Cut 94% of your noise with reachability-based SCA & AutoFix
Secure third-party dependencies with reachability analysis, pre-CVE and malware intelligence, SBOMs, and AI-assisted fixes.
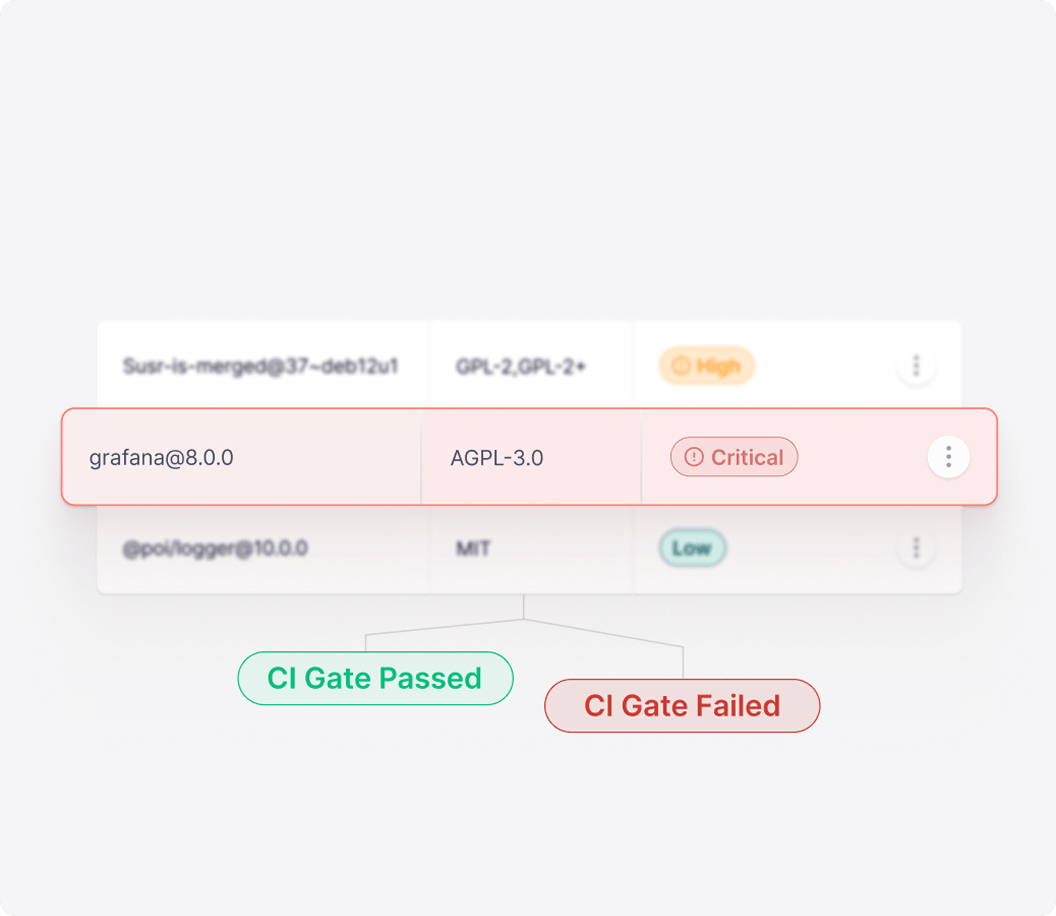
Cut Noise: Prioritise reachable issues
Fix Faster: AutoFix PRs + hardened packages & images
Stay Compliant: SBOM + license policies
.png)
.jpeg)















Multi-layered reachability analysis with one-click AutoFix
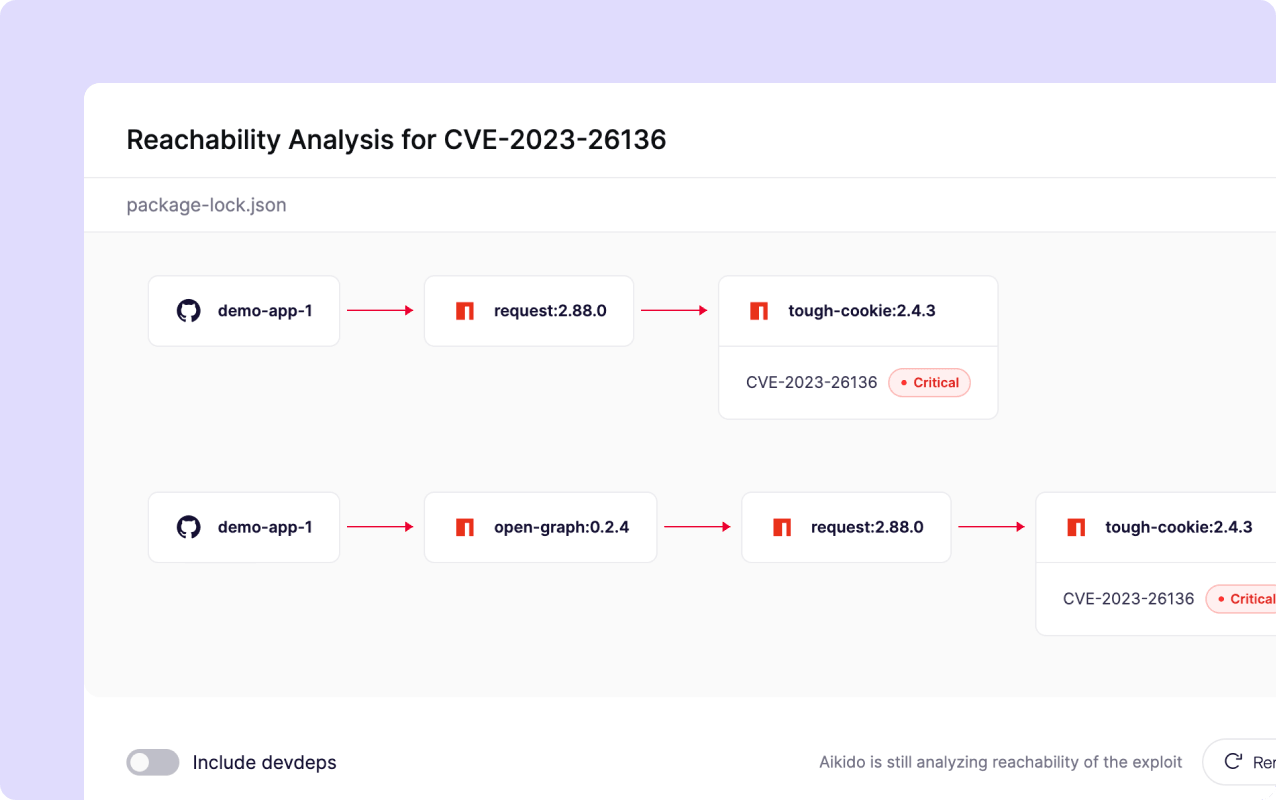
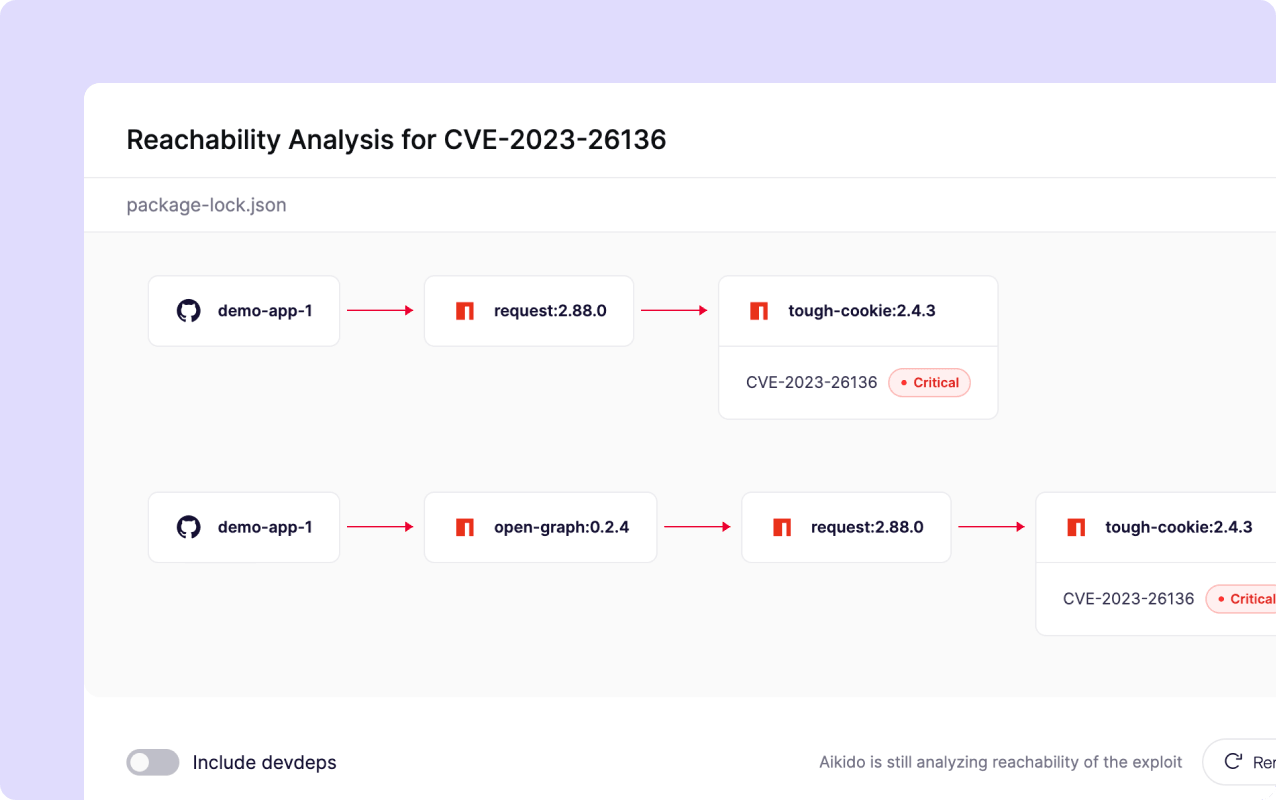
Fix what's reachable. Ignore what's not.
Aikido traces actual call chains from your code into third-party packages to determine which vulnerabilities are genuinely reachable at runtime and ignores the ones you’re not using.
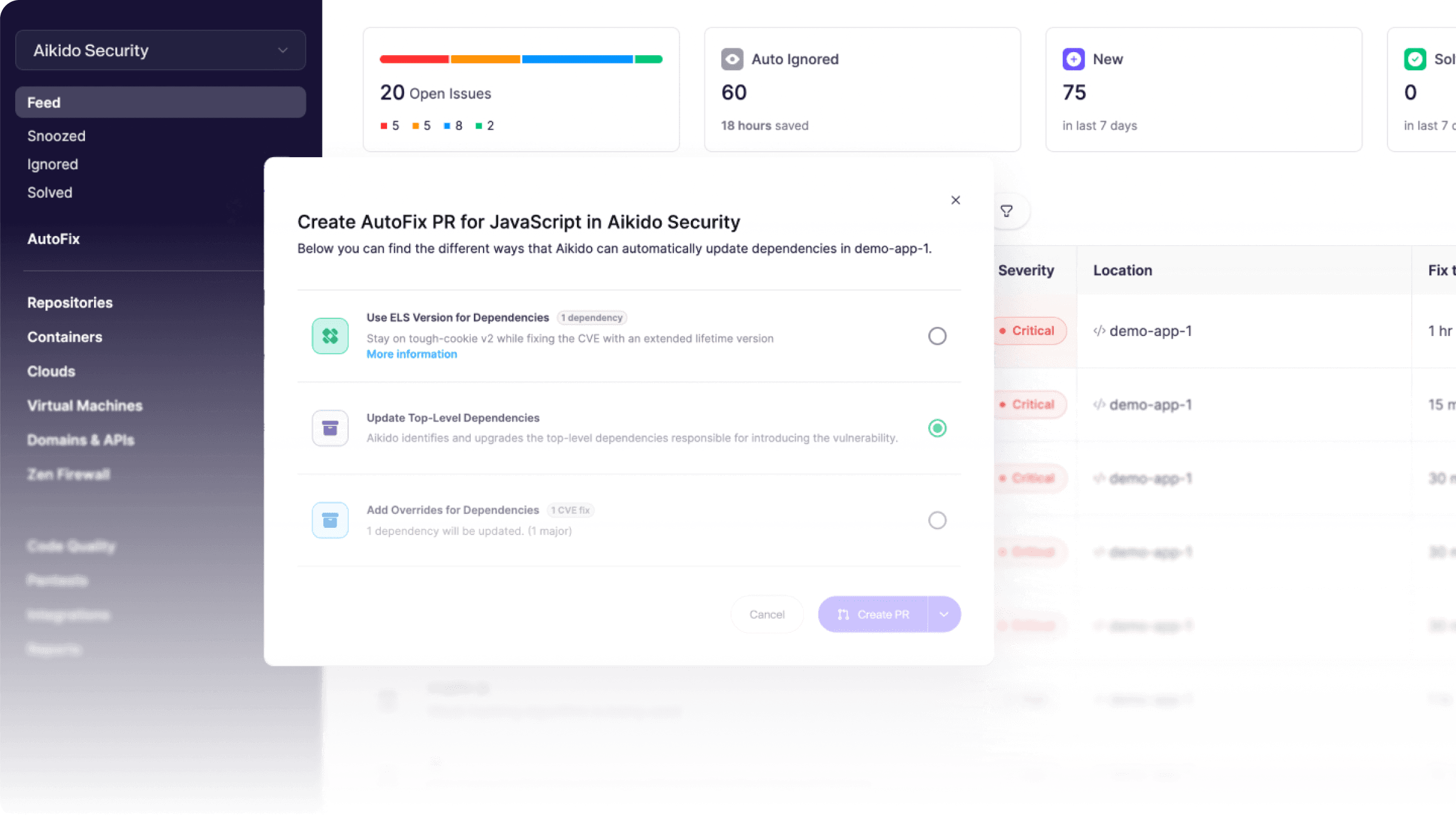
One-click fixes and auto-generated PRs.
Aikido creates PRs with safe, non-breaking version upgrades. For critical CVEs, auto-merge keeps your exposure window near zero.
"The 94% noise reduction is a game changer. It allows us to focus on the 6% that actually matter. That alone is gold… It’s a massive productivity and sanity boost."

What sets Aikido’s SCA apart from other tools
.png)
First scan results in under 2 minutes
Connect your repo and see only the vulnerabilities that are actually reachable.

“Aikido’s automation and accuracy help our teams focus on building, not babysitting vulnerabilities.”















Frequently Asked Questions

Software Composition Analysis (SCA) is basically a health check for your open-source dependencies. It scans the libraries and packages you pull into your project and flags known open-source vulnerabilities, license landmines, and other risks. You should care because if you're using open-source (spoiler: you are), one vulnerable dependency can compromise your entire application's security. SCA helps ensure the third-party code in your projects isn't a hidden backdoor or ticking time bomb.

It works like an automated detective for your dependencies. Aikido's SCA scanner identifies all the libraries and versions you're using (your dependency tree) and cross-references each one against a constantly updated database of known vulnerabilities (CVEs) and open-source threat intel. In plain English: if you're using a library with a known security hole or even a malicious package, Aikido will spot it and alert you. It's comprehensive dependency scanning that taps into vulnerability feeds to catch issues fast.

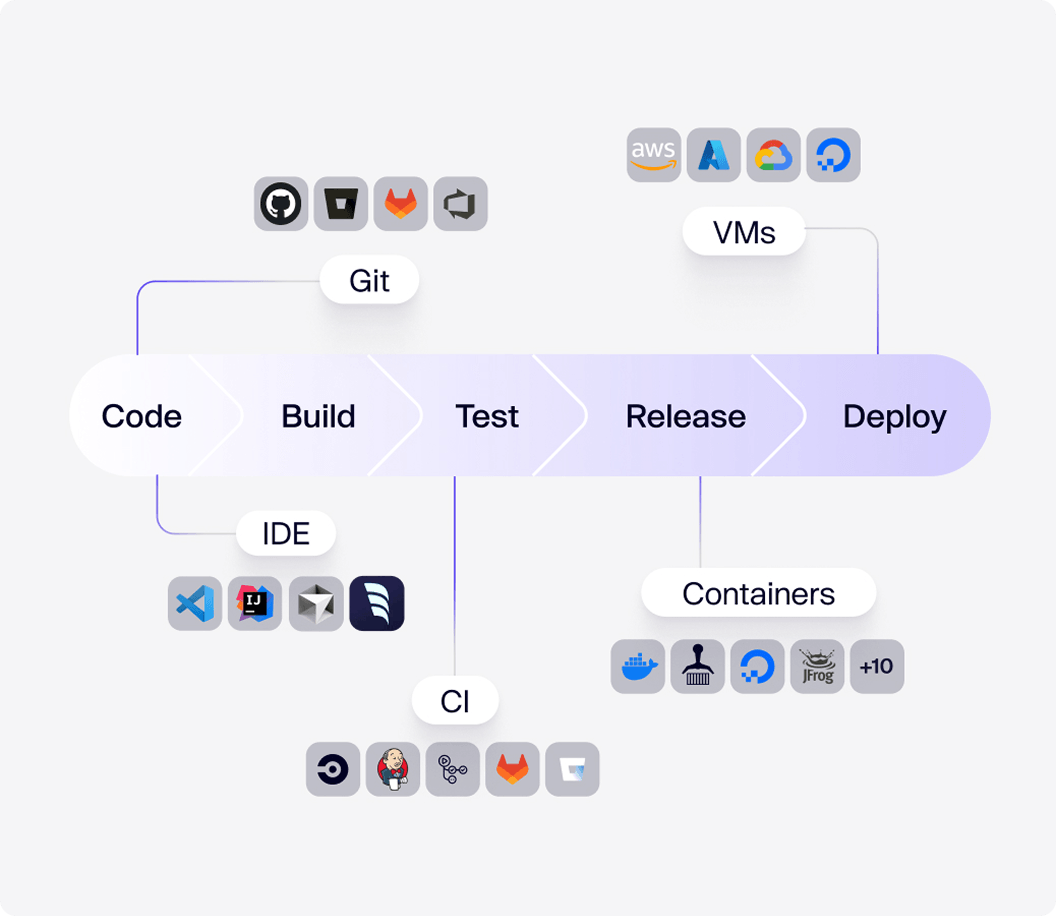
Absolutely - Aikido's SCA fits right into your CI/CD pipeline. You can hook it up with GitHub Actions, GitLab CI, Jenkins, CircleCI, or whatever you use so that dependency scanning runs automatically on every build or pull request. This means new vulnerable dependencies get caught and reported before they land in production. In short, automated open-source security checks become a built-in part of your development workflow.

Aikido doesn't just nag you about vulnerable dependencies - it helps fix them. For many issues, it provides one-click AutoFix solutions: it suggests the safe version to upgrade to and can automatically open a pull request to bump the dependency for you. In other cases, it gives clear remediation guidance so you know exactly how to resolve the problem. Bottom line: it not only reports open-source security issues, it also streamlines the fix (often doing the heavy lifting for you).

Yes - Aikido's SCA can whip up a Software Bill of Materials (SBOM) for your app with one click. It compiles a full list of all open-source components in your project and lets you export it in standard formats like CycloneDX or SPDX (or even a plain CSV). This SBOM gives you and your compliance team a complete inventory of what's in your software. It's great for visibility, compliance audits, and making sure there are no "unknown" pieces in your stack.

Aikido's SCA supports most major programming languages and their package managers - chances are if its' popular, it's supported. For example, it covers JavaScript/TypeScript (npm, Yarn, pnpm), Python (pip, Poetry), Java/Scala/Kotlin (Maven, Gradle, sbt), .NET (NuGet), Ruby (Bundler), PHP (Composer), Go (Go modules), Rust (Cargo), Swift (CocoaPods and SwiftPM), Dart (pub), and more. It even handles C/C++ projects (scanning for known dependencies without needing lockfiles). In short, Aikido's scanner has broad language coverage, so it can likely analyze whatever tech stack you throw at it.

Essentially any known open-source vulnerability in your dependencies will be caught. For instance, if your project includes a library affected by Log4Shell (the infamous Log4j vulnerability), Aikido's SCA will flag it. Same goes for something like the OpenSSL Heartbleed bug - if that vulnerable version is present, you'll know. It also catches less famous CVEs and even malicious packages (like compromised npm/PyPI packages); if there's a known flaw or backdoor in a dependency, Aikido will detect it.

Aikido's SCA offers similar coverage to Snyk's open-source scanning but with a lot less fluff. Snyk is powerful but often bombards you with a ton of alerts (including low-priority issues), whereas Aikido auto-prioritizes and shows you just the real risks - less noise, more signal. Unlike Dependabot, which simply automates version bump PRs for known vulns, Aikido gives you full context on vulnerabilities, scans for malicious packages, checks licenses, and provides one-click fixes. In short, you get Snyk-level thoroughness without the alert fatigue, and far more capability than basic tools like Dependabot.

Think of Dependabot as a helpful start but not the whole story. Dependabot will update dependencies with known issues, but it won't catch everything - for example, it might miss a malicious package or a vulnerability that doesn't yet have an update available. Aikido's SCA gives you a much deeper open-source security scan: it finds issues that slip past Dependabot, provides details on each vulnerability, and even auto-fixes them. In short, if you want thorough dependency scanning and not just basic update automation, you'll still want Aikido watching your back.