You want to secure your application. The best place to start is the Open Worldwide Application Security Project's (OWASP) Top 10. As security expert and educator Tanya Janca describes it on the Secure Disclosure Podcast: "It's the most popular project that OWASP does internationally, a list of the top 10 risks for web applications." Published every four years, it's the definitive benchmark security teams worldwide use to prioritize their defenses. These are the weaknesses attackers exploit most. Leave one undetected, and you've handed attackers a working invitation.
The problem is that most scanners don't actually cover all of them. Some only test a running application and miss everything lurking in your source code. Others only scan dependencies and overlook your infrastructure. Many generate so much noise that real issues get buried. Having a scanner doesn't necessarily mean you're covered.
76% of organizations deploy significant updates weekly or faster, and 39% deploy daily. More code shipping faster means more attack surface, and attackers are keeping pace. The right OWASP scanner keeps you ahead of them. Not all scanners are built the same, and the differences matter. This guide breaks down the top OWASP scanners on the market so you can choose one confidently.
What are the OWASP top 10 vulnerabilities?
Here's OWASP's 2025 list of the ten most critical web application security risks:
- A01: Broken Access Control
- A02: Security Misconfiguration
- A03: Software Supply Chain Failures
- A04: Cryptographic Failures
- A05: Injection
- A06: Insecure Design
- A07: Authentication Failures
- A08: Software or Data Integrity Failures
- A09: Security Logging and Alerting Failures
- A10: Mishandling of Exceptional Conditions
How do OWASP scanners work?
Most scanners don't cover the full OWASP top 10 with a single tool. They combine several methods to get there, each targeting a different slice of the vulnerability surface. Before committing to a scanner, it's worth understanding which tools it actually includes, and what each one covers:
- Static Application Security Testing (SAST) analyzes source code before anything ever runs, helping detect Injection (A05), Cryptographic Failures (A04), Insecure Design (A06), Authentication Failures (A07), and Software and Data Integrity Failures (A08)
- Software Composition Analysis (SCA) scans third-party dependencies for known vulnerabilities and malicious packages, directly targeting Software Supply Chain Failures (A03).
- Dynamic Application Security Testing (DAST) tests the running application for vulnerabilities that only surface at runtime, covering Broken Access Control (A01), Security Misconfiguration (A02), and Injection (A05) in ways that complement what SAST catches at the code level.
- Infrastructure as Code (IaC) scanning checks infrastructure configuration files for misconfigurations before deployment, targeting Security Misconfiguration (A02).
- Secrets scanning finds hardcoded credentials and exposed API keys in your codebase, addressing a root cause of Authentication Failures (A07) and Software Supply Chain Failures (A03).
- Pentesting validates real attack paths against your running application, confirming which vulnerabilities across all ten categories are actually exploitable rather than just theoretically present.
- Security Logging (A09) and Mishandling of Exceptional Conditions (A10) are partially covered by SAST, which can detect insufficient logging practices and poor error handling at the code level. Full coverage also benefits from runtime protection tools, and in some cases manual review.
With a clear understanding of what best-in-class scanners offer, let’s explore how some of the leading vendors compare.
Aikido Security
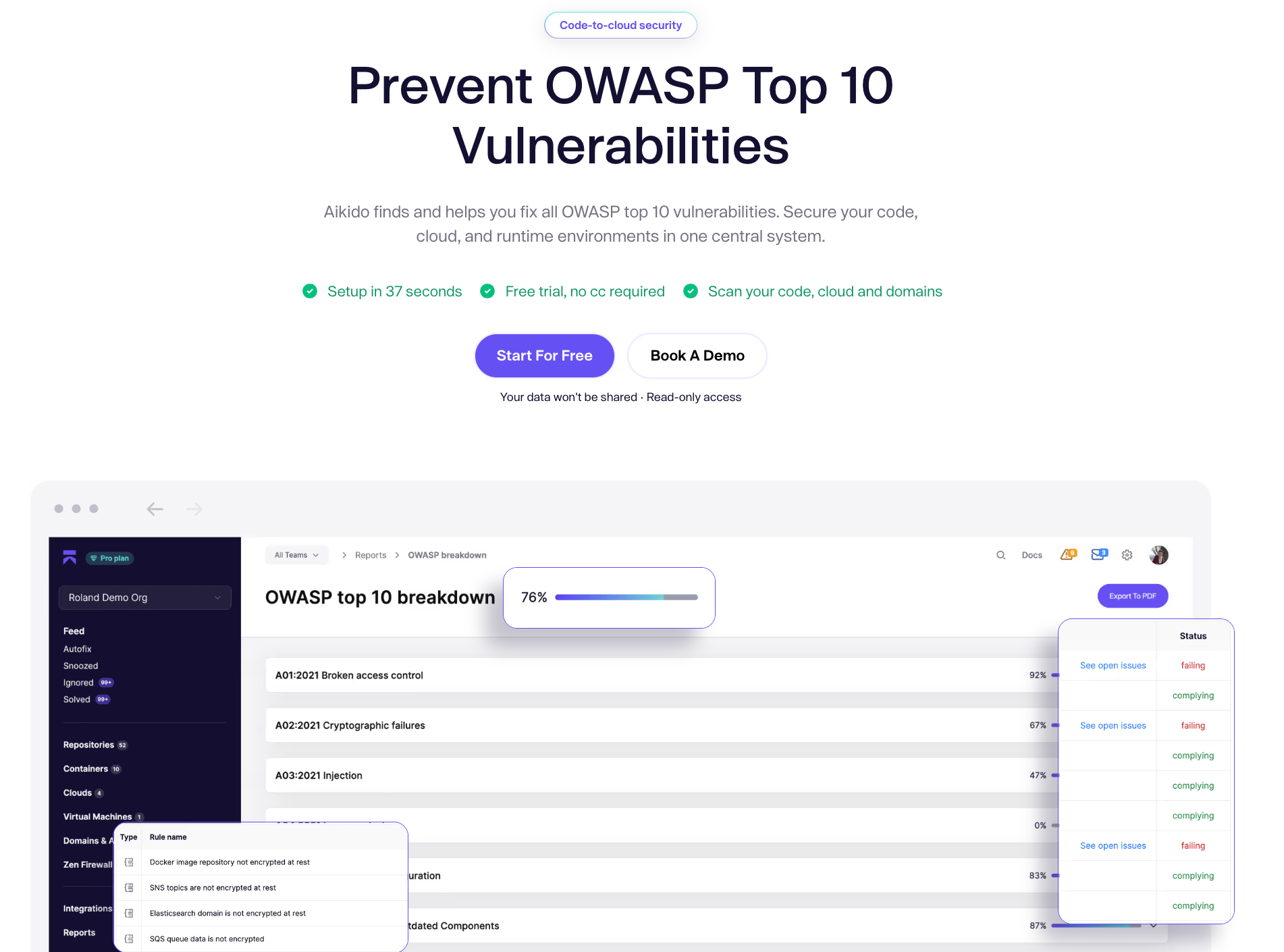
Aikido is the most comprehensive OWASP scanner on the market. Unlike tools that only cover part of the Top 10, Aikido combines SAST, SCA, DAST, secrets scanning, pentesting, and IaC scanning in a single platform, so organizations can easily scan their environment and get a report to see how their stack measures up.
On top of that, Aikido Intel adds real-time threat intelligence, flagging vulnerabilities in open-source packages that haven't yet made it into any CVE database. And the Zen firewall blocks critical injection attacks and API abuse at runtime, covering Security Logging (A09) and Mishandling of Exceptional Conditions (A10) at the infrastructure layer.
Signal quality matters as much as coverage. AutoTriage cuts false positives by over 90%, so alerts mean something. When a real issue surfaces, AI AutoFix generates a merge-ready PR so the path from finding to resolution is as short as possible. Setup takes less than a minute, and most DAST scans complete in under two minutes, so security fits into the development pipeline rather than slowing it down.
{{false-positives}}
AI Pentesting validates real attack paths against your running application, confirming which vulnerabilities are actually exploitable rather than just theoretically present. Where other scanners flag potential issues, pentesting proves them.
Trusted by over 100,000 teams, Aikido delivers enterprise-grade OWASP coverage at a price point accessible to teams of any size.
Key Features
- DAST, SAST, SCA, and IaC in one platform
- Aikido Intel real-time threat intelligence
- AutoTriage with over 90% reduction in false positives
- AI AutoFix with merge-ready PRs
- Zen firewall for runtime protection
- AI Pentesting
- IDE and CI/CD Integration
- Predictable pricing + free tier
- Diverse Developer Fit
ZAP

ZAP is a free, open-source DAST tool originally developed under OWASP, now maintained under Checkmarx's sponsorship as ZAP by Checkmarx.. The fact that it’s free and open source has made it popular for solo and small developer teams. For that same reason, however, ZAP has some notable limitations as an OWASP scanner.
By only utilizing DAST scans, without SAST to scan code and SCA to scan libraries, ZAP cannot reliably find every issue included in the OWASP top 10. It can be a time and labor-intensive process to implement ZAP on the front-end. On the back end, false positives make it difficult to turn results into meaningful security upgrades.
The low barrier to entry makes ZAP look appealing to developers who need quick insights. For anyone who needs efficient scans, reliable results, or a solution that’s suitable for larger teams and commercial products, ZAP leaves much to be desired.
Key Features
- Primarily DAST
- Passive and active scanning
- Manual proxy/interception
- CI/CD integration via CLI/Docker
- Free and open source
Burp Suite

Burp Suite is one of the leading DAST solutions on the market, but it doesn’t have the same reputation as an OWASP scanner.
DAST scanners excel at detecting runtime vulnerabilities. They cannot detect issues present in code such as hardcoded secrets, insecure practices, and logic flaws. As a result, DAST scanners like Burp Suite will fail to detect some of the vulnerabilities on the OWASP Top 10. Finding them will take additional tools not available from Burp Suite and a process to integrate results from disparate scanners.
Another feature of Burp Suite that counts as both a strength and a weakness is the focus of the product on security teams. It’s well suited to security professionals with experience and expertise defending web apps. The complex interface is less suited to developers who are juggling security among other priorities.
Burp Suite works well as a DAST tool, but it has significant limitations as an OWASP scanner and falls short as a comprehensive solution for application security.
Key Features
- Primarily a DAST tool
- CI/CD integration
- Community (free), Professional, Enterprise editions
- Emphasis on manual testing
- Built for security teams
Invicti

Invicti offers a comprehensive platform for web application security that incorporates DAST, SAST, IAST, SCA, API security, secrets scanning, and ASPM to scan for OWASP vulnerabilities, among others. It has impressive capabilities and a positive reputation among developers, but Invicti may not be the right choice for all or even most development teams.
The capabilities are suitable for large and complex web applications, and the pricing reflects that. Invicti offers three tiers (Essentials, Professional, and Ultimate). While Invicti offers a free “proof-of-concept” license, the capabilities are limited compared to other free or freemium options on the market. Some users also note that scan speeds can be slow on larger applications (typical scans run 8-10 hours).
Invicti merits consideration for large companies focused intensely on web application security. For everyone else, including companies that want to secure the entire software development lifecycle with a single solution, consider other options.
Key Features
- DAST, SAST, IAST, and SCA
- Proof-based scanning
- REST and GraphQL, and SOAP API scanning
- ASPM capabilities
- Compliance reporting
- CI/CD integration
Nikto

Nikto is a free, open-source web server scanner that can test for 8,000 potentially dangerous files, outdated software versions, and server misconfigurations. It's fast, accessible, and widely used as a first-pass reconnaissance tool. It's not a substitute for comprehensive OWASP scanning, though.
Scanning with Nikto will not detect all the vulnerabilities in the OWASP top 10. The server-side approach means it will miss application logic flaws like SQL injections and XSS scanning. Due to its pattern-based approach, it will also return a large number of false positives, and it lacks a GUI to display the results.
Nikto can be a helpful complement to other web application scanners, especially since it’s free and easy to use. Solo developers may want to run a scan early in development to find common issues. But for most development teams, Nikto will be inadequate for OWASP scanning or comprehensive application security.
Key Features
- Command-line web server scanner
- Free and open source
- CI/CD integration via Docker
- Multiple report formats
- Modular architecture
Snyk
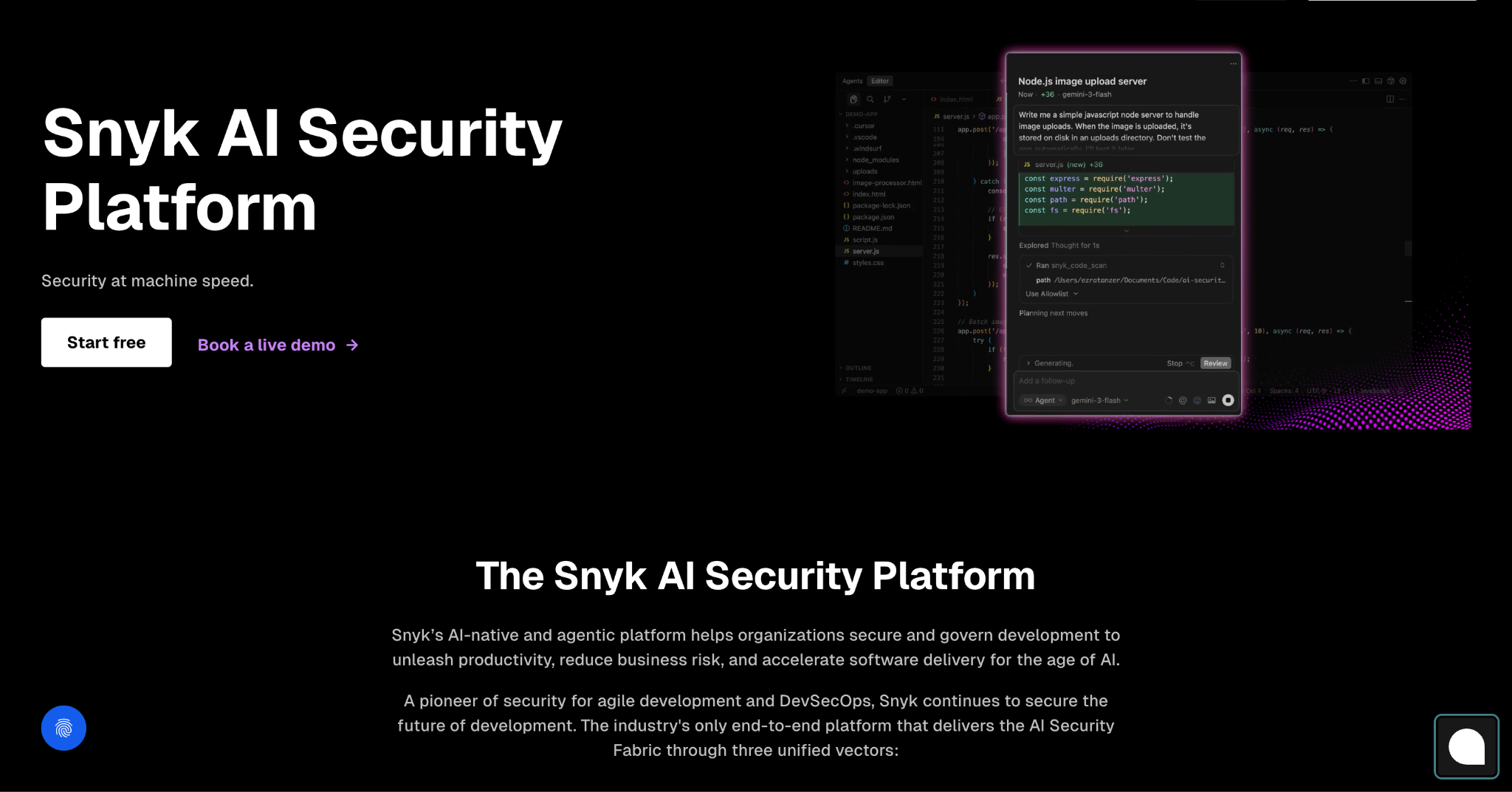
Snyk has become one of the best-known companies in the application security space, which can be both an advantage and a disadvantage. Tools necessary for OWASP scanning, such as SCA, SAST, and DAST are all available from Snyk and well-regarded among developers. But they come at a high cost.
Snyk costs more (significantly more in some cases) than most other options on this list. And while that price pays for application security tools that exceed the framework of OWASP, there are notable absences like Cloud Security Posture Management (CSPM) and an in-app firewall. Despite the high costs, Snyk has been criticized for having a high false-positive rate and a confusing interface.
Developers needing strong SCA or SAST capabilities may want to consider Snyk. But those capabilities come at a significant cost, and comparable coverage is available elsewhere without the per-developer pricing model or the need to bolt on separate modules for every scan type. Those looking for more complete OWASP coverage, lower noise, and a more transparent pricing structure should look elsewhere.
Key Features
- DAST, SAST, and SCA
- CI/CD integration
- Risk scoring
- Automated remediations
- Free tier plus paid plans
Vendor Comparison
Choose a scanner that actually covers the Top 10
While the market is full of capable and compelling solutions for application security, OWASP scanners that comprehensively cover the top 10 vulnerabilities are quite rare. Among those that can actually deliver full coverage, most come with a catch: high cost, suitable for enterprises only, full of false positives, or inefficient remediation workflows.
Aikido ranks first on the list of the top OWASP scanners because it clears all those bars. It combines SAST, SCA, DAST, IaC scanning, real-time threat intelligence, and AI-powered remediation in a single platform built around how developers actually work, at a price point that's attainable to small teams and midsize companies
OWASP scanners are a must-have for today’s developers. Aikido is too.
{{walkthrough}}
OWASP Scanner FAQs
What is an OWASP scanner? An OWASP scanner is a security tool that tests your application against the OWASP Top 10, the industry's definitive list of the most critical web application security risks. Most scanners combine multiple methods including SAST, SCA, DAST, and secrets scanning to cover the full list.
Do I need more than one tool to cover the full OWASP Top 10? With most scanners, yes. DAST-only scanners like ZAP and Burp Suite miss vulnerabilities that only appear in source code or dependencies. Full coverage typically requires a platform that combines multiple scanning methods in a single solution.
How often should I run OWASP scans? As continuously as possible. With 76% of organizations deploying updates weekly or faster, running scans only periodically leaves windows of exposure. The best scanner is one that integrates into your CI/CD pipeline and runs automatically on every build.
What is the difference between SAST and DAST? SAST analyzes your source code before the application runs, catching issues like hardcoded secrets and insecure logic early in development. DAST tests the running application, finding vulnerabilities that only surface at runtime like broken access control and misconfigurations. Comprehensive OWASP coverage requires both.
Why do false positives matter in OWASP scanning? A high false positive rate means developers spend time investigating issues that aren't real, which erodes trust in the tool and leads to alert fatigue. When alerts lose meaning, real vulnerabilities get ignored. Effective scanners like Aikido use automated triage to cut false positives so that when something surfaces, it warrants attention.
<script type="application/ld+json">
{
"@context": "https://schema.org",
"@graph": [
{
"@type": "WebPage",
"@id": "https://www.aikido.dev/blog/top-owasp-scanners#webpage",
"url": "https://www.aikido.dev/blog/top-owasp-scanners",
"name": "Top OWASP Scanners in 2026 for Web Application Security",
"description": "A comprehensive comparison of the top OWASP scanners in 2026, covering how each tool maps to the OWASP Top 10, what scanning methods they use, and which solution delivers the most complete coverage for web application security teams.",
"inLanguage": "en-US",
"isPartOf": {
"@type": "WebSite",
"@id": "https://www.aikido.dev#website",
"url": "https://www.aikido.dev",
"name": "Aikido Security",
"publisher": {
"@id": "https://www.aikido.dev#organization"
}
},
"breadcrumb": {
"@id": "https://www.aikido.dev/blog/top-owasp-scanners#breadcrumb"
},
"mainEntity": {
"@id": "https://www.aikido.dev/blog/top-owasp-scanners#article"
},
"speakable": {
"@type": "SpeakableSpecification",
"cssSelector": ["h1", "h2", ".article-intro"]
}
},
{
"@type": "BreadcrumbList",
"@id": "https://www.aikido.dev/blog/top-owasp-scanners#breadcrumb",
"itemListElement": [
{
"@type": "ListItem",
"position": 1,
"name": "Home",
"item": "https://www.aikido.dev"
},
{
"@type": "ListItem",
"position": 2,
"name": "Blog",
"item": "https://www.aikido.dev/blog"
},
{
"@type": "ListItem",
"position": 3,
"name": "Top OWASP Scanners in 2026 for Web Application Security",
"item": "https://www.aikido.dev/blog/top-owasp-scanners"
}
]
},
{
"@type": "TechArticle",
"@id": "https://www.aikido.dev/blog/top-owasp-scanners#article",
"mainEntityOfPage": {
"@id": "https://www.aikido.dev/blog/top-owasp-scanners#webpage"
},
"headline": "Top OWASP Scanners in 2026 for Web Application Security",
"alternativeHeadline": "Best OWASP Scanners in 2026: A Developer's Comparison Guide",
"description": "Most OWASP scanners don't actually cover the full Top 10. This guide compares the leading OWASP scanning tools in 2026 — including Aikido, ZAP, Burp Suite, Invicti, Nikto, and Snyk — evaluating each across SAST, SCA, DAST, secrets scanning, pentesting, IaC scanning, false positive rates, pricing, and overall OWASP Top 10 coverage. Includes a breakdown of how each scanning method maps to specific OWASP categories and a vendor comparison table.",
"url": "https://www.aikido.dev/blog/top-owasp-scanners",
"datePublished": "2026-05-06T00:00:00+00:00",
"dateModified": "2026-05-06T00:00:00+00:00",
"inLanguage": "en-US",
"author": {
"@id": "https://www.aikido.dev/authors/nicholas-thomson#person"
},
"publisher": {
"@id": "https://www.aikido.dev#organization"
},
"image": {
"@type": "ImageObject",
"@id": "https://www.aikido.dev/blog/top-owasp-scanners#image",
"url": "https://www.aikido.dev/images/blog/top-owasp-scanners-2026.png",
"width": 1200,
"height": 630
},
"articleSection": "Application Security",
"timeRequired": "PT10M",
"proficiencyLevel": "Intermediate",
"keywords": [
"OWASP scanner",
"OWASP Top 10",
"best OWASP scanners 2026",
"web application security tools",
"SAST tools",
"SCA tools",
"DAST tools",
"secrets scanning",
"IaC scanning",
"application security testing",
"vulnerability scanning",
"false positive reduction",
"AI pentesting",
"developer security tools",
"Aikido Security",
"ZAP scanner",
"Burp Suite",
"Snyk",
"Invicti",
"Nikto",
"DevSecOps tools",
"CI/CD security"
],
"about": [
{
"@type": "Thing",
"name": "OWASP Top 10",
"description": "The Open Worldwide Application Security Project's ranked list of the ten most critical web application security risks, published every four years and used as the definitive benchmark by security teams worldwide.",
"sameAs": "https://owasp.org/www-project-top-ten/"
},
{
"@type": "Thing",
"name": "Web Application Security Scanning",
"description": "The practice of using automated tools to identify vulnerabilities in web applications by combining static analysis, dynamic testing, dependency scanning, and infrastructure checks."
},
{
"@type": "Thing",
"name": "Static Application Security Testing",
"description": "SAST analyzes application source code before it runs to detect vulnerabilities including injection flaws, cryptographic failures, insecure design patterns, authentication weaknesses, and data integrity issues.",
"sameAs": "https://en.wikipedia.org/wiki/Static_application_security_testing"
},
{
"@type": "Thing",
"name": "Dynamic Application Security Testing",
"description": "DAST tests a running application for vulnerabilities that only surface at runtime, including broken access control, security misconfiguration, and injection attacks.",
"sameAs": "https://en.wikipedia.org/wiki/Dynamic_application_security_testing"
},
{
"@type": "Thing",
"name": "Software Composition Analysis",
"description": "SCA scans third-party dependencies and open source libraries for known vulnerabilities and malicious packages, directly targeting software supply chain failures.",
"sameAs": "https://en.wikipedia.org/wiki/Software_composition_analysis"
},
{
"@type": "Thing",
"name": "Secrets Scanning",
"description": "Automated detection of hardcoded credentials, API keys, and exposed secrets in source code and repositories, addressing a root cause of authentication failures and supply chain attacks."
},
{
"@type": "Thing",
"name": "Infrastructure as Code Security Scanning",
"description": "Analysis of IaC configuration files to detect security misconfigurations before they reach production environments."
},
{
"@type": "Thing",
"name": "False Positive Reduction in Security Scanning",
"description": "The challenge of minimizing irrelevant or incorrect vulnerability alerts in security tools, which when left unaddressed leads to alert fatigue and causes real vulnerabilities to be ignored."
}
],
"mentions": [
{
"@type": "SoftwareApplication",
"name": "Aikido Security",
"description": "A comprehensive developer security platform combining SAST, SCA, DAST, secrets scanning, IaC scanning, AI pentesting, and real-time threat intelligence in a single platform. Features AutoTriage for 90%+ false positive reduction and AI AutoFix for merge-ready remediation PRs.",
"url": "https://www.aikido.dev",
"applicationCategory": "SecurityApplication"
},
{
"@type": "SoftwareApplication",
"name": "ZAP by Checkmarx",
"description": "A free, open-source DAST tool originally developed under OWASP, now maintained under Checkmarx's sponsorship. Limited to DAST scanning without SAST or SCA capabilities.",
"url": "https://www.zaproxy.org",
"applicationCategory": "SecurityApplication"
},
{
"@type": "SoftwareApplication",
"name": "Burp Suite",
"description": "A leading DAST solution focused on web application security testing, primarily suited to experienced security professionals. Does not include SAST or SCA capabilities.",
"url": "https://portswigger.net/burp",
"applicationCategory": "SecurityApplication"
},
{
"@type": "SoftwareApplication",
"name": "Invicti",
"description": "A comprehensive web application security platform incorporating DAST, SAST, IAST, SCA, API security, secrets scanning, and ASPM. Suited to large enterprise environments.",
"url": "https://www.invicti.com",
"applicationCategory": "SecurityApplication"
},
{
"@type": "SoftwareApplication",
"name": "Nikto",
"description": "A free, open-source command-line web server scanner that tests for dangerous files, outdated software versions, and server misconfigurations. Not a substitute for comprehensive OWASP scanning.",
"url": "https://cirt.net/Nikto2",
"applicationCategory": "SecurityApplication"
},
{
"@type": "SoftwareApplication",
"name": "Snyk",
"description": "A well-known application security platform offering SCA, SAST, and DAST capabilities. Notable for strong dependency scanning but criticized for high cost, high false positive rates, and a complex interface.",
"url": "https://snyk.io",
"applicationCategory": "SecurityApplication"
},
{
"@type": "Thing",
"name": "OWASP Top 10 2025",
"description": "The 2025 edition of the OWASP Top 10, including Broken Access Control, Security Misconfiguration, Software Supply Chain Failures, Cryptographic Failures, Injection, Insecure Design, Authentication Failures, Software or Data Integrity Failures, Security Logging and Alerting Failures, and Mishandling of Exceptional Conditions.",
"sameAs": "https://owasp.org/www-project-top-ten/"
},
{
"@type": "Thing",
"name": "CI/CD Pipeline Security",
"description": "Integration of automated security scanning into continuous integration and deployment pipelines to catch vulnerabilities before code reaches production."
}
]
},
{
"@type": "ItemList",
"@id": "https://www.aikido.dev/blog/top-owasp-scanners#toollist",
"name": "Top OWASP Scanners in 2026",
"description": "A ranked comparison of the leading OWASP scanning tools evaluated on coverage, scanning methods, false positive rates, pricing, and developer fit.",
"numberOfItems": 6,
"itemListOrder": "https://schema.org/ItemListOrderDescending",
"itemListElement": [
{
"@type": "ListItem",
"position": 1,
"name": "Aikido Security",
"description": "The most comprehensive OWASP scanner on the market, combining SAST, SCA, DAST, secrets scanning, pentesting, and IaC scanning in a single platform with AutoTriage, AI AutoFix, and the Zen runtime firewall.",
"url": "https://www.aikido.dev"
},
{
"@type": "ListItem",
"position": 2,
"name": "ZAP by Checkmarx",
"description": "A free, open-source DAST tool popular with solo and small developer teams, with notable limitations as a comprehensive OWASP scanner due to lack of SAST and SCA.",
"url": "https://www.zaproxy.org"
},
{
"@type": "ListItem",
"position": 3,
"name": "Burp Suite",
"description": "A leading DAST solution well-suited to experienced security professionals, but limited as a full OWASP scanner due to absent SAST, SCA, and secrets scanning capabilities.",
"url": "https://portswigger.net/burp"
},
{
"@type": "ListItem",
"position": 4,
"name": "Invicti",
"description": "A comprehensive enterprise web application security platform with broad OWASP coverage, but high cost and slow scan speeds make it unsuitable for most small and midsize teams.",
"url": "https://www.invicti.com"
},
{
"@type": "ListItem",
"position": 5,
"name": "Nikto",
"description": "A free, open-source web server scanner useful as a first-pass reconnaissance tool, but inadequate as a standalone OWASP scanner due to limited coverage and high false positive rates.",
"url": "https://cirt.net/Nikto2"
},
{
"@type": "ListItem",
"position": 6,
"name": "Snyk",
"description": "A well-regarded application security platform with strong SCA and SAST capabilities, but high per-developer pricing, a high false positive rate, and notable gaps in cloud security limit its value as a complete OWASP solution.",
"url": "https://snyk.io"
}
]
},
{
"@type": "FAQPage",
"@id": "https://www.aikido.dev/blog/top-owasp-scanners#faq",
"mainEntity": [
{
"@type": "Question",
"name": "What is an OWASP scanner?",
"acceptedAnswer": {
"@type": "Answer",
"text": "An OWASP scanner is a security tool that tests your application against the OWASP Top 10, the industry's definitive list of the most critical web application security risks. Most scanners combine multiple methods including SAST, SCA, DAST, and secrets scanning to cover the full list."
}
},
{
"@type": "Question",
"name": "Do I need more than one tool to cover the full OWASP Top 10?",
"acceptedAnswer": {
"@type": "Answer",
"text": "With most tools, yes. DAST-only scanners like ZAP and Burp Suite miss vulnerabilities that only appear in source code or dependencies. Full coverage typically requires a platform that combines multiple scanning methods in a single solution."
}
},
{
"@type": "Question",
"name": "How often should I run OWASP scans?",
"acceptedAnswer": {
"@type": "Answer",
"text": "As continuously as possible. With 76% of organizations deploying updates weekly or faster, running scans only periodically leaves windows of exposure. The best scanner is one that integrates into your CI/CD pipeline and runs automatically on every build."
}
},
{
"@type": "Question",
"name": "What is the difference between SAST and DAST?",
"acceptedAnswer": {
"@type": "Answer",
"text": "SAST analyzes your source code before the application runs, catching issues like hardcoded secrets and insecure logic early in development. DAST tests the running application, finding vulnerabilities that only surface at runtime like broken access control and misconfigurations. Comprehensive OWASP coverage requires both."
}
},
{
"@type": "Question",
"name": "Why do false positives matter in OWASP scanning?",
"acceptedAnswer": {
"@type": "Answer",
"text": "A high false positive rate means developers spend time investigating issues that are not real, which erodes trust in the tool and leads to alert fatigue. When alerts lose meaning, real vulnerabilities get ignored. Effective scanners use automated triage to cut false positives so that when something surfaces, it warrants attention."
}
}
]
},
{
"@type": "Person",
"@id": "https://www.aikido.dev/authors/nicholas-thomson#person",
"name": "Nicholas Thomson",
"url": "https://www.aikido.dev/authors/nicholas-thomson",
"jobTitle": "Senior SEO & Growth Lead",
"worksFor": {
"@id": "https://www.aikido.dev#organization"
},
"sameAs": [
"https://www.linkedin.com/",
"https://x.com/"
]
},
{
"@type": "Organization",
"@id": "https://www.aikido.dev#organization",
"name": "Aikido Security",
"description": "Aikido Security is a developer security platform that combines SAST, SCA, DAST, secrets scanning, IaC scanning, AI pentesting, and real-time threat intelligence in a single solution designed to minimize developer cognitive burden while maximizing vulnerability coverage.",
"url": "https://www.aikido.dev",
"logo": {
"@type": "ImageObject",
"url": "https://www.aikido.dev/logo.png"
},
"sameAs": [
"https://www.linkedin.com/company/aikido-security",
"https://twitter.com/aikido_security"
]
}
]
}
</script>




