Application security is a balancing act, teams are expected to detect vulnerabilities across code, dependencies, Infrastructure-as-Code (IaC), and runtime, all while scaling effectively and without slowing down development.
SonarQube and GitHub Advanced Security are some of the most common tools considered by teams looking to address this challenge. However, choosing between them isn’t always straightforward, as teams have to weigh trade-offs such as coverage gaps, workflow integration, platform support, and more.
In this article, we’ll compare SonarQube and GitHub Advanced Security side by side, highlighting their strengths, weaknesses, and overlaps to help you determine which tool best aligns with your team’s security needs.
TL;DR
Aikido Security brings together the strengths of SonarQube and GitHub Advanced Security (GHAS) into a single, developer-friendly platform. While SonarQube emphasizes code quality and governance and GHAS focuses on GitHub-native SAST and dependency scanning, both leave gaps in coverage, noise reduction, and automation.
When compared to GitHub Advanced Security (GHAS), Aikido Security delivers broader and more robust SAST and dependency scans through its reachability analysis engine, platform-agnostic architecture, and AI-driven risk correlation. This allows teams to focus on truly exploitable vulnerabilities while reducing false positives, alert fatigue, and triage time.
In comparison to SonarQube, Aikido uses LLMs alongside standard code quality rules. That means that instead of simply checking whether code compiles cleanly, Aikido evaluates whether it’s the right code, assessing logic, intent, and context. This allows it to go beyond conventional static analysis tools that only detect surface-level patterns or syntax issues. Aikido’s code quality analyzes pull requests for bugs, security risks and logic issues, then offers actionable suggestions before the code is merged.
Compared to both GitHub Advanced Security and SonarQube, Aikido Security offers significantly more breadth thanks to its modular architecture. Teams can start with any module, such as Aikido Code (SAST, Code Quality, IaC Scanning, Malware Detection), Aikido Cloud (CSPM, CNAPP), Aikido Defend (RASP) and Aikido Attack (AI Penetration Testing, DAST), and expand as needs grow.
For both startups and enterprises, Aikido Security consistently stands out thanks to its developer-friendly workflow, comprehensive AppSec coverage, AI-driven risk prioritization, and the ability to replace multiple tools within a single developer-friendly workflow.
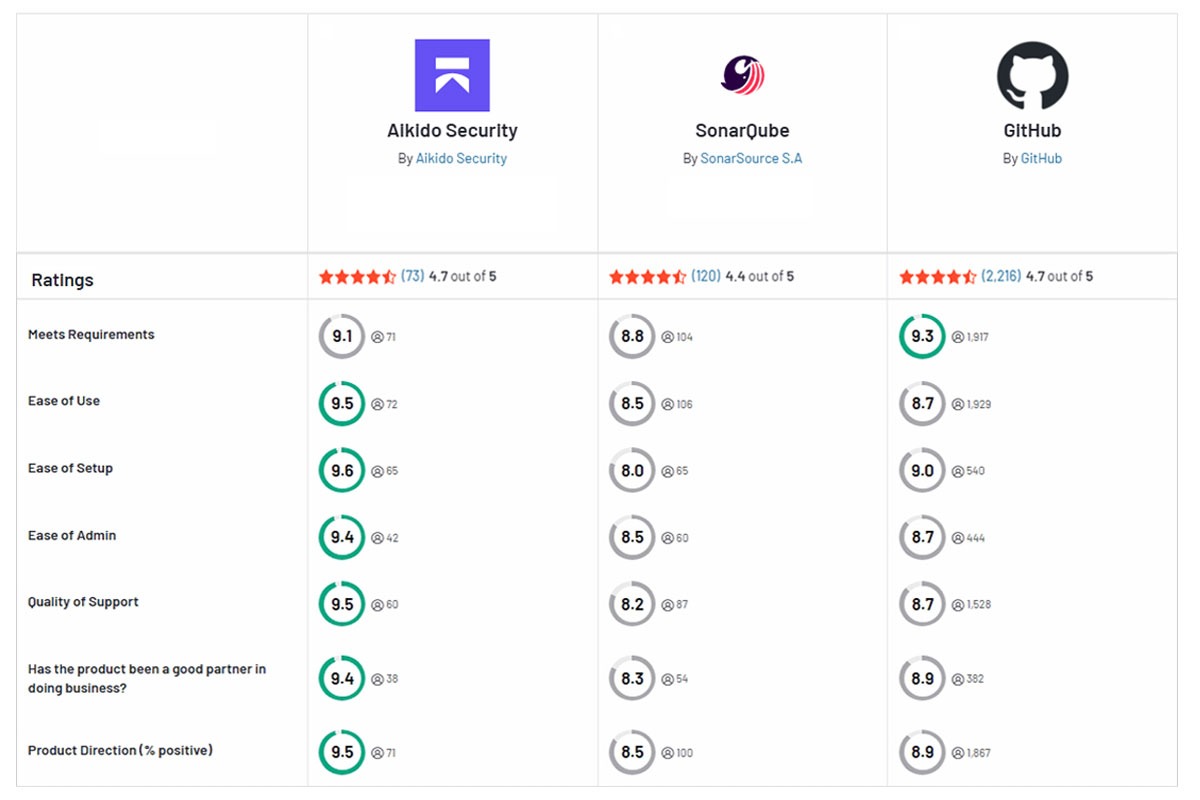
Quick Feature Comparison: SonarQube vs GHAS vs Aikido Security
What is SonarQube?
SonarQube is a continuous code inspection platform. Development teams use SonarQube for its ability to scan source code for bugs, code smells, and basic security weaknesses before release. Its static analysis engine checks code against thousands of rules for code quality and common security issues.
Pros:
- Robust code quality analysis
- Integrates with common CI/CD platforms
- Customizable rule-sets and quality gates
- Large community support
Cons:
- Primarily focused on code quality
- Coverage varies across programming languages
- Lacks runtime and environment-level security capabilities
- Requires additional third-party tools to achieve full AppSec coverage
- It is known to generate a high number of low-impact alerts
- Introduces infrastructure and maintenance overhead
- Advanced security rules and features are only available in paid editions.
- Its pricing can become expensive and hard to predict when scaling
What is GitHub Advanced Security?
GitHub Advanced Security (GHAS) is a suite of security features for code hosted on GitHub Enterprise. It integrates directly into your repositories and pull requests. GHAS includes CodeQL static analysis for deep code vulnerability scanning, secret scanning to catch leaked credentials, supply chain insights for supply chain security, and dependency scanning via Dependabot alerts. Because it’s built into GitHub, security alerts show up directly in PRs, issues, and the repository security tab.
Pros:
- Seamless Integration with GitHub workflows
- Robust static analysis engine
- Zero Infrastructure Overhead
- Automated supply chain protection
Cons:
- It Works only on code hosted on GitHub
- False Positives
- High alert volume
- Limited code quality features
- Lacks native scanning for container images or IaC
- It doesn’t cover cloud posture management
- It’s only available on GitHub Enterprise
- Users have reported its configuration as cumbersome
- Lacks the advanced customization and integrations many teams now expect.
Feature-by-Feature Comparison
Core Security Capabilities
SonarQube: SonarQube is primarily a code quality tool, with basic Static Application Security Testing (SAST).. It scans application source code for bugs, code smells and known vulnerability patterns, but its security testing capabilities are limited. SonarQube can identify vulnerabilities such as SQL injection patterns and weak cryptography. Its findings are marked as “security hotspots” which require manual review.
SonarQube lacks built-in scanning for open-source dependency vulnerabilities and container images. and may miss complex flaws that go beyond its pattern-based rules.
GitHub Advanced Security: GHAS, on the other hand, tackles security across code and dependencies. It uses its CodeQL engine to perform semantic static analysis to find code vulnerabilities . GHAS also monitors your third-party libraries for known CVEs via dependency scanning and secures secrets to prevent leaks. Allowing GHAS to cover software supply chain risks out-of-the-box.
In summary, GitHub Advanced Security provides broader coverage of your security surface (code, secrets, dependencies) while SonarQube focuses on code quality and basic static code issues. Neither tool provides dynamic testing (DAST), cloud monitoring, and runtime security.
Integration and DevOps Workflow
When it comes to integrating into development pipelines, SonarQube and GHAS differ significantly.
SonarQube: SonarQube can integrate with common CI/CD systems (Jenkins, GitLab CI, Azure DevOps) and works with various version control platforms. Typically, you run a Sonar scanner during the build, and results are published to a SonarQube server or SonarCloud. This flexibility is great,but also requires additional setup and maintenance. You might need to adjust pipeline configurations, manage webhooks for PR decoration, and deal with a separate web User Interface (UI) to view findings.
GitHub Advanced Security: GitHub Advanced Security is, by design, tightly integrated into the GitHub workflow. If your code lives on GitHub, enabling GHAS means security scans run automatically on each push or pull request via GitHub Actions. Developers see CodeQL findings as comments on their pull requests or in the repository’s Security tab, no separate app or context-switching needed. Its security feedback is also delivered in-line during code review. However, with its deep GitHub integration there is also a possibility for vendor lock-in, as GHAS only on GitHub.
In summary, while GHAS provides a smoother experience for GitHub-centric teams, SonarQube offers broader integration flexibility across different CI/CD and Supply Chain Management (SCM) platforms.
Accuracy and Performance
A critical concern in any security tool is how noisy it is and how much it actually catches.
SonarQube: SonarQube has a reputation for high false positives, flagging low-priority issues. Teams have reported experiencing “alert fatigue” with SonarQube, where numerous low-priority findings cause engineers to start ignoring the tool. In practice, SonarQube can miss serious security bugs (false negatives) while also raising many minor alerts. Many of its security rules are simple pattern checks, which means they require manual triage to determine actual risk. Leading to longer triage times and eroded trust in results.
Performance-wise, SonarQube analysis runs in the CI pipeline and varies in speed, from a few minutes to longer for large codebases.
GitHub Advanced Security’s: GitHub Advanced Security’s CodeQL is more advanced in its analysis, which often translates to fewer false positives on the vulnerability types it knows. CodeQL has strong dataflow analysis for certain flaws, so when it flags vulnerabilities such as XSS or SQLi, it’s likely a real issue. However, GHAS is not immune to noise. Users have reported that its dependency scanner can flood teams with alerts if the project has many outdated libraries, and will only find what it has queries for.
On the performance front, CodeQL analysis is relatively heavy. Running GHAS scans via GitHub Actions might add a minute or two to each PR’s checks .
Overall, GHAS tends to be more accurate for standard vulnerability patterns and produces less random noise than SonarQube, but it can still miss complex logic flaws unless you write custom queries. SonarQube, meanwhile, might catch a broader set of code quality issues but at the cost of more false alarms.
Coverage and Scope
SonarQube: SonarQube covers a wide range of programming languages and code quality domains, but a narrow range of security testing types. It supports 10+ languages (from Java, C#, and Python to COBOL and PL/SQL) and is great for polyglot codebases. SonarQube also tracks code quality metrics (maintainability, duplication, test coverage), which GHAS doesn’t
However, SonarQube’s security coverage is limited to static code analysis (SAST) within your code. It doesn’t natively scan open-source dependencies for known vulnerabilities, examine container images, or monitor cloud configurations.
GitHub Advanced Security: GHAS’s scope is both broader and narrower than SonarQube. GHAS covers code,dependencies, and secrets, and even some configuration issues. It will alert you to vulnerable npm packages or Python libraries in your project and also prevent developers from committing AWS keys or other secrets.
However, GHAS is narrower in language support and is primarily focused on security. CodeQL supports major languages (such as Java, JavaScript/TypeScript, Python, C/C++, C#, Go),, but if your stack includes uncommon languages GHAS won’t cover it. GHAS also doesn’t provide any feedback on code maintainability or style,duplicate code or complexity.
In summary, GHAS offers deeper security coverage within GitHub (covering both code and supply chain), while SonarQube offers broader language and quality coverage. Platforms like Aikido Security help teams avoid tool sprawl by covering all these aspects in one solution. .
Developer Experience
Adoption by developers is critical. A security tool that frustrates engineers will end up shelved or ignored.
SonarQube: . Setting up SonarQube often requires managing a server, configuring quality profiles, and dealing with a web UI that can feel clunky. Developers typically interact with SonarQube through its web interface or via PR comments. The UI, while powerful, isn’t very intuitive or modern. With many developers seeing SonarQube as a tool for the CI pipeline rather than something that helps them day-to-day. SonarQube also provides plugins like SonarLint for IDEs to provide inline feedback.
SonarQube’s high false positive rate has been known to make developers ignore its alerts over time.Its alerts are not real-time either and by default, issues are reported after code is pushed and analyzed in CI.
GitHub Advanced Security: GHAS’s developer experience is more seamless, if you’re on GitHub. Developers get security feedback as part of code review and CodeQL alerts pop up in pull requests as annotations on affected lines. There’s no separate login or interface, meaning the alerts live alongside your code, which makes developers more likely to see and act on them. GHAS can automatically open pull requests to fix vulnerable dependencies. However, all of this occurs only within GitHub workflows.
GHAS has also been known to produce high alert volumes that can crowd PR discussions and become overwhelming. Another consideration is that CodeQL’s findings can be quite detailed, which can intimidate developers who don’t have extensive security experience. .
Overall, GHAS is more developer-friendly for teams already on GitHub, with security feedback built directly into existing workflows. While, SonarQube often feels like a separate step developers must actively remember to review. Modern developer-first security tools like Aikido Security address these challenges by delivering inline feedback and AI-powered one click auto-fixes.
Pricing and Maintenance
SonarQube: SonarQube offers a free open-source Community Edition , but it lacks many of its advanced features. Its paid editions are priced by lines of code (LOC) and unlock advanced security rules, additional language support, and faster analysis, but come with significant licensing fees and difficult to predict costs. If you self-host SonarQube, you also bear the maintenance overhead: running servers, databases, and upgrades. .
GitHub Advanced Security: GHAS is only available as part of GitHub Enterprise. In other words, to use GHAS on private repos, you need to be on a GitHub Enterprise plan and pay for the GHAS add-on. GitHub’s pricing for this is opaque. For large teams, GHAS can be difficult to predict, and smaller companies might not be able to justify it at all.
On the other hand, since it’s a cloud service, you don’t have to manage any infrastructure, no servers or maintenance efforts.. But you are locked into GitHub’s ecosystem and pricing.
In summary, neither tool is cheap at scale. SonarQube can become expensive as you add more code and need enterprise features, while GHAS carries a steep per-seat cost.
Aikido Security offers a simpler, more transparent pricing model – flat and predictable – and is significantly more affordable at scale than either SonarQube or GitHub Advanced Security.
To help you compare the features of both tools, the table below summarizes it for you.
Aikido Security: The Better Alternative
Aikido Security is a developer-first application security platform that combines intelligent code quality analysis with advanced SAST. It builds on the strengths of SonarQube and GitHub Advanced Security while addressing their key limitations.
Unlike SonarQube’s rule-heavy approach, Aikido treats security as a core part of code quality. Its SAST engine combines traditional static analysis with LLM-powered context awareness to detect real-world issues such as injection risks, insecure command execution, and hardcoded secrets, while reducing false positives common in traditional code quality tools.
Compared to GitHub Advanced Security, Aikido uses OpenGrep, a non-compiling SAST engine that scales reliably across large and complex repositories without the timeouts often seen in compile-based scanners. Findings are correlated across code, dependencies, infrastructure, and runtime context, allowing Aikido to prioritize truly exploitable risks and eliminate up to 85% of noise through AI-assisted triage.
Beyond SAST and dependency scanning, Aikido provides broader security coverage including IaC scanning, container security, DAST and API security testing, runtime protection, cloud security posture management, secrets detection, and AI-powered penetration testing. These capabilities are available modularly or as a unified platform.
Aikido integrates directly into developer workflows across GitHub, GitLab, and Bitbucket, surfacing issues and fix suggestions directly in pull requests, with one-click fixes and automated pull requests for common issues. With platform-agnostic support, flat pricing, and a free forever tier, Aikido delivers comprehensive application security without the cost and complexity of managing multiple tools.
Want to improve your application security? Start your free trial or book a demo with Aikido Security today.
FAQ
How can I integrate SonarQube with GitHub repositories for continuous code analysis?
SonarQube integrates with GitHub by running scans in CI pipelines (GitHub Actions, Jenkins) and reporting results back to pull requests. You’ll need to host and maintain a SonarQube server , configure tokens, and explicitly connect analysis steps into each repository’s workflow.
How does GitHub Advanced Security enhance code security compared to SonarQube?
GitHub Advanced Security (GHAS) embeds security directly into the GitHub developer workflow with native code scanning, secret scanning, and dependency vulnerability alerts. Unlike SonarQube, GHAS focuses less on general code quality and more on identifying real security risks within pull requests and repositories without requiring external infrastructure.
Which tool offers better vulnerability detection: SonarQube or GitHub Advanced Security?
GHAS generally provides stronger vulnerability detection for modern application security, especially around secrets exposure, dependency vulnerabilities, and CodeQL-based security analysis. SonarQube’s strength lies in static code quality and maintainability, but its security rule depth varies by language and often requires complementary tools for full coverage. Platforms like Aikido Security address these gaps by using its AI engine to correlate findings across code, dependencies, cloud, and runtime to reduce noise and highlight only exploitable issues, as well as improve code quality
What are common challenges when migrating from SonarQube to GitHub Advanced Security or vice versa?
Teams moving from SonarQube to GHAS often struggle with losing detailed code-quality metrics and long-term technical debt tracking. Migrating from GHAS to SonarQube can introduce operational overhead, increased false positives, and workflow friction due to external dashboards and infrastructure management.
What are the configuration differences between SonarQube and GitHub Advanced Security for scanning?
SonarQube requires explicit pipeline configuration, scanner setup, server connectivity, and ongoing maintenance. GHAS is largely configuration-light, enabling scans directly from GitHub settings with minimal CI changes, making it easier to adopt at scale.
You Might Also Like:




