Full visibility into your software supply chain and AI tools.
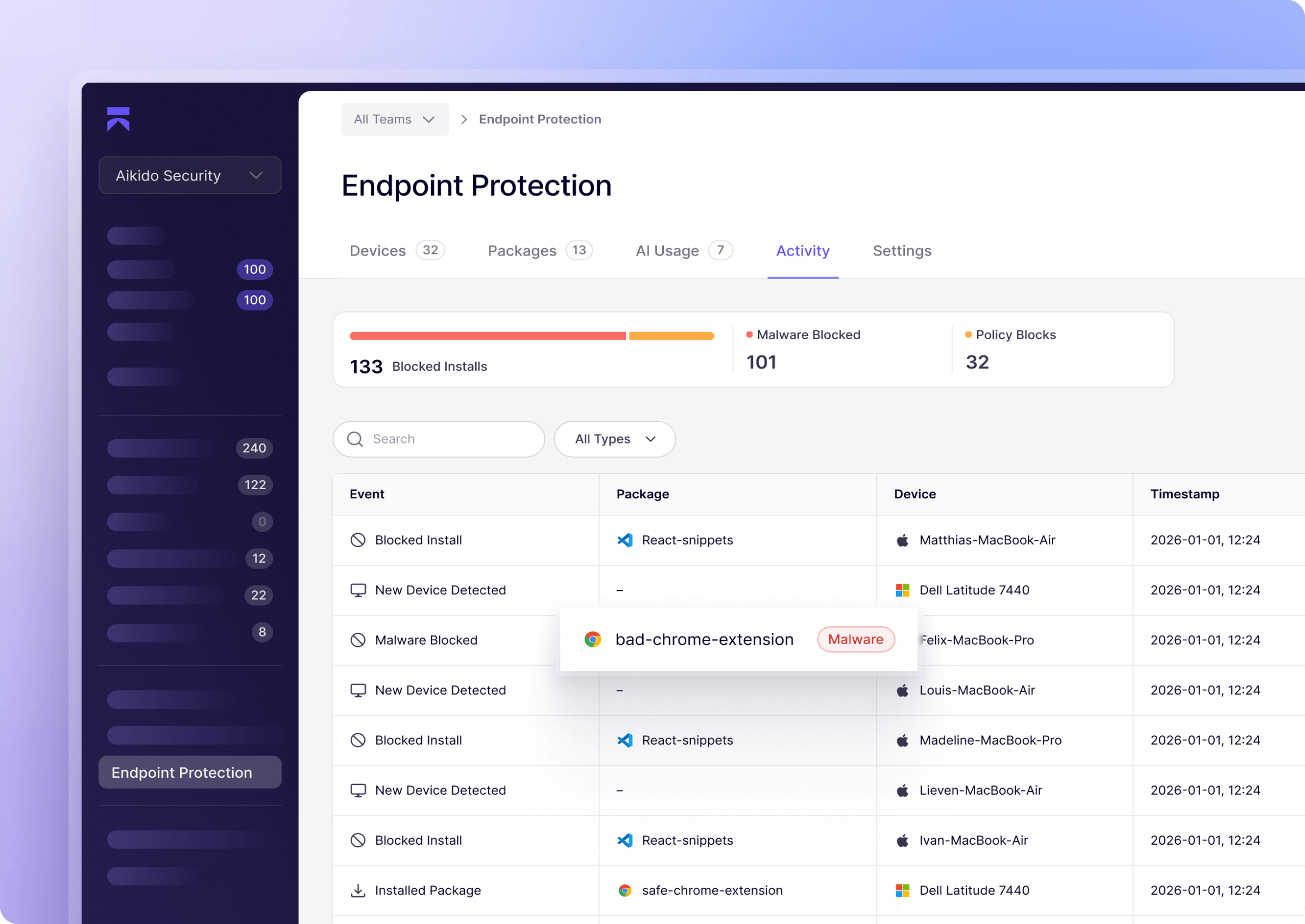
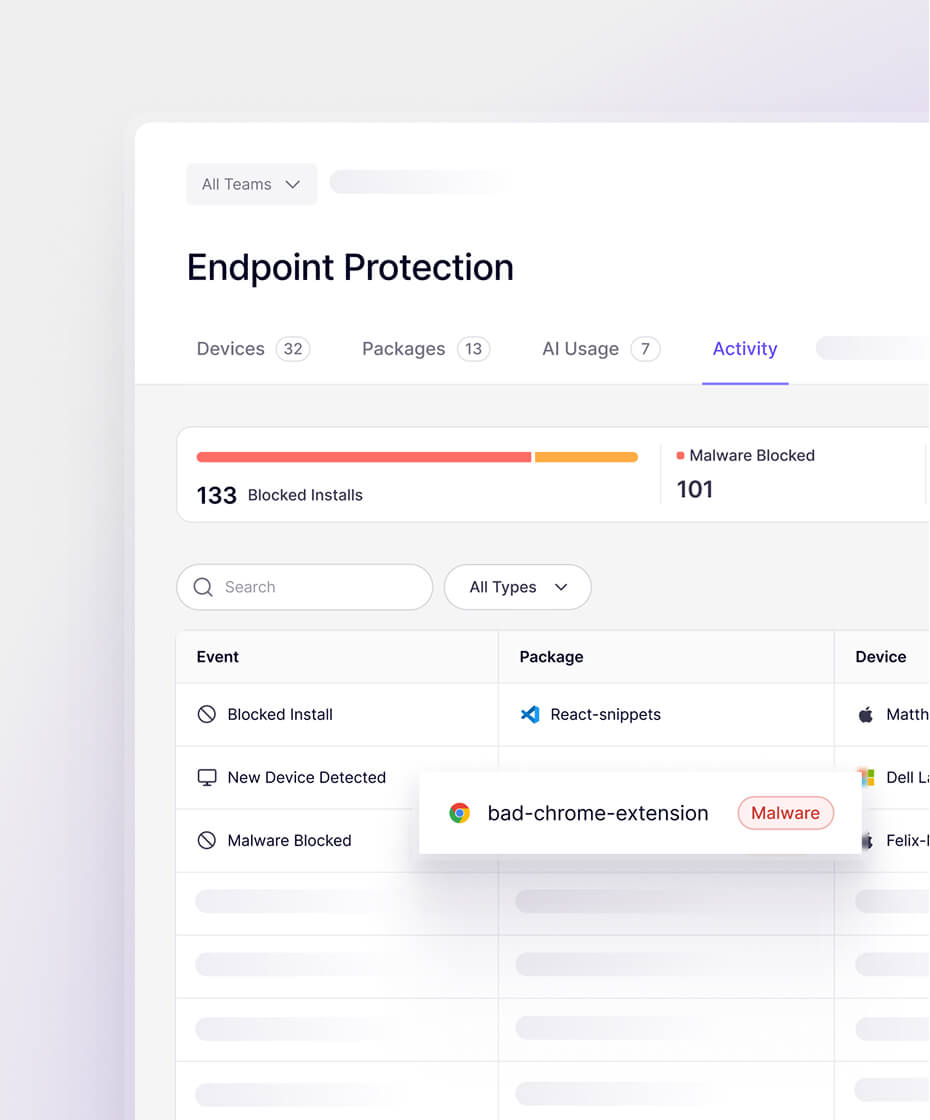
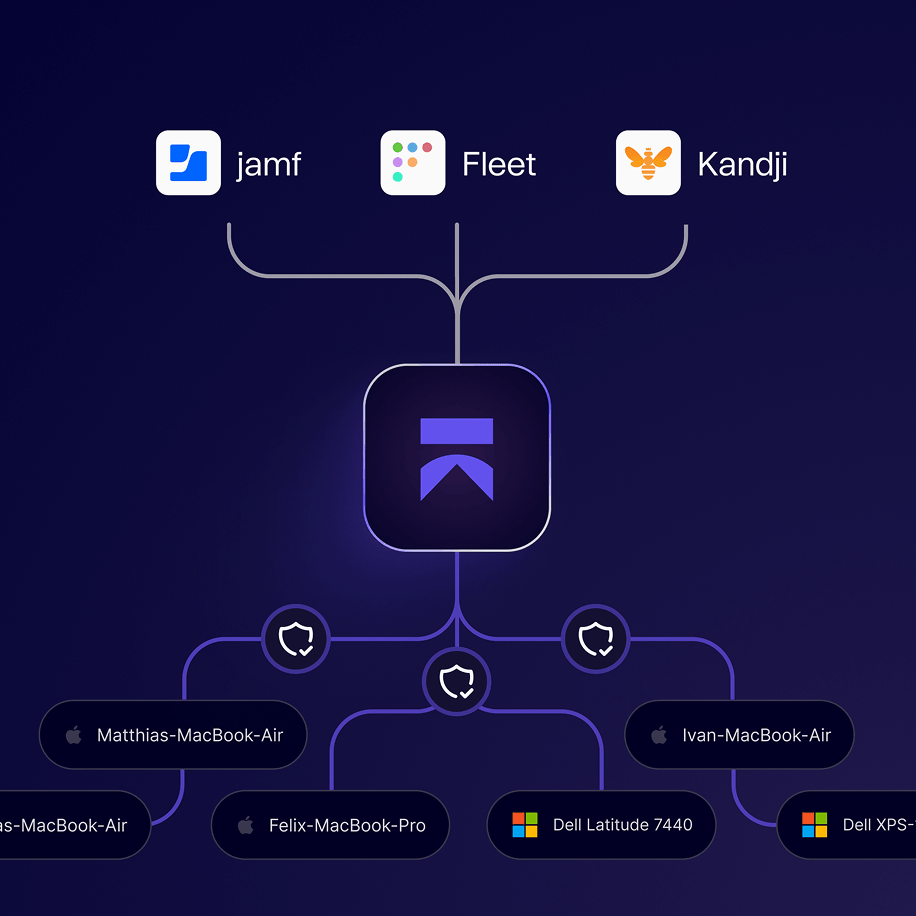
A security agent for developer workstations. Blocks malware at install.
Governs AI tooling. Manages packages and extensions.
Runs without getting in the way.
.png)
.jpeg)















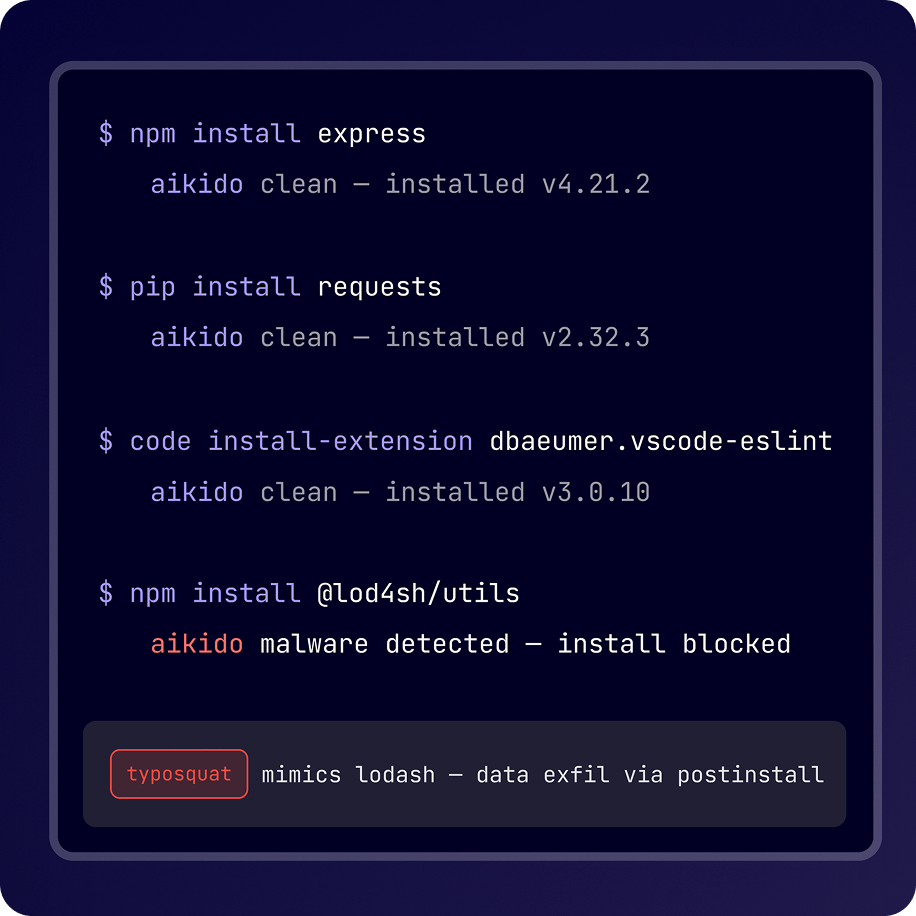
Works with every install source and AI tool your developers use
Package Registries
IDE & Browser Extensions
AI Tools & Models
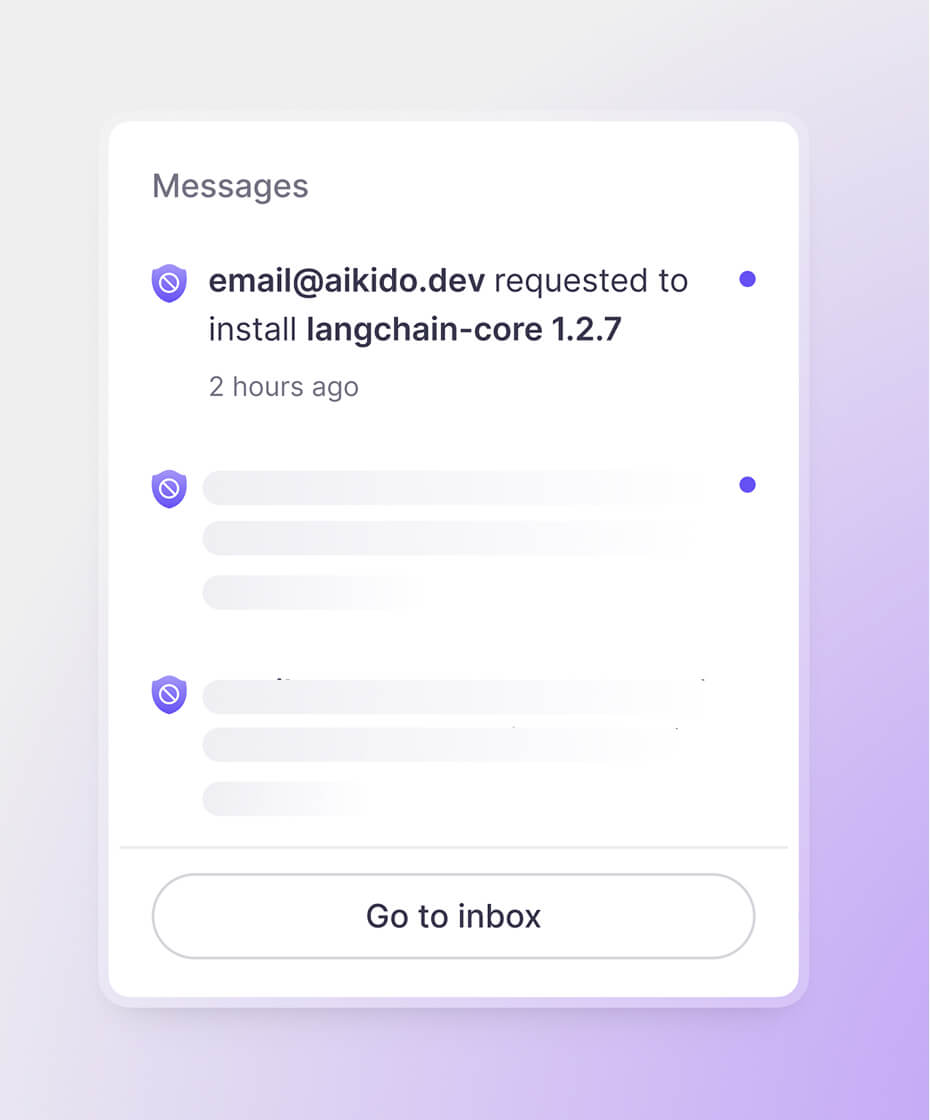
Aikido Endpoint runs in the background, blocking threats before they land.
Detects
Which AI tools, package installs, and extension downloads, pass through Aikido's agent. You see exactly what's running on every developer workstation before it becomes a problem.
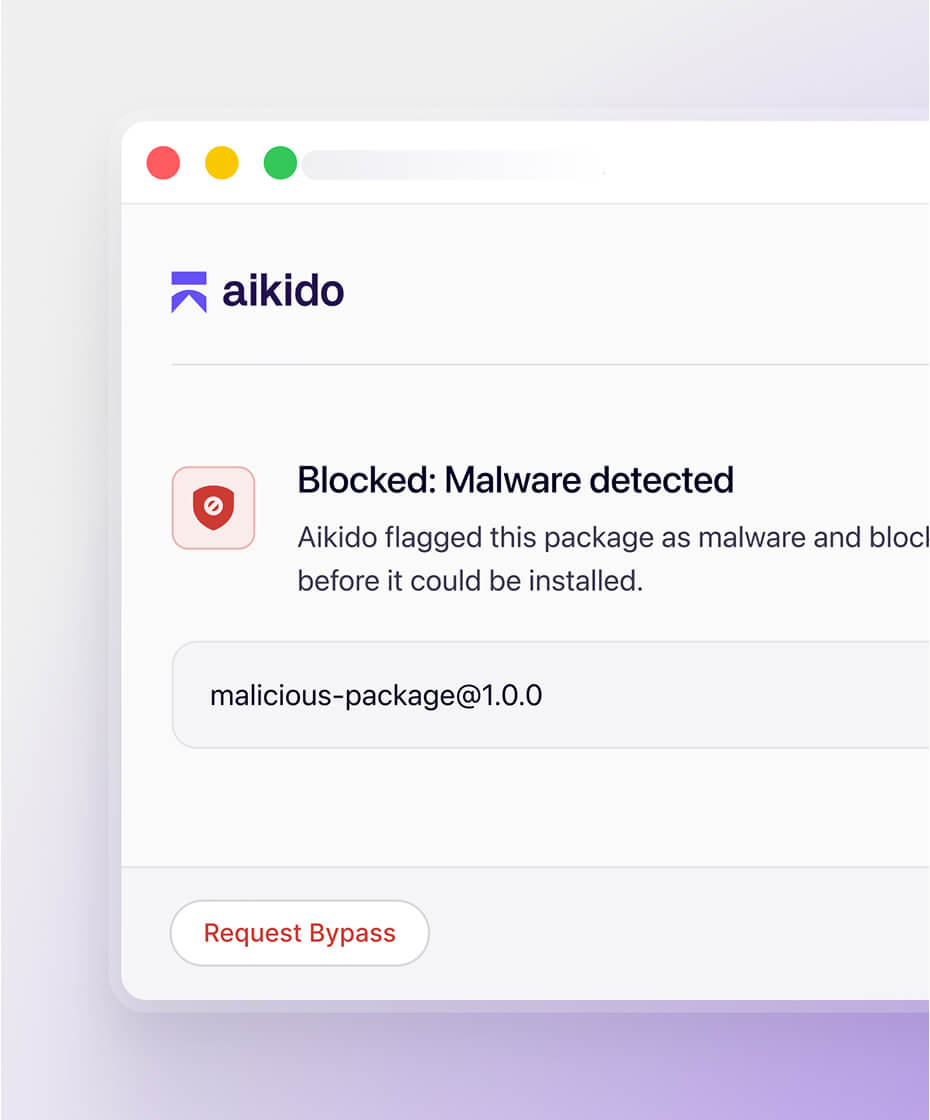
Prevents
Known malware is blocked before it touches the filesystem. Not flagged after. Not quarantined later. Stopped before it's downloaded.
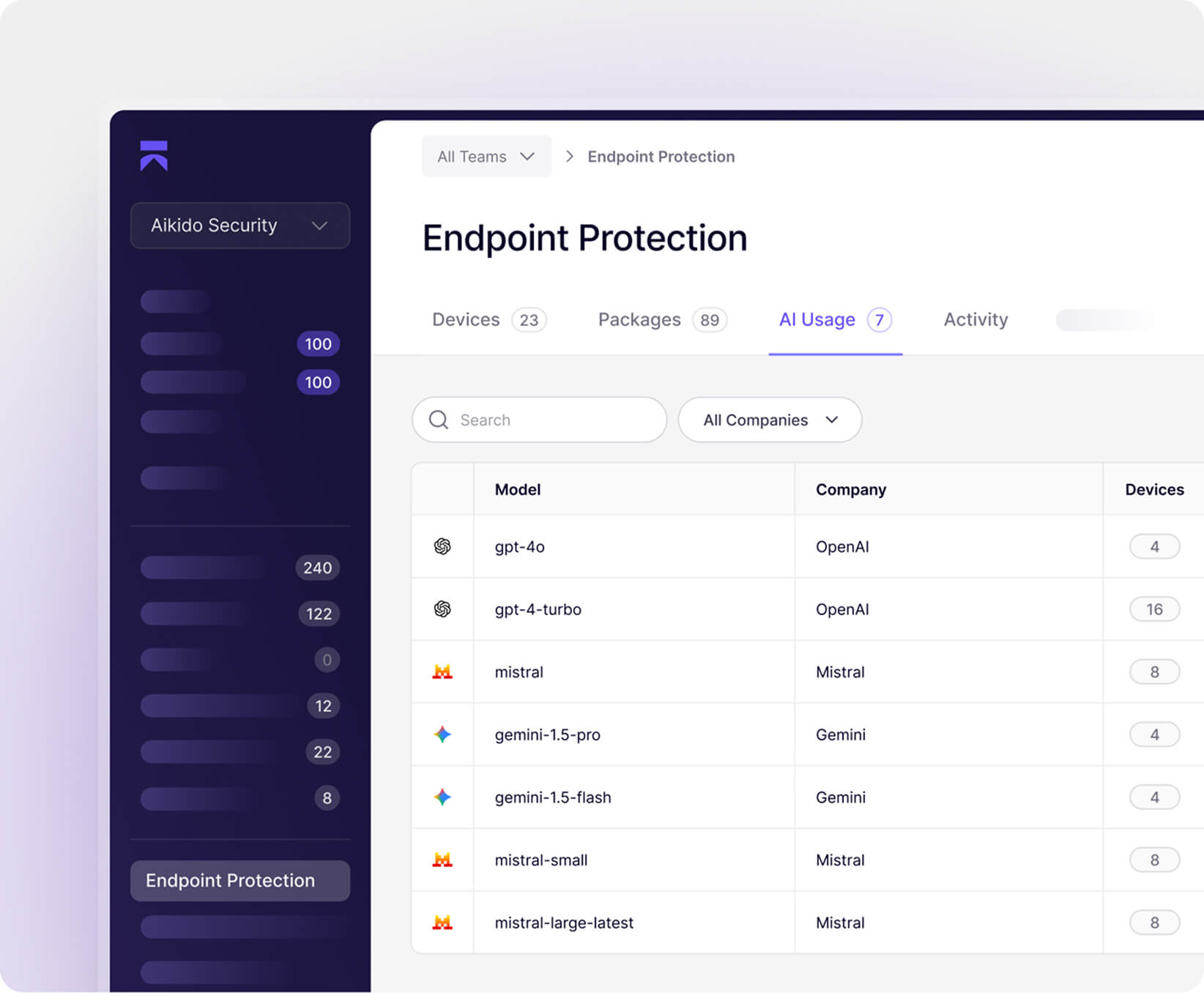
Developers are using AI tools your security team has never reviewed
Get up and running in a few minutes
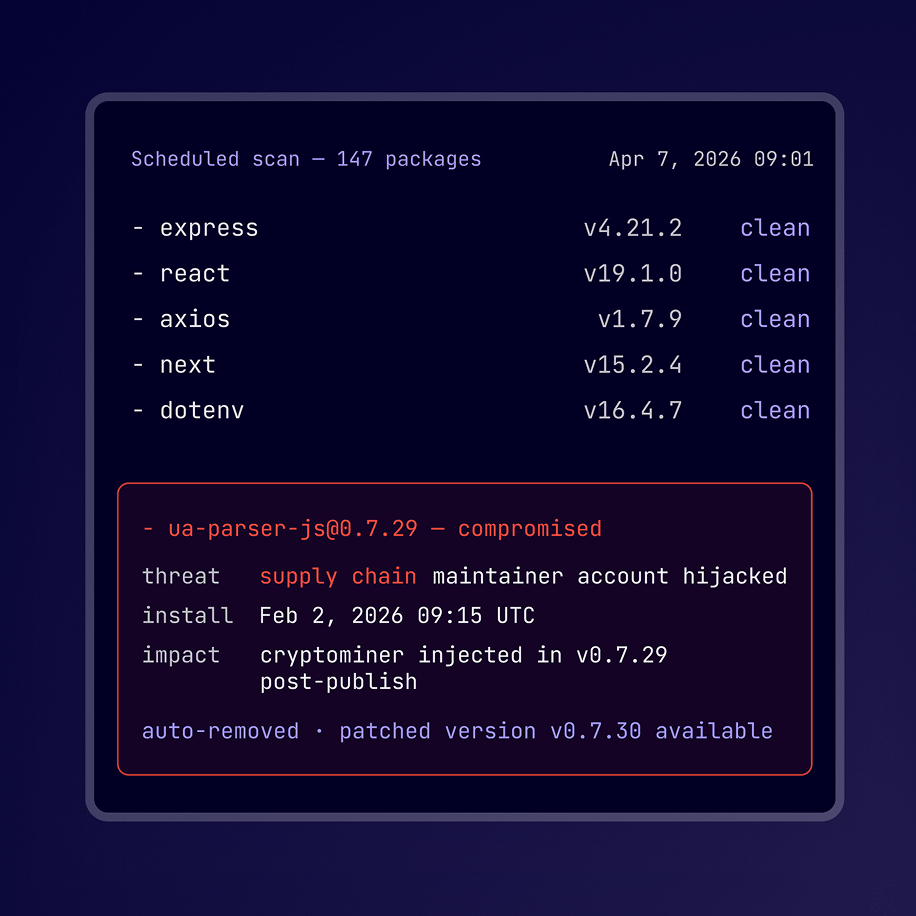
What's hitting npm right now
Supply chain attacks are escalating fast: Trivy, Cannisterworm, LiteLLM, and Axios, all got hit recently.
Malicious packages are slipping into npm and PyPI, executing on install before teams know something's wrong.
Aikido Intel continuously detects malicious packages across npm, PyPI, and more. Every detection is automatically pushed to the block list on connected workstations, before any developer can install it.
.png)
Your developers install thousands of packages a year.. Secure them today.
Most security tools ask developers to slow down.
Aikido just makes sure nothing dangerous gets through.

“Aikido’s automation and accuracy help our teams focus on building, not babysitting vulnerabilities.”















Frequently Asked Questions

It's a real pentest, not a scan. Aikido deploys AI agents against your live, running application, the same one your users access. They probe login flows, try to access data they shouldn't be able to reach, and attempt to chain smaller weaknesses into bigger breaches. You get findings with full reproduction steps, not just a list of potential issues. Lovable's built-in scanner reviews your code before you publish. Aikido attacks what's actually running after you do.

Quite a lot! Most vulnerabilities in Lovable apps aren't in the code itself. They're in how the application behaves at runtime. Can a logged-in user access another user's data by changing a parameter? Does your API enforce the same rules your UI does? Are your authentication flows as airtight as they look? The pentest tests the running application, not the source code, which is exactly why it catches things a code review misses.

The agents interact with your app the way any user would, through its front end and APIs. One thing worth knowing: because the agents actively probe your app, they may create test data in the process (submitted forms, created accounts, and so on). They don't access your database directly. Findings are stored in your Aikido account and visible only to you.

They cover different moments and different threat models. Lovable's scanner reviews your code before you publish. It catches exposed secrets, misconfigured database policies, and known vulnerability patterns at the source level. Aikido tests your live application after it's running, probing how it actually behaves under attack, not just how it looks on paper. You need both. Code that looks clean can still have logic flaws that only show up when someone tries to break in.

No. Each finding comes with a plain-language explanation of what was found, why it matters, and the exact steps to reproduce it. When you're ready to fix, click Fix all in Lovable and their agent patches the vulnerabilities for you, without leaving your project.