Technical leaders know that choosing the right code security tool can make or break development velocity and risk management. Application security is no longer just a security-team concern; it must integrate seamlessly into developer workflows while keeping total cost of ownership, maintenance overhead, and operational effort under control.
Snyk and Checkmarx are often considered by organizations evaluating code security solutions. While both platforms aim to reduce application risk early in the software development lifecycle (SDLC), they take very different approaches, each with its own strengths and trade-offs.
In this article, we’ll compare Snyk and Checkmarx side by side, highlighting where each excels, where limitations appear, and how their capabilities overlap, helping you determine which tool best aligns with your team’s security and development needs.
TL;DR
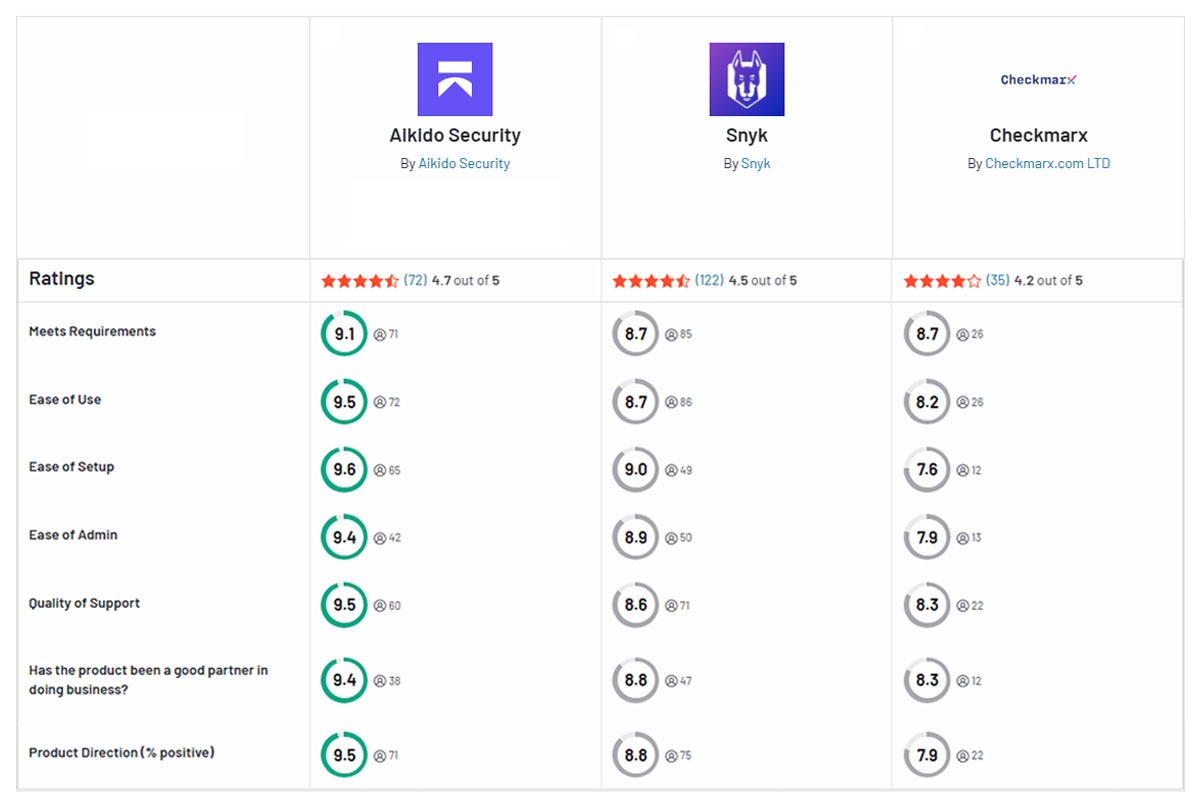
Aikido Security combines the strengths teams often associate with Snyk’s Software Composition Analysis (SCA) and Checkmarx’s depth in Static Application Security Testing (SAST), while delivering a more accurate, developer-first security experience with significantly less noise.
Compared to Snyk’s SCA, Aikido Security goes beyond traditional CVE-based dependency scanning. It combines vulnerability detection with Aikido Intel, which identifies silently patched vulnerabilities and issues without CVEs, alongside malicious package detection, license analysis, and reachability-based prioritization. This allows teams to reduce systemic dependency risk instead of reacting to long lists of individual alerts.
Compared to Checkmarx, Aikido Security focuses on reducing noise and improving developer actionability. It uses its own trained LLM models to reduce false positives by over 85% and supports custom rules tailored to a team’s specific codebase. Findings are enriched with code quality signals and risk scoring, while developers receive in-IDE alerts with AI-generated remediation guidance. After scanning a large HRtech platform’s code, issues flagged showed 99% fewer critical false positives compared to Checkmarx, this was because EPSS and AI-based prioritizations were used to help identify and reduce noise.
Beyond individual scanners, Aikido Security offers broader coverage with simpler and more transparent pricing. Teams can start with any module, including Aikido Code (SAST, Code Quality, IaC Scanning, Malware Detection), Aikido Cloud (CSPM, CNAPP), Aikido Defend (RASP) and Aikido Attack (AI Penetration Testing, DAST), and expand as their needs grow.
As a result, both startups and enterprises consistently rate Aikido Security higher in pilot evaluations, citing its developer-friendly workflows, low-noise scanning, comprehensive coverage across the software lifecycle, AI-driven risk prioritization, and predictable pricing.
Quick Feature Comparison: Snyk vs Checkmarx vs Aikido Security
What is Snyk?
Snyk is an application security platform designed to integrate directly into development workflows. It originally focused on Software Composition Analysis (SCA) for identifying vulnerabilities in open-source dependencies, and later expanded into proprietary code scanning (SAST), container image scanning, and infrastructure-as-code (IaC).
Snyk emphasizes fast feedback through IDEs and CI/CD pipelines to help teams catch and fix issues early in the development lifecycle.
Pros:
- Integrates with popular IDEs, Git repositories, and CI/CD pipelines
- Provides in-context vulnerability alerts with remediation guidance
- Intuitive user interface for getting started quickly
- Strong open-source vulnerability database and ecosystem coverage
Cons:
- High alert volume; users often report needing significant tuning to manage false positives
- Advanced policy management, reporting, and full AppSec coverage require enterprise plans and add-ons
- Per-developer pricing can become expensive as teams and repositories scale
- Security workflows (Jira, policies, issue management) often require manual configuration
- Users report fix suggestions can be generic for complex or non-standard codebases
- Some teams report limitations when scanning large or highly specialized proprietary code
What is Checkmarx?
Checkmarx is an enterprise application security (AppSec) platform that started with Static Application Security Testing (SAST) for custom code and broadened its platform to cover open-source libraries, cloud infrastructure, and supply chain security. Its roots in static code analysis give it a reputation for deep code inspection and governance.
Pros:
- Deep static analysis capabilities for large and complex codebases
- Strong policy enforcement and governance controls
- Built-in secure coding training to support developer education
- Well-suited for compliance-driven security programs
Cons:
- Primarily designed for large enterprises, with workflows centered around security teams rather than developers
- Scans can be slow and resource-intensive, especially for large projects, with limited visibility into scan bottlenecks
- High volume of findings often requires significant manual triage by security teams
- Limited issue grouping and prioritization, which can lead to visual clutter and developer friction
- Reporting is often minimal out of the box, with team- and executive-level views typically requiring custom exports
- Third-party integrations can require additional setup and maintenance
- Cloud offering (Checkmarx One) is still maturing compared to the on-premise platform
- Pricing is modular, with separate contracts for different security capabilities
Feature-by-Feature Comparison
Security Scanning Capabilities
Both Snyk and Checkmarx offer multiple types of security scans, but their strengths differ.
- Snyk: Snyk made its name in open-source vulnerability scanning by quickly identifying known CVEs in third-party libraries and monitoring container image risks. It also performs static analysis via Snyk Code, as well as checks for infrastructure-as-code misconfigurations. However, Snyk does not offer full native DAST or runtime protection capabilities.
- Checkmarx: Checkmarx, on the other hand, built its foundation on static analysis (SAST) and is known for its thorough scans. Over time, Checkmarx added its own SCA, container and IaC scanning tools as part of the “Checkmarx One” platform. However, its strongest area remains finding code vulnerabilities with SAST. Checkmarx does not offer native runtime protection.
In summary, Snyk shines at securing the software supply chain (open-source dependencies, containers), whereas Checkmarx primarily focuses on custom code (SAST).
Integration and DevOps Workflow
- Snyk: Snyk is built to integrate directly into developer workflows with minimal friction. It offers plugins for popular IDEs, alerts in source control (pull requests) and CI/CD pipelines. Developers can get security feedback in real time as they code or commit changes.Snyk’s API and integration options are also praised by engineering teams as it makes it easier to connect and start scans with minimal configuration. It is primarily a cloud SaaS service.
- Checkmarx: Checkmarx integration is more heavyweight. It supports CI pipeline hooks and even IDE plugins, but its setup and maintenance are more involved, requiring more expertise and time. Many companies deploy Checkmarx in a centralized way, for example, a security engineer runs scans and shares results,rather than having every developer run it independently. Checkmarx can be run on-premises or as a cloud service, which adds flexibility for enterprises with strict data requirements. However, on-premise deployments also mean you’ll need to manage servers, updates, and scaling yourself adding operational overhead. It is powerful but not as plug-and-play for developers.
In summary, Snyk is generally seen as the more DevOps-friendly tool as it fits into existing developer and cloud workflows with little friction. Checkmarx, on the other hand, can also integrate, but often feels built for security teams first and developers second.
If your goal is to empower engineers to fix issues early, Snyk has the advantage of approachability. If you require an on-premise solution with strict controls, Checkmarx provides that option.
Accuracy and Performance
When it comes to scan accuracy and performance, both tools have trade-offs.
- Checkmarx: Checkmarx has a reputation for very thorough static analysis (it will find subtle issues in code) but historically it has been known to overwhelm developers with findings, some of which may not be critical or are hard to validate. In other words, it can be noisy. Tuning Checkmarx requires writing custom rules or suppressing certain patterns and is often needed to reduce false positives and make results actionable. Checkmarx scans (especially full SAST scans) are known to be slow. It’s not uncommon for Checkmarx to take hours to scan a big project with millions of lines of code, especially if using thorough settings. This slower feedback cycle can frustrate agile teams. If developers have to wait overnight or longer for results, security fixes slow down. x.
- Snyk: On the flip side, Snyk tends to have a better signal-to-noise ratio. Its vulnerability scanning prioritizes actionable results and tries to minimize the volume of alerts common in legacy SAST tools. With many users describing its false-positive rate as “quite manageable”, letting teams focus on real issues. Snyk’s static analysis uses an AI-based engine (from their DeepCode acquisition) that learns from developer feedback to improve accuracy.. However, some developers have still encountered “false flags” with Snyk Code scanning (e.g. flagging safe code as vulnerable).
From a performance point of view, Snyk is generally fast. Its cloud scanners and lightweight plugins can give results in seconds or minutes, thanks to its incremental scans. It also provides near real-time feedback as code is written.
To put it simply,: Snyk is fast and fairly accurate, but might miss some deeper issues; While, Checkmarx offers more scan depth is deep but is noisy and slow, without careful tuning. Teams often use both tools to complement one another, or look for a unified solution that balances depth with developer-friendly UX such as Aikido Security.
Coverage and Scope
Coverage in this case refers to the breadth of programming languages, frameworks, and security issue types each tool supports. Both Snyk and Checkmarx support container and Infrastructure-as-Code (IaC) scanning.
- Checkmarx: Checkmarx positions itself as an enterprise-grade solution with broad language support. It supports 1a broad range of programming languages and frameworks, covering everything from popular languages like Java, Swift, Kotlin, C#, and JavaScript to legacy or niche languages making it suitable for polyglot (mult-language) codebases.. Checkmarx’s SAST can also analyze desktop, web, mobile, and even some low-level code.
In terms of vulnerability detection, Checkmarx’s SAST goes beyond catching common OWASP Top 10 issues like SQL injection and XSS. Its deeper static analysis allows it to identify complex logical flaws and insecure coding patterns, particularly in proprietary or legacy codebases where issues are not always obvious. This depth is one of the reasons Checkmarx is often favored in large, regulated enterprise environments.
Its SCA component similarly covers a wide range of package ecosystems (Maven, NPM, PyPI, NuGet, etc.), and includes an “Exploitable Path” analysis to prioritize reachable security vulnerabilities, which works across major repository platforms and programming languages.
- Snyk: Snyk, while suitable for most modern development needs, supports fewer languages in its SAST tool compared to Checkmarx. As of recent data, Snyk Code supports most common modern programming languages. . Snyk’s strength is in open-source scanning: it has an extensive vulnerability database and monitors open-source projects for new security vulnerabilities , which means teams get alerts for new dependency issues in real time. Snyk Open Source covers all major package managers and has detailed remediation guidance.
Snyk’s SAST focuses on fast, developer-friendly detection of common security issues in modern codebases. While its rule set may not yet be as extensive as Checkmarx’s for complex or legacy code patterns, it effectively covers many common OWASP Top 10 vulnerabilities and continues to improve. Snyk’s strength lies in balancing security coverage with speed and usability, making it well suited for modern CI/CD-driven development teams.
One gap to note is neither Snyk nor Checkmarx offers fully integrated, modern penetration testing or runtime testing as a core strength, so business-logic and runtime-only vulnerabilities may still require additional tools.
For compliance needs, both provide reporting on security posture (e.g. adherence to standards like OWASP, PCI, etc.), but Checkmarx places more emphasis on policy enforcement and compliance alignment, though teams often rely on exports or custom reporting for auditor-ready views.
Overall, Checkmarx covers a broader technology stack (especially if you have legacy apps or a diverse portfolio), while Snyk covers the modern cloud-native stack well (cloud infrastructure, containers, code and dependencies)
Developer Experience
- Snyk: Snyk’s interface is intuitive and geared towards developers rather than security analysts. Setting up a Snyk scan is as easy as a few clicks or commands, and the results are presented with actionable fix advice. For instance, if Snyk finds a vulnerable dependency, it will suggest a specific version to upgrade to; if it finds a code issue, it often provides a code snippet and guidance on how to remediate. Snyk offers automated fix pull requests for some dependency-related issues, though these workflows often require additional configuration at scale.
- Checkmarx: Checkmarx, by contrast, is often seen as a tool for the security team. Its interface and outputs can be overwhelming or overly verbose for developers. Developers have reported needing to sift through lengthy PDF reports or complex dashboards to find the issues they actually need to fix. Without customization, Checkmarx has also been known to flood teams with hundreds of findings labeled with Common Weakness Enumeration Identifier (CWE ID) and internal codes rather than CVE ID’s. As a result, teams sometimes treat Checkmarx as a compliance gate (run it in the background and have security triage the results).
The learning curve for Checkmarx is steep. Developers may need training to use the tool effectively . Additionally, Checkmarx often requires manual tuning (writing custom queries or adjusting rule packs) to fit a team’s coding patterns.
In summary, developers tend to use Snyk because it’s straightforward and reduces friction. Checkmarx, if used without care, can feel like a chore or “security tax” on development teams
Pricing and Maintenance
- Snyk: Snyk uses a subscription-based pricing model with public entry-level plans, though pricing becomes more complex and less predictable at scale. Teams are charged per contributing developer , which can become expensive as you scale up. Many startups start with Snyk’s free or affordable plans, but as they grow, the costs can ramp up significantly.
The upside is that Snyk being a SaaS means zero infrastructure to maintain. You don’t need to provision servers or worry about updating the scanning engine; Snyk handles all that in the cloud.
- Checkmarx: Checkmarx, typically is a larger investment. It’s sold as an enterprise product (with no public pricing, usually custom quotes). Its cost can be justified for large organizations with big security budgets. However, if you’re a smaller company or startup, Checkmarx’s price tag will likely be prohibitive . Moreover, if you choose an on-premise deployment, you’ll incur maintenance costs: hardware or VMs for the scanning engine and database, an administrator to apply updates/patches, and potentially support contracts. Checkmarx does offer a cloud-hosted option (Checkmarx One), which offloads some maintenance.
In terms of maintenance, Snyk clearly wins. It’s mostly hands-off for teams as it is cloud- based. Checkmarx, on the other hand, requires additional time and expertise, from customizing rules to managing false positive workflow and updates.
Bottom line, Snyk is easier to start with and budget (especially with its free tier and SaaS model), whereas Checkmarx is a heavier upfront investment that makes sense if you’re a large enterprise needing more breadth of coverage.
Aikido Security offers a simpler, more transparent pricing model – flat and predictable – and is significantly more affordable at scale than either Snyk or Checkmarx.
To help you compare the features of both tools, the table below summarizes it for you.
Aikido Security: The Better Alternative

Aikido Security is a developer-first application security platform that combines modern SAST and SCA with AI-driven prioritization. It brings together the strengths of Snyk’s dependency scanning (SCA) and Checkmarx’s static code analysis (SAST), while removing much of the noise, operational overhead, and workflow friction associated with both.
Unlike Checkmarx, Aikido consistently delivers far less noise and faster results in real-world environments. In a six-week customer pilot, Aikido produced 99% fewer critical false positives than Checkmarx (3 vs. 306) across SAST and SCA scans. This drastic reduction meant developers spent their time fixing real issues instead of manually triaging findings. Combined with EPSS scoring and AI-based prioritization, Aikido made it easier to understand what actually mattered, while Checkmarx continued to surface large volumes of critical findings that later proved irrelevant. Customers also avoided long scan times and poor visibility into scan bottlenecks, which are common complaints with Checkmarx.
Compared to Snyk, Aikido removes much of the workflow friction that slows teams down. Snyk’s approach of pushing every issue individually into Jira creates noise and requires manual cleanup when issues are resolved. Aikido instead focuses on automatic issue grouping, severity- and SLA-based task creation, and automatic closure, reducing operational overhead and developer frustration. In practice, many issues flagged as “critical” by Snyk were accurately identified as false positives by Aikido and ignored. Combined with AI AutoTriage, AI AutoFixes, and pull-request fix suggestions, teams were able to reduce critical issues by 92% across 548 repositories during the pilot, without building extra automations or workflows.
Aikido also integrates directly into developer workflows across GitHub, GitLab, and Bitbucket, surfacing prioritized findings and fixing suggestions directly in pull requests.
Beyond SAST and SCA, Aikido provides broader coverage through built-in modules for IaC scanning, container security, DAST and API testing, runtime protection, cloud security posture management, secrets detection, and AI-powered penetration testing. This all-in-one approach reduces context switching and lowers total cost of ownership compared to assembling multiple point solutions.
Aikido Security provides even broader security coverage via its modules including IaC scanning, container security, DAST and API security testing, runtime protection, cloud security posture management, secrets detection, and AI-powered penetration testing.
Thanks to its modular architecture, transparent pricing, and developer-centric approach, Aikido offers a practical alternative for teams evaluating Snyk or Checkmarx, and looking for a security solution that excels at both speed and depth.
Want to improve your application security? Start your free trial or book a demo with Aikido Security today.
FAQ
Which tool, Snyk or Checkmarx, is better for vulnerability scanning?
It depends on what you mean by “better” and the environment you’re operating in. Checkmarx is typically chosen by large enterprises that prioritize deep static analysis for complex or legacy proprietary codebases, even if that comes with longer scan times and higher false positive rates. Snyk is better suited for modern development teams that value fast feedback, strong open-source dependency scanning, and tight CI/CD integration.
In practice, many teams struggle with the trade-off between depth and noise. Platforms like Aikido Security aim to remove that trade-off by delivering deep analysis with dramatically fewer false positives and clearer prioritization, making vulnerability scanning more actionable for developers without heavy tuning.
What is static application security testing (SAST), and how do Snyk and Checkmarx implement it?
SAST is a security testing method that analyzes source code without executing it to identify security vulnerabilities such as SQL injection, XSS, and insecure cryptography. Checkmarx uses deep data-flow and control-flow analysis to uncover complex and sometimes non-obvious issues, particularly in proprietary or legacy code. Snyk prioritizes speed and ease of use, scanning code quickly and surfacing common security issues directly in developer tools like IDEs and pull requests.
What features distinguish Snyk from Checkmarx in static application security testing (SAST)?
The main distinction between Snyk and Checkmarx in SAST comes down to how security fits into the development process. Checkmarx is designed for centralized security programs, offering deep analysis, extensive customization, broad language support (including legacy languages), and detailed governance and reporting features. This makes it well suited for compliance-driven environments.
Snyk, by contrast, focuses on developer adoption. It emphasizes fast scans, easy setup, and tight integration into IDEs and CI/CD pipelines so developers can catch issues early without leaving their workflow. Tools like Aikido Security follow a similar developer-first model while adding more context and prioritization to reduce noise and help teams focus on truly exploitable risks.
How do Snyk and Checkmarx differ in vulnerability detection accuracy and false positive rates?
Checkmarx is known for detecting complex vulnerability patterns due to its deep static analysis, but this often results in a high volume of findings, many of which require manual validation or tuning to eliminate false positives. This can slow teams down and create alert fatigue.
Snyk generally produces fewer findings and prioritizes clarity and speed, making results easier for developers to act on. However, its newer SAST capabilities may miss some deeper or highly contextual issues in proprietary code. Real-world evaluations show that newer developer-first platforms like Aikido Security can significantly reduce false positives while maintaining depth, shifting the focus from raw detection volume to actionable security outcomes.
How do Snyk and Checkmarx handle open-source dependency scanning compared to proprietary code scanning?
For open-source dependency scanning (SCA), Snyk is generally stronger. It offers real-time vulnerability monitoring, a large CVE database, and clear remediation guidance such as recommended upgrade paths, making it easy for developers to address dependency risks quickly. Checkmarx also supports SCA across major ecosystems, but it is often treated as a complement to its core SAST capabilities rather than its primary strength.
For proprietary code scanning, Checkmarx’s SAST typically provides deeper analysis, especially for large or legacy codebases, while Snyk focuses on faster, more accessible scans for modern applications. Developer-centric platforms like Aikido Security aim to balance both by combining deep analysis with lower noise and clearer prioritization.
You Might Also Like:




