, the Shai-Hulud, TeamPCP, and Axios attacks were blocked.
Safe Chain is the starter pack. We will continue to invest in the project. It will remain open source. Device Protection is the evolution, with extended sources, ease-of-deployment, governance controls, and central dashboard.
Both Safe Chain and Device Protection run on Aikido Intel, our LLM-based threat intelligence engine. Aikido Intel monitors the open internet, exposing malware and pre-CVE vulnerabilities in open-source ecosystems as they’re detected. For malware specifically, Aikido Intel now analyzes 100,000+ suspicious projects per day, up from 20,000 this time last year, identifying malware within minutes of publication.
Aikido Intel is supported by a dedicated team of security researchers and AI engineers. We publicize all of the threat findings automatically, making Aikido Intel your earliest warning for supply chain threats. Free. Open. → https://intel.aikido.dev/
Get started (yes, there’s a free tier)
Aikido Device Protection is available on all plans. npm and PyPI protection is included free.
For custom policies, approval workflows, VS Code extension monitoring, browser plug-in monitoring, and additional ecosystems, an additional subscription per device applies.
To see how Device Protection can protect your devs, book a demo, start free or join our live demo this Thursday at 9AM PT.
Build fearlessly
This year has been rough, or as Charlie poetically (albeit darkly) puts it, "Right now, our supply chains aren't chains at all. They're loose threads, and they're unraveling."
Device Protection helps tie down those loose threads. Discover your risk. Prevent attacks. Most importantly, enable developers to build without interruption…and without fear.
- Madeline, Aikido
P.S While “build fearlessly” veers dangerously close to an embroidered “live, laugh, love” couch pillow that I’d burn on sight… it works. It’s snappy.
I have free will and executive power. Today, I’m using both. Tagline = decided.




