Get a pentest done, today.
Autonomous AI agents that outperform humans at machine speed. Get a full audit-grade SOC2 or ISO27001 PDF report in hours, not weeks.

.png)
.jpeg)















Aikido Attack: The future of pentesting
Automated penetration testing that matches human creativity with machine speed. Detect, exploit, and validate vulnerabilities across your entire attack surface, on demand.
How our Pentests work
.jpg)
Maps your attack surface first
Aikido inventories what can be attacked using code and OpenAPI specs in whitebox mode, or probing the live app in blackbox mode.
.jpg)
Parallel agents test real attack paths
Hundreds of agents focus on specific vectors and try to break expected behavior, more like a red team than a checklist scan.


"Aikido’s pentest delivered human level, comprehensive findings at lightning speed and passed a rigorous compliance review with no issues."
Dan SherwoodManaging Director at Khaos Control Solutions
Generate the right report for every audience.
Our engine automates security analysis using the same methodologies trusted by professional pentesters.
Generate the right report for every audience.
High-level management report: key findings and overall risk posture for execs
Post-remediation report: resolved issues and remaining risk, built for stakeholder communication
Simplified customer report: proves security posture without exposing sensitive stack details
Detailed auditor report: every finding, technical detail, and remediation guidance for SOC2 / ISO27001
.png)
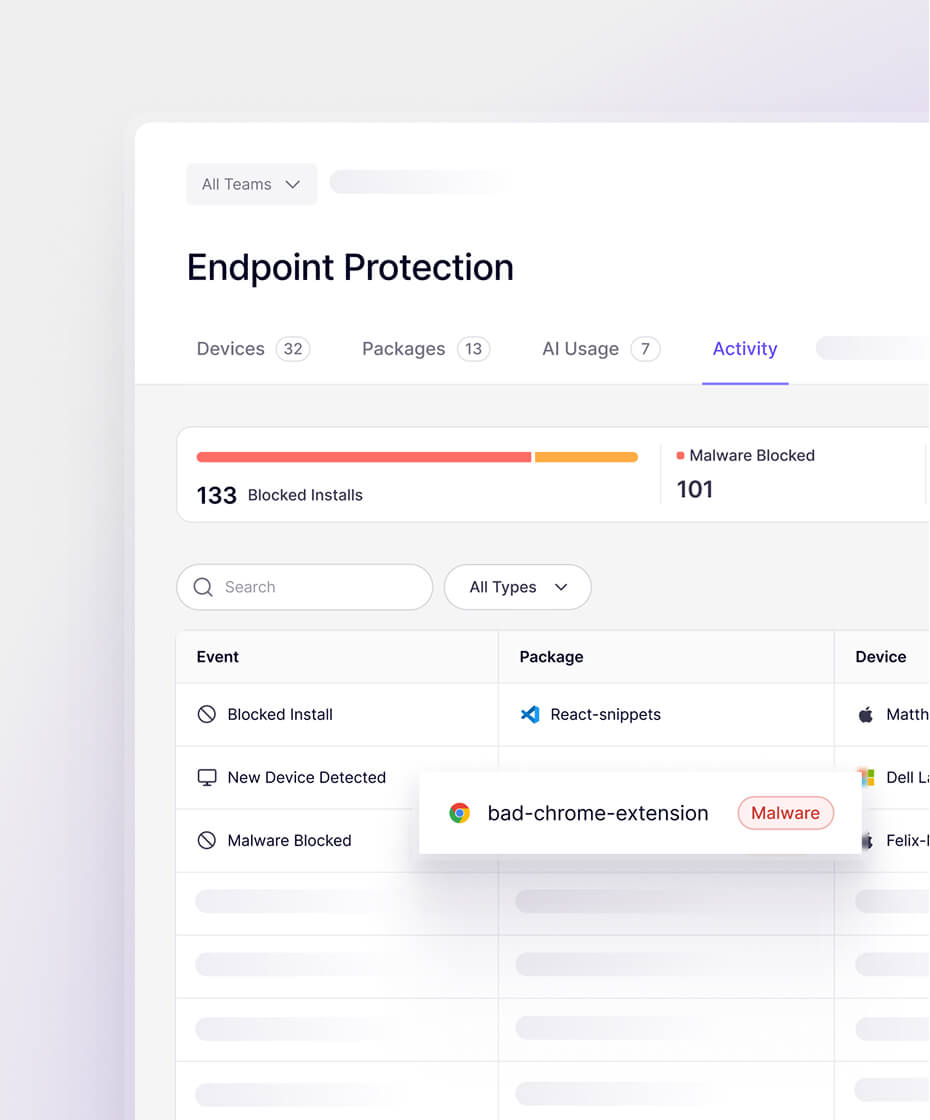
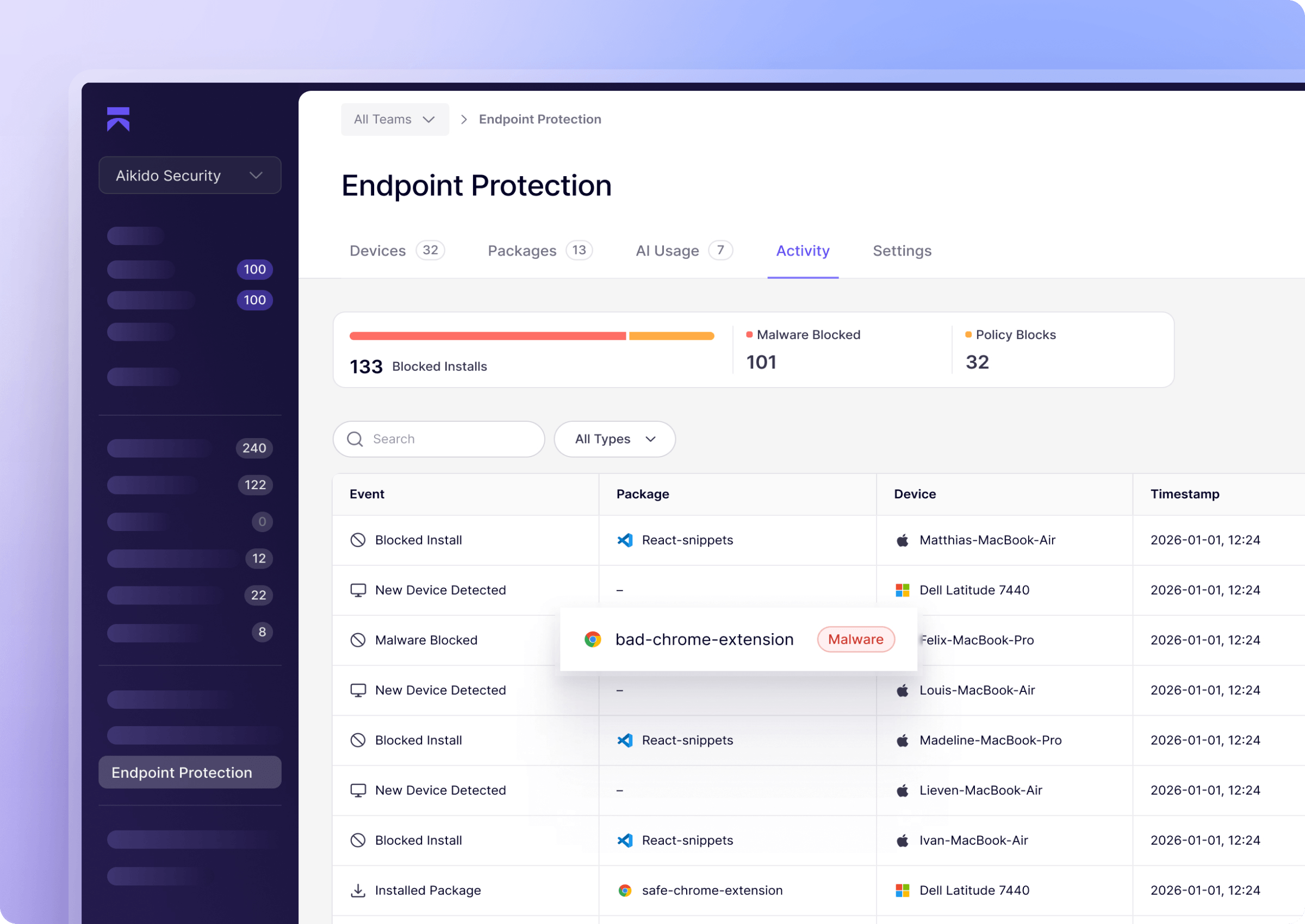
Features
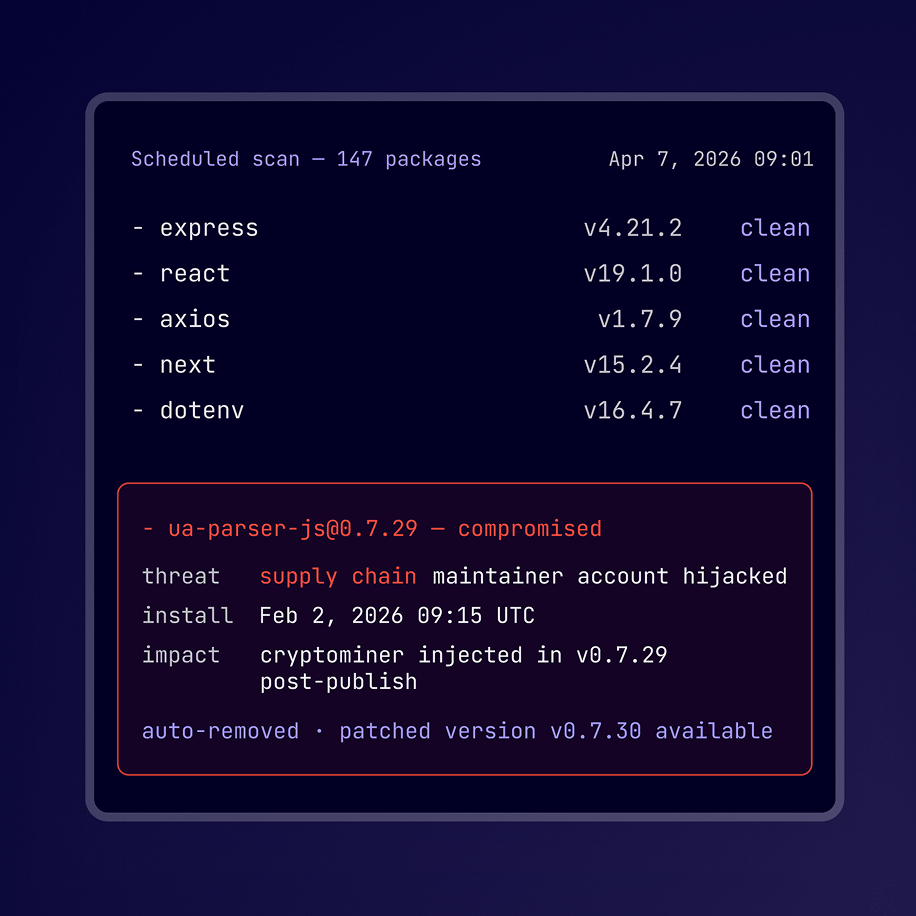
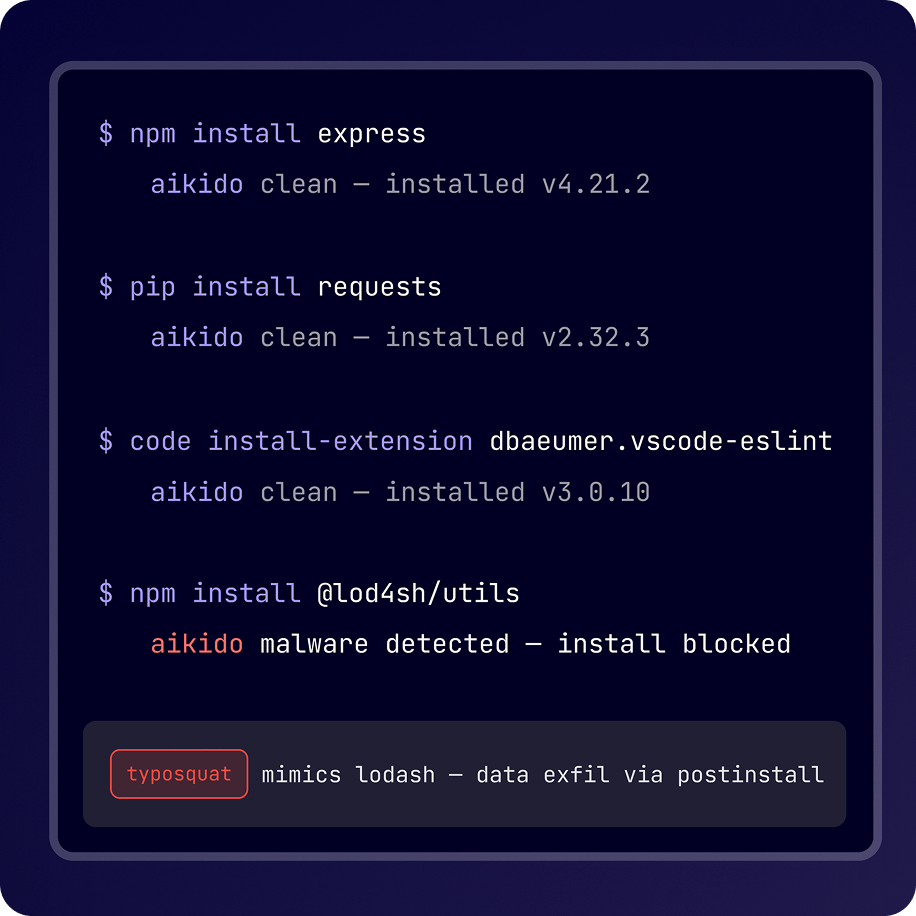
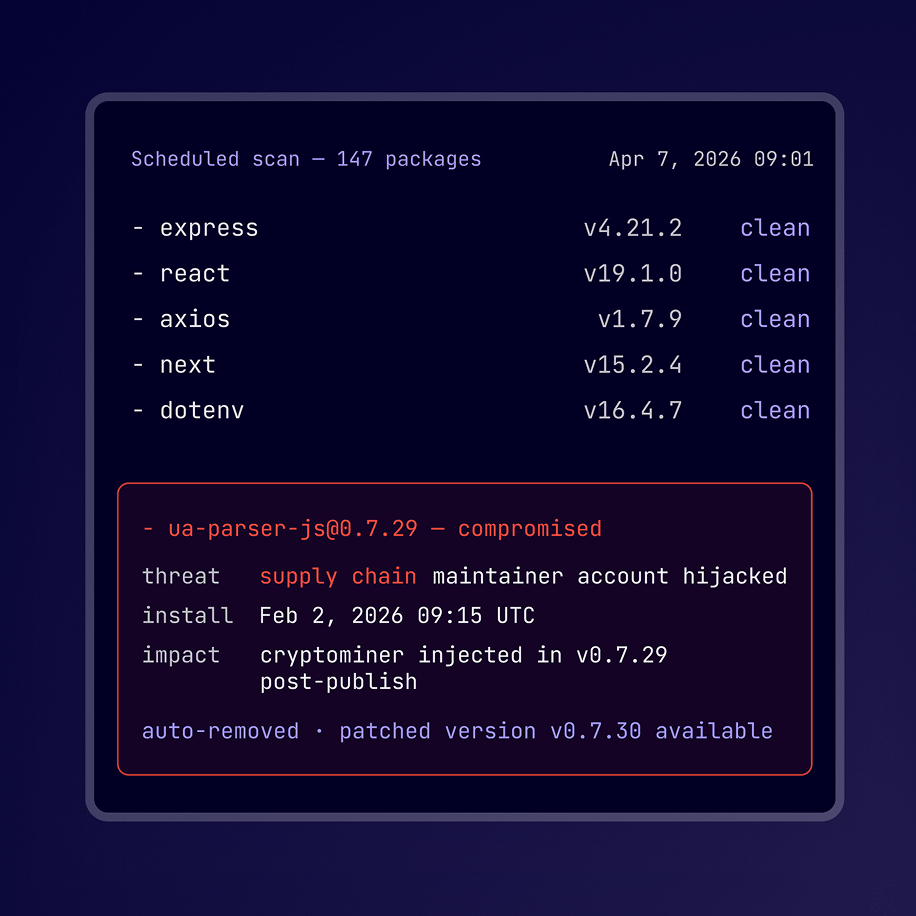
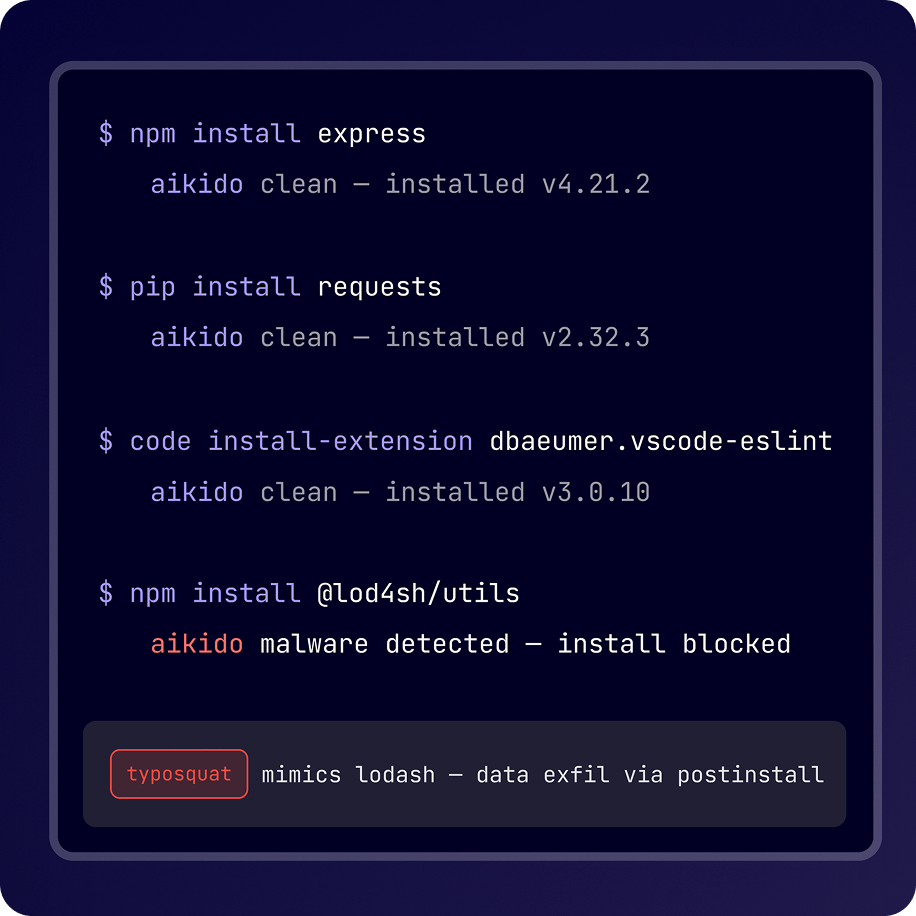
Pentest every feature release. Patch automatically.
Continuous offensive testing with built-in remediation. Every release tested, every finding fixed.
.png)
Pentest Escalate
Top-tier pentest, flat-rate price.
Full PDF Report usable for SOC2 and ISO27001 compliance.
Focused multi-day manual penetration test



Full PDF Report usable for SOC2 and ISO27001 compliance.
Provides the depth of a 2 week manual penetration test
Guaranteed auditor-accepted reports.
Free re-testing of findings for 90 days.
Full PDF Report usable for SOC2 and ISO27001 compliance.
Provides the depth of a 4 week manual penetration test

Guaranteed auditor-accepted reports.
Free re-testing of findings for 90 days.
Continuous offensive security that scales with your organization
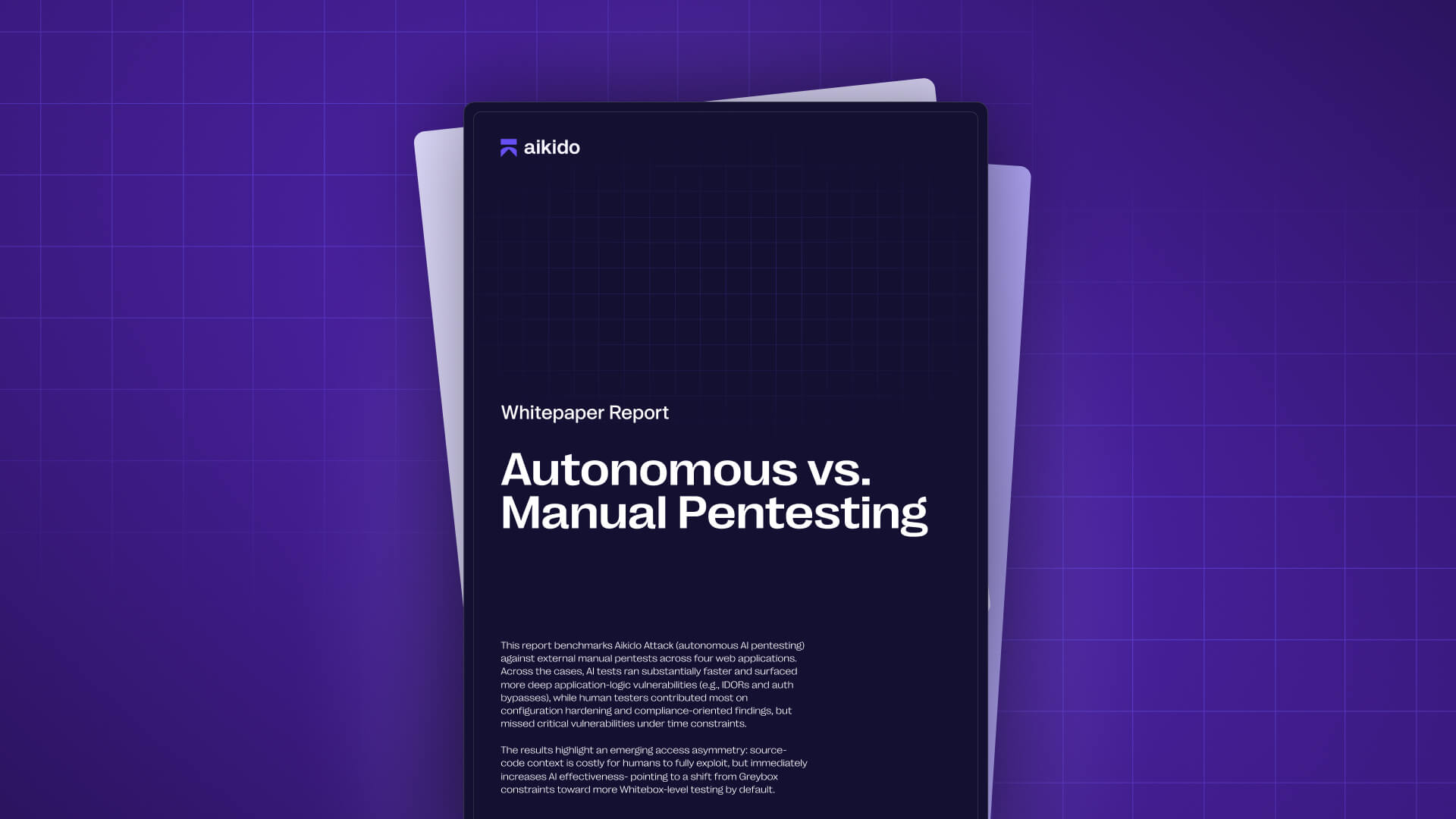
AI Pentesting vs. Humans: The Benchmark
AI pentesting sounds like hype - until you test it properly. This report compares autonomous AI pentesting with external manual pentests on 4 real web apps, including the exact vulnerability categories each method found (and missed).
.png)
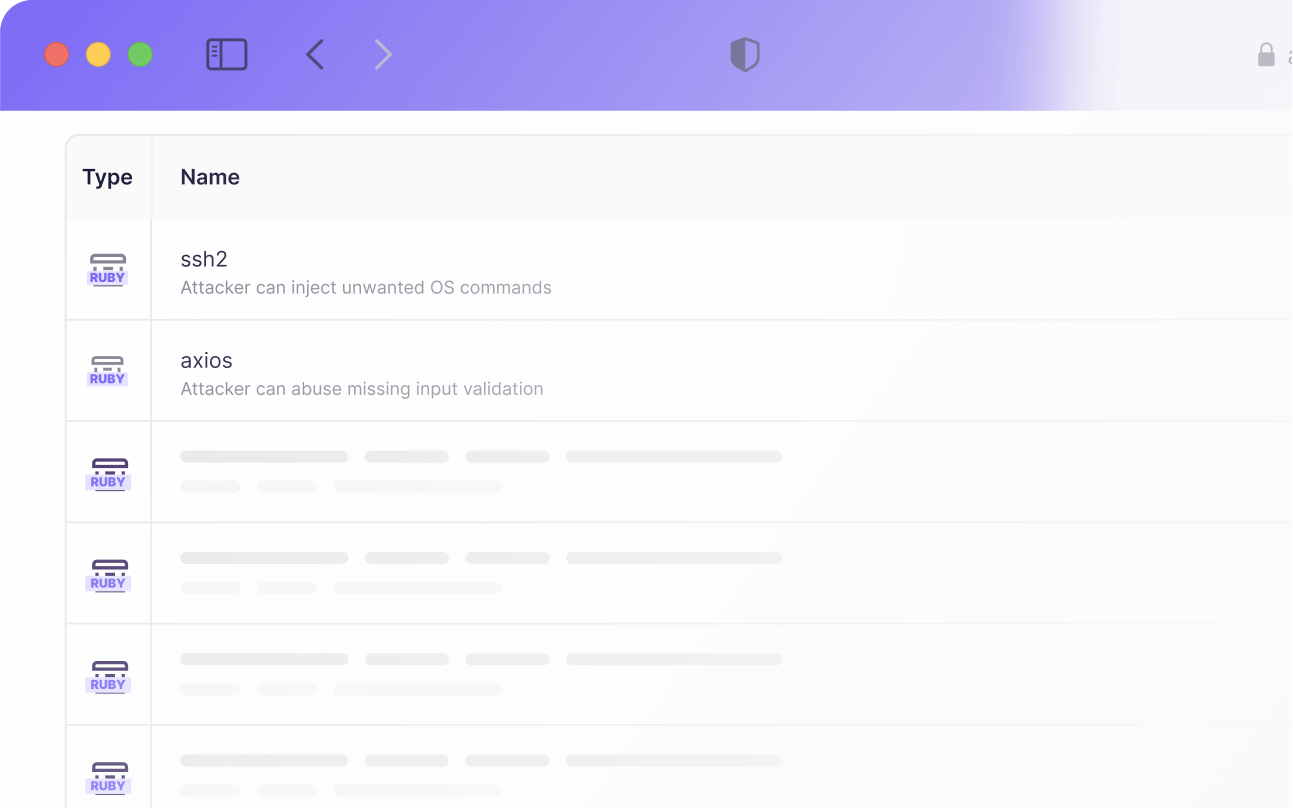
How it Works
.png)
When the pentest begins, features and endpoints of the applications are mapped.


100’s of agents are dispatched on those features and endpoints, each going in-depth, focused on their attack vector.


For each finding, additional validation is performed to avoid false-positives and hallucinations.
Frequently Asked Questions

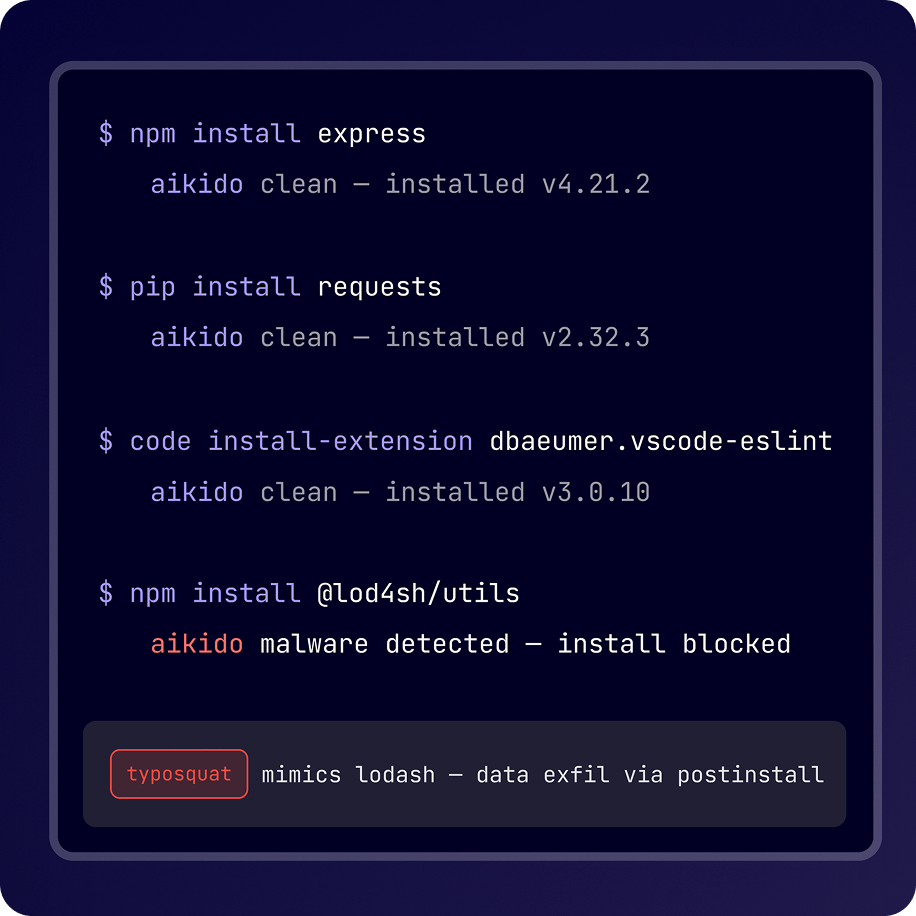
AI Pentesting simulates real-world attacks on your app or API using AI models trained on thousands of real exploits. It finds and validates vulnerabilities automatically - no waiting for a human pentester to start.

Traditional pentests take weeks to schedule and deliver. AI Pentesting runs instantly, scales to your full environment, and gives reproducible, detailed results in minutes.

Usually within minutes. Connect your target, define scope, and the system starts testing immediately - no coordination, no back-and-forth. Almost 100% of AI pentest find actual vulnerabilities.

Yes. Every run produces an audit-ready penetration test report with validated findings, proof-of-exploit details, and remediation guidance, structured to meet SOC 2 and ISO 27001 requirements.

Because Aikido already understands your code and environment, AutoFix generates targeted code changes for confirmed vulnerabilities. Once applied, the issue can be immediately retested to verify that it is fully resolved.

No, but providing code access significantly improves results. When repositories are connected, agents understand application logic, roles, and data flows, which leads to deeper coverage and more accurate findings.

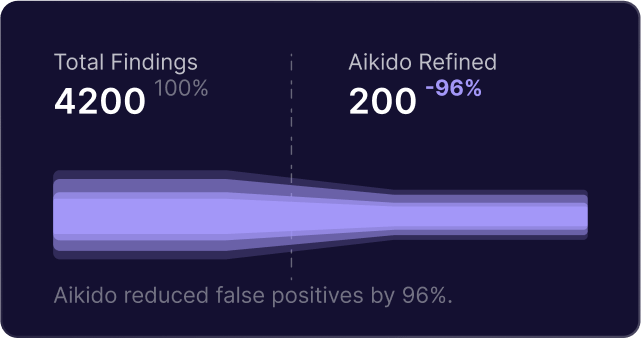
Findings are only reported after they are successfully exploited and confirmed against the live target. If an attack attempt cannot be validated, it is discarded and never shown in the results.

AI Pentesting covers everything expected from a penetration test, including injection flaws, access control issues, authentication weaknesses, and unsafe API behavior.
It also detects business logic and authorization issues such as IDOR and cross-tenant access by reasoning about how the application is supposed to behave.

You define which domains can be attacked and which are only reachable. All traffic is enforced through strict guardrails, with pre-flight checks before the run and a panic button that stops all agents instantly.

For web applications, AI Pentesting delivers coverage comparable to a traditional human-led pentest, with results available in hours instead of weeks.
In side-by-side evaluations, autonomous agents have matched and in some cases exceeded human coverage by exploring more paths consistently. Human testers remain valuable for non-web targets and highly contextual edge cases.

No. Start the pentest with “Skip payment.” When it’s done, you’ll see the results summary. High/critical issues and the full report unlock only if you decide to pay. No upfront cost. No risk to try.
First scan results in under 2 minutes
Connect your repo and see only the vulnerabilities that are actually reachable.

“Aikido’s automation and accuracy help our teams focus on building, not babysitting vulnerabilities.”


















.png)




.png)
.png)

.svg)
.png)